service作用体现在两个方面
1、集群内部 不断跟踪pod的变化,更新endpoint中的pod对象,基于pod的IP地址不断变化的一种服务发现机制
2、集群外部 类似负载均衡器,把流量ip+端口,不涉及转发url(http,https),把请求转发到pod
nodePort:容器端口----service端口----nodePort,设定了nodePort,每个节点都会有一个端口被打开,30000-32767
IP+端口 节点ip+30000+32767,实现负载均衡
loadbalancer 云平台上的一种service服务,云平台提供负载均衡ip地址
extrenal 域名映射
ingress 基于域名进行映射,把url(http https)请求转发到service,再由service请求转发到每一个pod
ingress只要一个或者是少量的公网ip或者LB,可以把多个http请求暴漏到外网,七层反向代理
service的service,是一组域名和URL路径,把一个或者多个请求转发到service的规则
先是七层代理----四层代理----podingress service nginxingress的组成
ingress是一个api的对象,通过yaml文件来进行配置,ingress的作用是定义请求如何转发到service的规则,配置模版
ingress通过http和https暴漏集群内部service,给service提供一个外部的url,负载均衡,ssl/tls(https)的能力,实现一个基于域名的负载均衡
ingress如何实现
ingress-controller:具体的实现反向代理和负载均衡的程序,对ingress定义的规则进行解析,根据ingress的配置进行请求的转发
ingress-controller不是k8s自带的组件功能,ingress-controller一个统称
nginx ingress controller
traefik都是ingress-controller 都是开源的
ingress资源的定义项
1、定义外部流量的路由规则
2、定义服务的暴漏方式,主机名,访问路径和其他的选项
3、负载均衡(ingress-controller)
ingress-controller的运行方式是pod方式运行集群当中
nginx-ingress-controller
wget https://gitee.com/mirrors/ingress-nginx/raw/nginx-0.30.0/deploy/static/mandatory.yamlingress暴漏服务方式
1、deployment+LoadBalancer模式,ingress部署在公有云,会ingress配置文件里面有type,type:LoadBalancer,公有云平台会为个LoadBalancer的service创建一个负载均衡器,绑定一个公网地址,通过域名指向这个公网地址就可以实现集群对外暴漏
2、方式二:Daemonset+hostnetwork+nodeSelector
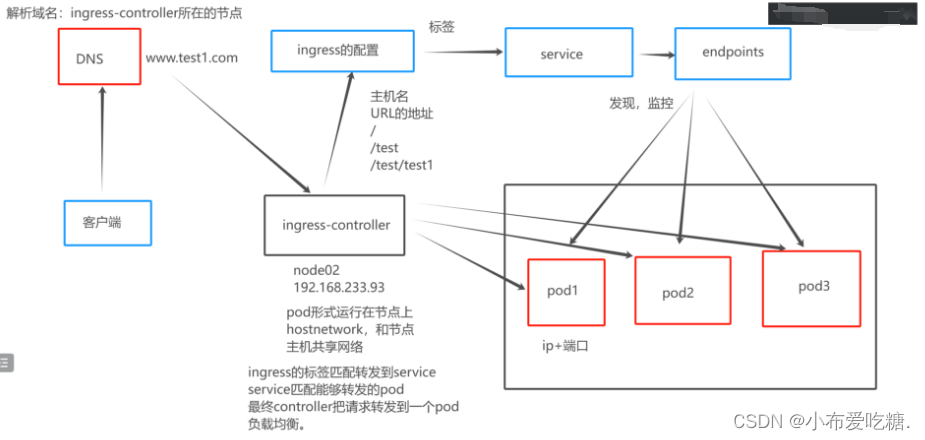
Daemonsetset 在每个节点都会创建一个pod
hostnetwork pod共享节点主机的网络命名空间,容器内直接使用节点主机的ip+端口,pod中的容器可以直接访问主机上的网络资源
nodeSelecor 根据标签选择部署的节点,nginx-ingress-controller部署的节点
缺点:直接利用节点主机的网络和端口,一个node只能部署一个ingress-controller pod比较适合大并发的生产环境,性能最好的Daemonset+hostnetwork+nodeSelector实现
修改生成的配置文件mandatory.yaml.............apiVersion: apps/v1
kind: DaemonSet
metadata:name: nginx-ingress-controllernamespace: ingress-nginxlabels:app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/part-of: ingress-nginx
spec:#replicas: 1selector:matchLabels:app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/part-of: ingress-nginxtemplate:metadata:labels:app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/part-of: ingress-nginxannotations:prometheus.io/port: "10254"prometheus.io/scrape: "true"spec:# wait up to five minutes for the drain of connectionsterminationGracePeriodSeconds: 300serviceAccountName: nginx-ingress-serviceaccounthostNetwork: truenodeSelector:test1: "true"# kubernetes.io/os: linuxcontainers:- name: nginx-ingress-controllerimage: quay.io/kubernetes-ingress-controller/nginx-ingress-controller:0.30.0args:- /nginx-ingress-controller- --configmap=$(POD_NAMESPACE)/nginx-configuration
.............把镜像(拖到opt)上传
tar -xf ingree.contro-0.30.0.tar.gz
docker load -i ingree.contro-0.30.0.tar.gz service 的yaml文件
apiVersion: v1
kind: PersistentVolumeClaim
metadata:name: nfs-pvc
spec:accessModes:- ReadWriteManystorageClassName: nfs-client-storageclassresources:requests:storage: 2Gi
---
apiVersion: apps/v1
kind: Deployment
metadata:name: nginx-applabels:app: nginx
spec:replicas: 3selector:matchLabels:app: nginxtemplate:metadata:labels:app: nginxspec:containers:- name: nginximage: nginx:1.22volumeMounts:- name: nfs-pvcmountPath: /usr/share/nginx/htmlvolumes:- name: nfs-pvcpersistentVolumeClaim:claimName: nfs-pvc
---
apiVersion: v1
kind: Service
metadata:name: nginx-app-svc
spec:ports:- protocol: TCPport: 80targetPort: 80selector:app: nginx
---
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: nginx-app-ingress
spec:rules:- host: www.test1.comhttp:paths:- path: /pathType: Prefix
#根据前缀进行匹配 / www.test1.com/ www.test1.com/ www.test1.com /www/www1/www2backend:service:name: nginx-app-svcport:number: 80给node节点设置标签
kubectl label nodes node02 test1=true给node02节点做映射
20.0.0.70 master01
20.0.0.71 node01
20.0.0.72 node02 www.test1.com

3、deployment+NodePort
主要通过nginx-ingress-controller
host-ingress的配置找到pod----controller---请求发到pod
NodePort---controller---ingress----service---pod
NodePort暴漏端口的方式是最简单的方法,NodePort多了一层nat(地址转换),并发量大的对性能会有一定影响,内部都会用NodePort修改配置文件生成service-nodePort的yaml文件
wget https://gitee.com/mirrors/ingress-nginx/raw/nginx-0.30.0/deploy/static/provider/baremetal/service-nodeport.yaml用最原始的生成的mandatory.yaml修改service的标签
apiVersion: v1
kind: PersistentVolumeClaim
metadata:name: nfs-pvc1
spec:accessModes:- ReadWriteManystorageClassName: nfs-client-storageclassresources:requests:storage: 2Gi
---
apiVersion: apps/v1
kind: Deployment
metadata:name: nginx-app1labels:app: nginx2
spec:replicas: 3selector:matchLabels:app: nginx2template:metadata:labels:app: nginx2spec:containers:- name: nginximage: nginx:1.22volumeMounts:- name: nfs-pvcmountPath: /usr/share/nginx/htmlvolumes:- name: nfs-pvcpersistentVolumeClaim:claimName: nfs-pvc1
---
apiVersion: v1
kind: Service
metadata:name: nginx-app-svc1
spec:ports:- protocol: TCPport: 80targetPort: 80selector:app: nginx2
---
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: nginx-app-ingress
spec:rules:- host: www.test2.comhttp:paths:- path: /pathType: Prefix
#根据前缀进行匹配 / www.test1.com/ www.test1.com/ www.test1.com /www/www1/www2backend:service:name: nginx-app-svc1port:number: 80生成的service-nodeport.yaml
apiVersion: v1
kind: Service
metadata:name: ingress-nginxnamespace: ingress-nginxlabels:app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/part-of: ingress-nginx
spec:type: NodePortports:- name: httpport: 80targetPort: 80protocol: TCP- name: httpsport: 443targetPort: 443protocol: TCPselector:app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/part-of: ingress-nginx
#现在执行这个yaml文件,会生成一个service,在ingress-nginx这个命名空间生成一个service,所有的controller的请求都会
#从这个定义的service的nodeport的端口,把请求转发到自定义的service的pod做映射
127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4
::1 localhost localhost.localdomain localhost6 localhost6.localdomain6
20.0.0.70 master01
20.0.0.71 node01 www.test2.com
20.0.0.72 node02 www.test1.com虚拟主机的方式实现http代理
ingress的方式实现:一个ingress可以访问不同的主机
pod1apiVersion: apps/v1
kind: Deployment
metadata:name: deployment1labels:test: nginx1
spec:replicas: 1selector:matchLabels:test: nginx1template:metadata:labels:test: nginx1spec:containers:- name: nginx1image: nginx:1.22
---
apiVersion: v1
kind: Service
metadata:name: svc-1
spec:ports:- port: 80targetPort: 80protocol: TCPselector:test: nginx1pod2apiVersion: apps/v1
kind: Deployment
metadata:name: deployment2labels:test: nginx2
spec:replicas: 1selector:matchLabels:test: nginx2template:metadata:labels:test: nginx2spec:containers:- name: nginx2image: nginx:1.22
---
apiVersion: v1
kind: Service
metadata:name: svc-2
spec:ports:- port: 80targetPort: 80protocol: TCPselector:test: nginx2pod-ingressapiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: ingress1
spec:rules:- host: www1.test.comhttp:paths:- path: /pathType: Prefixbackend:service:name: svc-1port:number: 80
---
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: ingress2
spec:rules:- host: www2.test.comhttp:paths:- path: /pathType: Prefixbackend:service:name: svc-2port:number: 80做映射
127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4
::1 localhost localhost.localdomain localhost6 localhost6.localdomain6
20.0.0.70 master01
20.0.0.71 node01 www2.test.com
20.0.0.72 node02 www1.test.com查看对外访问的端口(service)
kubectl get svc -o wide -n ingress-nginx
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE SELECTOR
ingress-nginx NodePort 10.96.23.193 <none> 80:30150/TCP,443:30780/TCP 42m app.kubernetes.io/name=ingress-nginx,app.kubernetes.io/part-of=ingress-nginxingress实现https代理访问
openssl req -x509 -sha256 -nodes -days 365 -newkey ras:2048 -keyout tls.key -out tls.crt -subj "/CN=nginxsvc/O=nginxsvc
req 生成证书文件的请求
x509 生成x509自签名的证书
-sha256 表示使用sha-256的散列算法
-nodes 表示生成的密钥不加密
-days 365 证书有效期是365
-newkey rsa:2048 RSA的密钥对创建tls
kubectl create secret tls tls-secret --key tls.key --cert tls.crtmkdir httpsapiVersion: apps/v1
kind: Deployment
metadata:name: nginx-httpslabels:app: https
spec:replicas: 3selector:matchLabels:app: httpstemplate:metadata:labels:app: httpsspec:containers:- name: nignximage: nginx:1.22
---
apiVersion: v1
kind: Service
metadata:name: nginx-svc
spec:ports:- port: 80targetPort: 80protocol: TCPselector:app: https
---
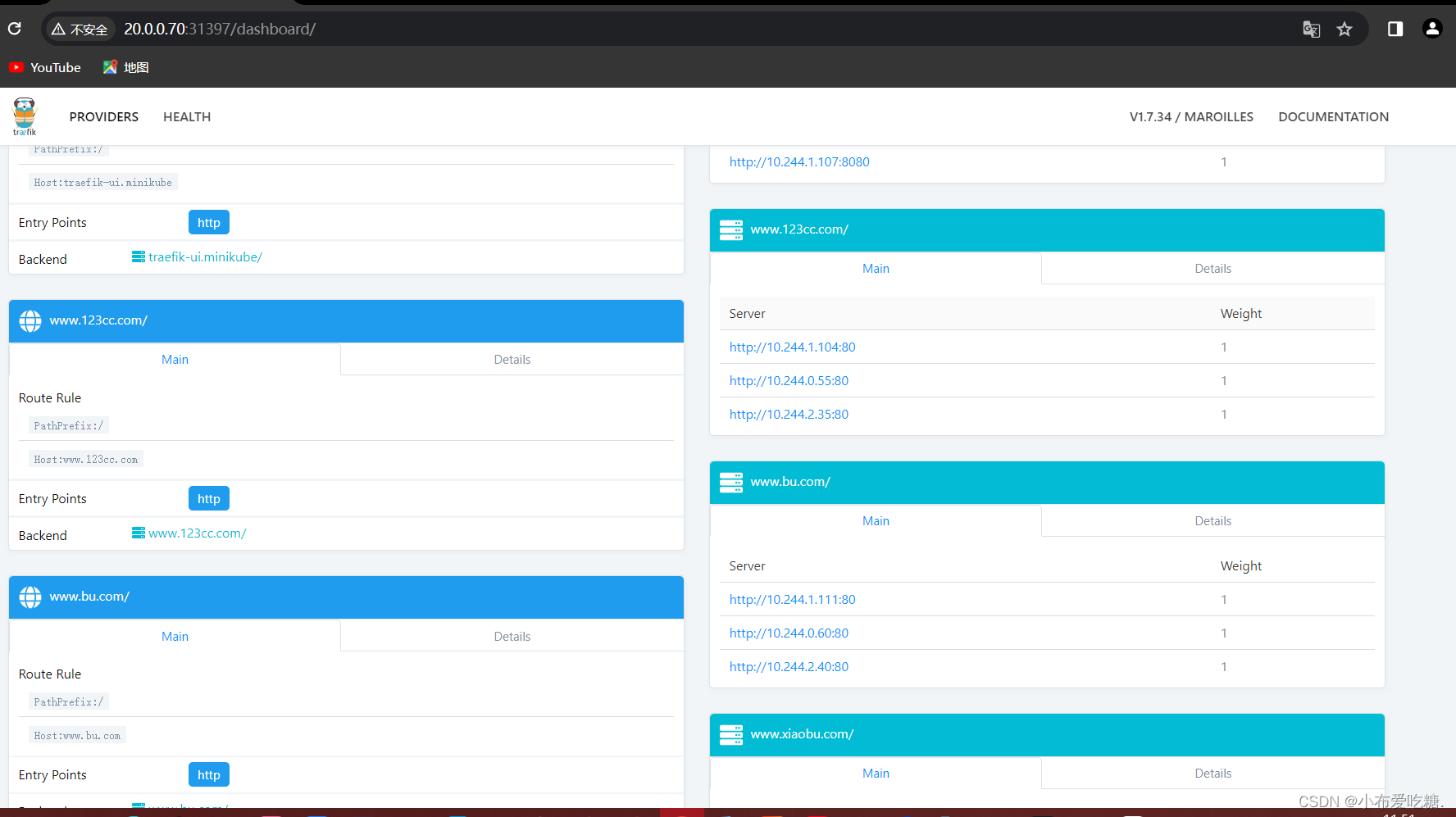
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: nignx-ingress-https
spec:tls:- hosts:- www.123cc.comsecretName: tls-secret
#加密的配置保存在ingress当中,请求--ingress-controller--ingress---转发service
#在代理进行时,就要先验证密钥对,然后再把请求转发service对应的podrules:- host: www.123cc.comhttp:paths:- path: /pathType: Prefixbackend:service:name: nginx-svcport:number: 80
做映射
www.123cc.comcurl -k https://www.123cc.com:32674nginx的登录账户认证
mkdir basic-auth
cd basic-auth/
yum -y install httpd
htpasswd -c auth xiaobu
kubectl create secret generic basic-auth --from-file=authkubectl describe secrets basic-auth
Name: basic-auth
Namespace: default
Labels: <none>
Annotations: <none>Type: OpaqueData
====
auth: 45 bytesapiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: ingress-authannotations:
#开启认证模块的配置nginx.ingress.kubernets.io/auth-type: basic
#设置认证类型为basic,这是k8s自带的认证加密的模块nginx.ingress.kubernets.io/auth-secret: basic-auth
#把认证的加密模块导入到ingress中nginx.ingress.kubernets.io/auth-realm: 'Authentication Required -xiaobu'
#设置认证窗口的提示信息
spec:rules:- host: www.xiaobu.comhttp:paths:- path: /pathType: Prefixbackend:service:name: nginx-svcport:number: 80做映射
127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4
::1 localhost localhost.localdomain localhost6 localhost6.localdomain6
20.0.0.70 master01 www.xiaobu.com
20.0.0.71 node01 www.test2.com
20.0.0.72 node02 www.test1.com www.123cc.com
20.0.0.73 hub.test.com www.test1.com www.test2.com访问
www.xiaobu.com:31328nginx的重写,nginx的重定向
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: nginx-rewriteannotations:nginx.ingress.kubernetes.io/rewrite-target: https://www.123cc.com:32674
#访问页面会跳转到指定的页面
spec:rules:- host: www.xiaokai.comhttp:paths:- path: /pathType: Prefixbackend:service:name: nginx-svcport:number: 80
访问
www.xiaokai.com:31328traefik
traefik ingress controller traefik是一个为了让部署微服务更加快捷而诞生的一个http反向代理,负载均衡
traefik设计时就能够实时的和k8s API交互,感知后端service以及pod的变化,可以自动更新配置和重载
pod内nginx 80 8081
traefik的部署方式
daemonset
特点,优点: 每个节点都会部罢一个traefik,节点感知,可以自动发现,更新容器的配置。不需要手动重载。
缺点: 资源占用,大型集群中,deamonset可能会运行多个traefik的实力,尤其是节点上不需要大量容器运行的情况下,没有办法扩缩容
部署对外集群 对外的业务会经常变更,Daemonset可以更好的,自动大发现服务配置变更
deployment:
有点:集中办公控制,可以使用少量的实例来运行处理整个集群的流量,更容易升级和维护
缺点:deployment的负载均衡不会均分到每个节点
手动更新,他无法感知容器内部配置的变化
部署对内集群 对内的相对稳定,更新和变化也比较少,适合deployment
对外标签 traffic-type: internal 对内服务
对内标签 traffic-type: external 对外服务nginx-ingress和traefik-ingress
工作原理都一样,都是7层代理,都可以动态的更新配置,都可以自动发现服务
traefik-ingress 自动更新的重载更快,更方便
traefik的并发能力只能nginx-ingress的6成 60%
生成的yaml文件
wget https://gitee.com/mirrors/traefik/raw/v1.7/examples/k8s/traefik-deployment.yaml
wget https://gitee.com/mirrors/traefik/raw/v1.7/examples/k8s/traefik-rbac.yaml
wget https://gitee.com/mirrors/traefik/raw/v1.7/examples/k8s/traefik-ds.yaml
wget https://gitee.com/mirrors/traefik/raw/v1.7/examples/k8s/ui.yaml基于deployment的apiVersion: apps/v1
kind: Deployment
metadata:name: nginx-traefiklabels:nginx: traefik
spec:replicas: 3selector:matchLabels:nginx: traefiktemplate:metadata:labels:nginx: traefikspec:containers:- name: nginximage: nginx:1.22
---
apiVersion: v1
kind: Service
metadata:name: nginx-traefik-svc1
spec:ports:- port: 80targetPort: 80protocol: TCPselector:nginx: traefik
---
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: nginx-traefik-test1
spec:rules:- host: www.bu.comhttp:paths:- path: /pathType: Prefixbackend:service:name: nginx-traefik-svc1port:number: 80


即将召开)







![[足式机器人]Part2 Dr. CAN学习笔记- Kalman Filter卡尔曼滤波器Ch05-1+2](http://pic.xiahunao.cn/[足式机器人]Part2 Dr. CAN学习笔记- Kalman Filter卡尔曼滤波器Ch05-1+2)






)

