目录
一. 前言
二. Hashcat 安装
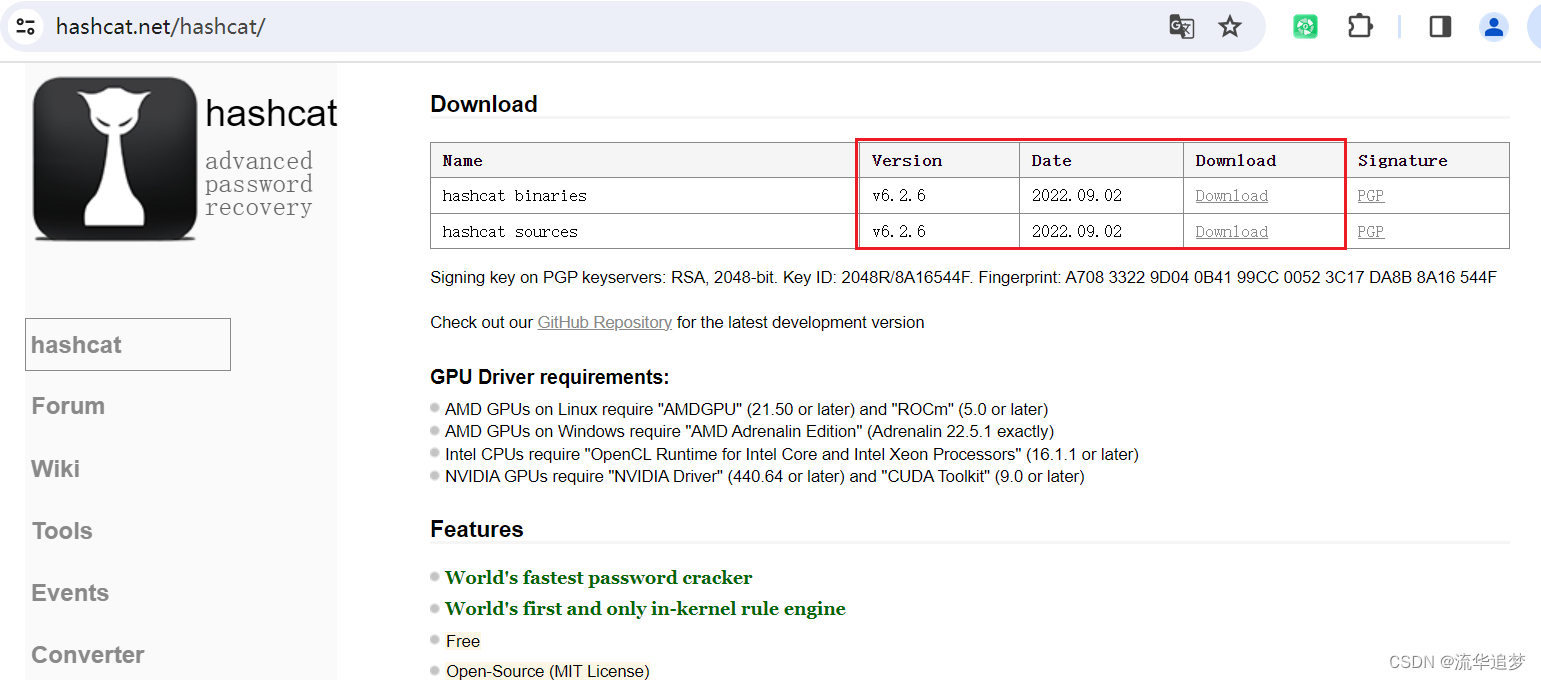
2.1. Hashcat 官网下载
2.2. hash 类型识别工具 HashIdentifier
2.3. John The Ripper
三. Hashcat 全部参数
3.1. Hashcat 的攻击模式(-a 参数)
3.2. 输出格式(--outfile-format 参数)
3.3. 内置掩码字符集
3.4. Hash 类型对照表(-m 参数)
3.5. 工作负载配置
四. Hashcat 的常见使用案例
4.1. RAR 文件解密
4.2. MD5 密文解密
4.2.1. 字典模式破解
4.2.2. 掩码模式破解
4.2.3. 使用字典+掩码进行破解
4.2.4. 使用掩码+字典进行破解
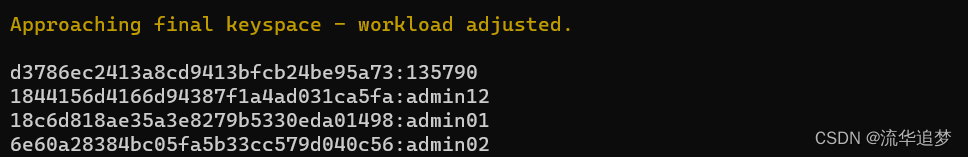
4.2.5. 批量字典破解
4.3. SHA512 密文解密
4.4. Windows 密码解密
4.5. MySql 密码解密
4.6. Office 密码解密
4.7. 在线解密
一. 前言
Hashcat 软件是一款非常强大的、开源的、号称世界上最快的密码破解软件,配合强大的字典,可以破译超过百分之九十的密码。Hashcat 目前支持各类公开算法高达240+类,市面上公开的密码加密算法基本都支持,有 Microsoft LM 哈希、MD4、MD5、SHA 系列,Unix 加密格式,MySQL 和 Cisco PIX 等!是安全测试中经常用到的密码解密神器之一。
作为新手,可以使用 Hashcat 工具 CPU 模式破解,电脑机型高端可以使用 GPU 破解。内存的大小也影响工具破解的成功率。
二. Hashcat 安装
2.1. Hashcat 官网下载
建议从官网下载最新版本的 Hashcat 压缩包:https://hashcat.net/hashcat/
解压目录如下:

该目录下的文件:
- hashcat.exe:是64位操作系统上可以使用的可执行文件。
- hashcat.potfile:是 hashcat 破解后密文、译文默认存储文件,只要解密过的 hash 密文都会被记录,后续相同密文就不需要再破解,直接从该文件中通过 --show 参数获取。
- password.dict:是密码字典文件。
在该目录下 cmd 窗口中执行命令:hashcat -h
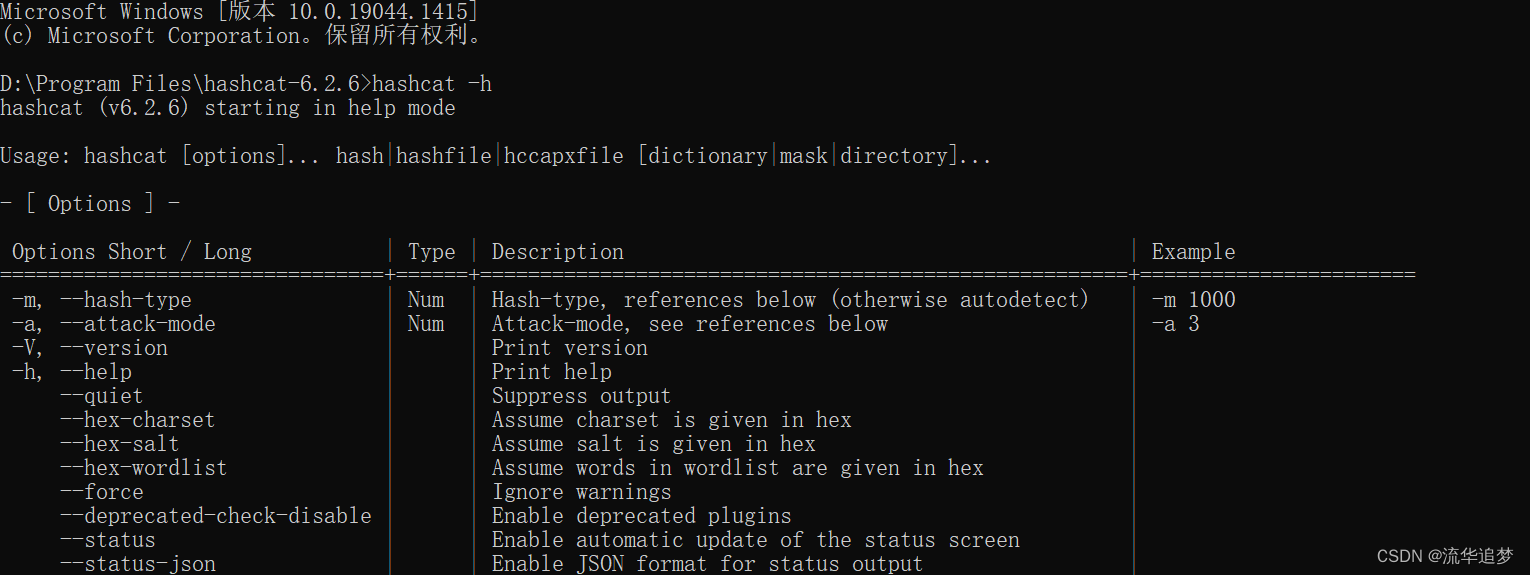
搞定,安装成功,为方便使用,可以配置该文件夹目录到系统环境变量 path 中,就可以在Windows 任何目录下执行 hashcat 命令了。
2.2. hash 类型识别工具 HashIdentifier
可以使用 HashIdentifier 识别数据的 hash 算法类型,HashIdentifier 是 python 开发的工具,需要有 python3 的基础环境,下载压缩包,解压就可以使用。

2.3. John The Ripper
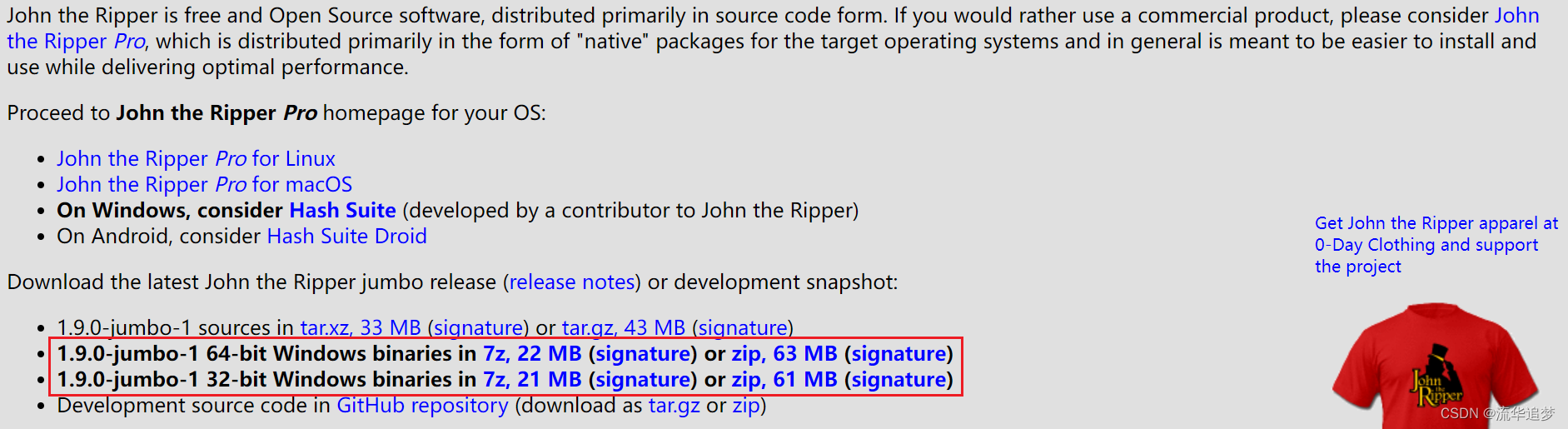
一款免费、开源的暴力密码破解器,它有多平台版本,支持目前大多数的加密算法,如 DES、MD4、MD5 等。该软件破解密码方式简单而粗暴,理论上只要时间上面允许,该软件可以破译绝大多数用户密码。John the Ripper 免费的开源软件,支持目前大多数的加密算法,如 DES、MD4、MD5 等。它支持多种不同类型的系统架构,包括 Unix、Linux、Windows、DOS 模式、BeOS 和 OpenVMS,主要目的是破解不够牢固的 Unix/Linux 系统密码。
下载地址:https://www.openwall.com/john/
三. Hashcat 全部参数
| 选项全称 | 选项简写 | 类型 | 描述 | 示例 |
|---|---|---|---|---|
| --hash-type | -m | Num | 指定要破解的hash类型,如果不指定类型,则默认是MD5 | -m 1000 |
| --attack-mode | -a | Num | 指定要使用的破解模式,其值参考后面对参数。“-a 0”字典攻击,“-a 1” 组合攻击;“-a 3”掩码攻击。 | -a 3 |
| --version | -V | 查看版本信息 | ||
| --help | -h | 查看帮助信息 | ||
| --quiet | 禁止输出 | |||
| --hex-charset | 假设字符集是用十六进制给出的 | |||
| --hex-salt | 假设salt是十六进制的 | |||
| --hex-wordlist | 假设单词表中的单词是用十六进制表示的 | |||
| --force | 忽略破解过程中的警告信息,跑单条hash可能需要加上此选项 | |||
| --deprecated-check-disable | 启用不推荐使用的插件 | |||
| --status | 启用状态屏幕的自动更新 | |||
| --status-json | 为状态输出启用JSON格式 | |||
| --status-timer | Num | 将状态屏幕更新之间的秒数设置为X | --status-timer=1 | |
| --stdin-timeout-abort | Num | 如果在X秒内没有来自stdin的输入,则中止 | --stdin-timeout-abort=300 | |
| --machine-readable | 以机器可读的格式显示状态视图 | |||
| --keep-guessing | 破解后继续猜测散列 | |||
| --self-test-disable | 启动时禁用自检功能 | |||
| --loopback | 将新plains添加到导入目录 | |||
| --markov-hcstat2 | File | 指定要使用的hcstat2文件 | --markov-hcstat2=my.hcstat2 | |
| --markov-disable | 禁用马尔可夫链,模仿经典暴力 | |||
| --markov-classic | 启用经典马尔可夫链,无每个位置 | |||
| --markov-inverse | 启用逆马尔可夫链,无每个位置 | |||
| --markov-threshold | -t | Num | 阈值X何时停止接受新的马尔可夫链 | -t 50 |
| --runtime | Num | 运行X秒后中止会话 | --runtime=10 | |
| --session | Str | 定义特定会话名称 | --session=mysession | |
| --restore | 从--session还原会话 | |||
| --restore-disable | 不写入还原文件 | |||
| --restore-file-path | File | 恢复文件的特定路径 | --restore-file-path=x.restore | |
| --outfile | -o | File | 为恢复的哈希定义输出文件 | -o outfile.txt |
| --outfile-format | Str | 要使用的完整文件格式,用逗号分隔 | --outfile-format=1,3 | |
| --outfile-autohex-disable | 禁止在输出平面中使用$HEX[] | |||
| --outfile-check-timer | Num | 将输出文件检查之间的秒数设置为X | --outfile-check-timer=30 | |
| --wordlist-autohex-disable | 禁用单词列表中$HEX[]的转换 | |||
| --separator | -p | Char | 哈希列表和输出文件的分隔符字符 | -p : |
| --stdout | 不要破解哈希,而是只打印候选者 | |||
| --show | 将hashlist与potfile进行比较;显示破解的哈希 | |||
| --left | 将hashlist与potfile进行比较;显示未破解的哈希 | |||
| --username | 启用忽略哈希文件中的用户名 | |||
| --remove | 一旦哈希被破解,就可以删除它们 | |||
| --remove-timer | Num | 每X秒更新一次输入哈希文件 | --remove-timer=30 | |
| --potfile-disable | 不写入potfile | |||
| --potfile-path | File | potfile的特定路径 | --potfile-path=my.pot | |
| --encoding-from | Code | 强制从X进行内部单词表编码 | --encoding-from=iso-8859-15 | |
| --encoding-to | Code | 强制内部单词表编码为X | --encoding-to=utf-32le | |
| --debug-mode | Num | 定义调试模式(仅通过使用规则混合) | --debug-mode=4 | |
| --debug-file | File | 调试规则的输出文件 | --debug-file=good.log | |
| --induction-dir | Dir | 指定用于环回的导入目录 | --induction=inducts | |
| --outfile-check-dir | Dir | 指定要监视plains的输出文件目录 | --outfile-check-dir=x | |
| --logfile-disable | 禁用日志文件 | |||
| --hccapx-message-pair | Num | 仅从匹配X的hccapx加载消息对 | --hccapx-message-pair=2 | |
| --nonce-error-corrections | Num | 替换AP的nonce最后字节的BF大小范围 | --nonce-error-corrections=16 | |
| --keyboard-layout-mapping | File | 特殊哈希模式的键盘布局映射表 | --keyb=german.hckmap | |
| --truecrypt-keyfiles | File | 要使用的密钥文件,用逗号分隔 | --truecrypt-keyf=x.png | |
| --veracrypt-keyfiles | File | 要使用的密钥文件,用逗号分隔 | --veracrypt-keyf=x.txt | |
| --veracrypt-pim-start | Num | VeraCrypt个人迭代乘数启动 | --veracrypt-pim-start=450 | |
| --veracrypt-pim-stop | Num | VeraCrypt个人迭代乘数停止 | --veracrypt-pim-stop=500 | |
| --benchmark | -b | 运行所选哈希模式的基准测试 | ||
| --benchmark-all | 运行所有哈希模式的基准测试(需要-b) | |||
| --speed-only | 返回预期的攻击速度,然后退出 | |||
| --progress-only | 返回理想的进度步长和处理时间 | |||
| --segment-size | -c | Num | 将wordfile中缓存的大小(MB)设置为X | -c 32 |
| --bitmap-min | Num | 将位图允许的最小位设置为X | --bitmap-min=24 | |
| --bitmap-max | Num | 将位图允许的最大位设置为X | --bitmap-max=24 | |
| --cpu-affinity | Str | 锁定CPU设备,用逗号分隔 | --cpu-affinity=1,2,3 | |
| --hook-threads | Num | 设置挂钩的线程数(每个计算单元) | --hook-threads=8 | |
| --hash-info | 显示每个哈希模式的信息 | |||
| --example-hashes | --hash-info的别名 | |||
| --backend-ignore-cuda | 启动时不要尝试打开CUDA接口 | |||
| --backend-ignore-hip | 启动时不要尝试打开HIP接口 | |||
| --backend-ignore-metal | 启动时不要尝试打开Metal接口 | |||
| --backend-ignore-opencl | 启动时不要尝试打开OpenCL接口 | |||
| --backend-info | -I | 显示系统/环境/后端API信息 | -I or -II | |
| --backend-devices | -d | Str | 要使用的后端设备,用逗号分隔 | -d 1 |
| --opencl-device-types | -D | Str | 要使用的OpenCL,用逗号分隔 | -D 1 |
| --optimized-kernel-enable | -O | 启用优化内核(限制密码长度) | ||
| --multiply-accel-disable | -M | 禁用将内核加速与处理器计数相乘 | ||
| --workload-profile | -w | Num | 启用特定的工作负载配置文件,请参阅下面的池,有4种选项 | -w 3 |
| --kernel-accel | -n | Num | 手动工作负载调整,将outerloop步长设置为X | -n 64 |
| --kernel-loops | -u | Num | 手动工作负载调整,将innerloop步长设置为X | -u 256 |
| --kernel-threads | -T | Num | 手动工作负载调整,将线程数设置为X | -T 64 |
| --backend-vector-width | Num | 手动将后端矢量宽度覆盖为X | --backend-vector=4 | |
| --spin-damp | Num | 使用CPU进行设备同步(百分比) | --spin-damp=10 | |
| --hwmon-disable | 禁用温度和风扇转速读数和触发器 | |||
| --hwmon-temp-abort | Num | 如果温度达到X摄氏度,则中止 | --hwmon-temp-abort=100 | |
| --scrypt-tmto | Num | 手动将scrypt的TMTO值重写为X | --scrypt-tmto=3 | |
| --skip | -s | Num | 从开头跳过X个单词 | -s 1000000 |
| --limit | -l | Num | 从开始限制X个单词+跳过的单词 | -l 1000000 |
| --keyspace | 显示密钥空间基础:mod值并退出 | |||
| --rule-left | -j | Rule | 单个规则应用于左侧单词列表中的每个单词 | -j 'c' |
| --rule-right | -k | Rule | 单个规则应用于右侧单词列表中的每个单词 | -k '^-' |
| --rules-file | -r | File | 使用自定义破解规则 | -r rules/best64.rule |
| --generate-rules | -g | Num | 生成X个随机规则 | -g 10000 |
| --generate-rules-func-min | Num | 强制每个规则至少X个函数 | ||
| --generate-rules-func-max | Num | 强制每个规则至多X个函数 | ||
| --generate-rules-func-sel | Str | 对随机规则引擎有效的规则运算符池 | --generate-rules-func-sel=ioTlc | |
| --generate-rules-seed | Num | 强制RNG种子设置为X | ||
| --custom-charset1 | -1 | CS | 用户定义的字符集 ?1 | -1 ?l?d?u |
| --custom-charset2 | -2 | CS | 用户定义的字符集 ?2 | -2 ?l?d?s |
| --custom-charset3 | -3 | CS | 用户定义的字符集 ?3 | |
| --custom-charset4 | -4 | CS | 用户定义的字符集 ?4 | |
| --identify | 显示所有支持的输入哈希算法 | --identify my.hash | ||
| --increment | -i | 启用掩码增量模式 | ||
| --increment-min | Num | 在X处开始掩码递增 | --increment-min=4 | |
| --increment-max | Num | 在X处停止掩码递增 | --increment-max=8 | |
| --slow-candidates | -S | 启用较慢(但高级)的候选生成器 | ||
| --brain-server | 启用大脑服务器 | |||
| --brain-server-timer | Num | 每X秒更新一次大脑服务器转储(最小值:60) | --brain-server-timer=300 | |
| --brain-client | -z | 启用大脑客户端,激活-S | ||
| --brain-client-features | Num | 定义大脑客户端功能,见下文 | --brain-client-features=3 | |
| --brain-host | Str | 大脑服务器主机(IP或域) | --brain-host=127.0.0.1 | |
| --brain-port | Port | Brain服务器端口 | --brain-port=13743 | |
| --brain-password | Str | Brain server身份验证密码 | --brain-password=123 | |
| --brain-session | Hex | 覆盖自动计算的大脑会话 | --brain-session=0x2ae611db | |
| --brain-session-whitelist | Hex | 仅允许给定的会话,用逗号分隔 | --brain-session-whitelist=0x2ae611db |
3.1. Hashcat 的攻击模式(-a 参数)
使用的格式为:-a 后跟对应的数字编号
0 | Straight(字段破解)
1 | Combination(将字典中密码进行组合,例:1,2 -> 11 22 12 21)
3 | Brute-force(掩码暴力破解)
6 | Hybrid Wordlist + Mask(字典+掩码破解)
7 | Hybrid Mask + Wordlist(掩码+字典破解)
9 | Association(关联破解)
3.2. 输出格式(--outfile-format 参数)
1 | hash[:salt]
2 | plain
3 | hex_plain
4 | crack_pos
5 | timestamp absolute
6 | timestamp relative
3.3. 内置掩码字符集
l | abcdefghijklmnopqrstuvwxyz [a-z]
u | ABCDEFGHIJKLMNOPQRSTUVWXYZ [A-Z]
d | 0123456789 [0-9]
h | 0123456789abcdef [0-9a-f]
H | 0123456789ABCDEF [0-9A-F]
s | !"#$%&'()*+,-./:;<=>?@[\]^_`{|}~
a | ?l?u?d?s
b | 0x00 - 0xff
字符集含义:
- ?l:代表小写字母
- ?u:代表大写字母
- ?d:代表数字
- ?s:代表特殊字符
- ?a:代表大小写字母、数字以及特殊字符
- ?b:0x00-0xff
掩码的使用格式:
- 八位数字密码:?d?d?d?d?d?d?d?d
- 八位未知密码:?a?a?a?a?a?a?a?a
- 前四位为大写字母,后面四位为数字:?u?u?u?u?d?d?d?d
- 前四位为数字或者是小写字母,后四位为大写字母或者数字:?h?h?h?h?H?H?H?H
- 前三个字符未知,中间为admin,后三位未知:?a?a?aadmin?a?a?a
- 6-8 位数字密码:--increment --increment-min 6 --increment-max 8
- 6-8 位数字+小写字母密码:--increment --increment-min 6 --increment-max 8 ?h?h?h?h?h?h?h?h
3.4. Hash 类型对照表(-m 参数)
可以通过 hashcat --help 查看。
# | Name | Category======+============================================================+======================================900 | MD4 | Raw Hash0 | MD5 | Raw Hash100 | SHA1 | Raw Hash1300 | SHA2-224 | Raw Hash1400 | SHA2-256 | Raw Hash10800 | SHA2-384 | Raw Hash1700 | SHA2-512 | Raw Hash17300 | SHA3-224 | Raw Hash17400 | SHA3-256 | Raw Hash17500 | SHA3-384 | Raw Hash17600 | SHA3-512 | Raw Hash6000 | RIPEMD-160 | Raw Hash600 | BLAKE2b-512 | Raw Hash11700 | GOST R 34.11-2012 (Streebog) 256-bit, big-endian | Raw Hash11800 | GOST R 34.11-2012 (Streebog) 512-bit, big-endian | Raw Hash6900 | GOST R 34.11-94 | Raw Hash17010 | GPG (AES-128/AES-256 (SHA-1($pass))) | Raw Hash5100 | Half MD5 | Raw Hash17700 | Keccak-224 | Raw Hash17800 | Keccak-256 | Raw Hash17900 | Keccak-384 | Raw Hash18000 | Keccak-512 | Raw Hash6100 | Whirlpool | Raw Hash10100 | SipHash | Raw Hash70 | md5(utf16le($pass)) | Raw Hash170 | sha1(utf16le($pass)) | Raw Hash1470 | sha256(utf16le($pass)) | Raw Hash10870 | sha384(utf16le($pass)) | Raw Hash1770 | sha512(utf16le($pass)) | Raw Hash610 | BLAKE2b-512($pass.$salt) | Raw Hash salted and/or iterated620 | BLAKE2b-512($salt.$pass) | Raw Hash salted and/or iterated10 | md5($pass.$salt) | Raw Hash salted and/or iterated20 | md5($salt.$pass) | Raw Hash salted and/or iterated3800 | md5($salt.$pass.$salt) | Raw Hash salted and/or iterated3710 | md5($salt.md5($pass)) | Raw Hash salted and/or iterated4110 | md5($salt.md5($pass.$salt)) | Raw Hash salted and/or iterated4010 | md5($salt.md5($salt.$pass)) | Raw Hash salted and/or iterated21300 | md5($salt.sha1($salt.$pass)) | Raw Hash salted and/or iterated40 | md5($salt.utf16le($pass)) | Raw Hash salted and/or iterated2600 | md5(md5($pass)) | Raw Hash salted and/or iterated3910 | md5(md5($pass).md5($salt)) | Raw Hash salted and/or iterated3500 | md5(md5(md5($pass))) | Raw Hash salted and/or iterated4400 | md5(sha1($pass)) | Raw Hash salted and/or iterated4410 | md5(sha1($pass).$salt) | Raw Hash salted and/or iterated20900 | md5(sha1($pass).md5($pass).sha1($pass)) | Raw Hash salted and/or iterated21200 | md5(sha1($salt).md5($pass)) | Raw Hash salted and/or iterated4300 | md5(strtoupper(md5($pass))) | Raw Hash salted and/or iterated30 | md5(utf16le($pass).$salt) | Raw Hash salted and/or iterated110 | sha1($pass.$salt) | Raw Hash salted and/or iterated120 | sha1($salt.$pass) | Raw Hash salted and/or iterated4900 | sha1($salt.$pass.$salt) | Raw Hash salted and/or iterated4520 | sha1($salt.sha1($pass)) | Raw Hash salted and/or iterated24300 | sha1($salt.sha1($pass.$salt)) | Raw Hash salted and/or iterated140 | sha1($salt.utf16le($pass)) | Raw Hash salted and/or iterated19300 | sha1($salt1.$pass.$salt2) | Raw Hash salted and/or iterated14400 | sha1(CX) | Raw Hash salted and/or iterated4700 | sha1(md5($pass)) | Raw Hash salted and/or iterated4710 | sha1(md5($pass).$salt) | Raw Hash salted and/or iterated21100 | sha1(md5($pass.$salt)) | Raw Hash salted and/or iterated18500 | sha1(md5(md5($pass))) | Raw Hash salted and/or iterated4500 | sha1(sha1($pass)) | Raw Hash salted and/or iterated4510 | sha1(sha1($pass).$salt) | Raw Hash salted and/or iterated5000 | sha1(sha1($salt.$pass.$salt)) | Raw Hash salted and/or iterated130 | sha1(utf16le($pass).$salt) | Raw Hash salted and/or iterated1410 | sha256($pass.$salt) | Raw Hash salted and/or iterated1420 | sha256($salt.$pass) | Raw Hash salted and/or iterated22300 | sha256($salt.$pass.$salt) | Raw Hash salted and/or iterated20720 | sha256($salt.sha256($pass)) | Raw Hash salted and/or iterated21420 | sha256($salt.sha256_bin($pass)) | Raw Hash salted and/or iterated1440 | sha256($salt.utf16le($pass)) | Raw Hash salted and/or iterated20800 | sha256(md5($pass)) | Raw Hash salted and/or iterated20710 | sha256(sha256($pass).$salt) | Raw Hash salted and/or iterated21400 | sha256(sha256_bin($pass)) | Raw Hash salted and/or iterated1430 | sha256(utf16le($pass).$salt) | Raw Hash salted and/or iterated10810 | sha384($pass.$salt) | Raw Hash salted and/or iterated10820 | sha384($salt.$pass) | Raw Hash salted and/or iterated10840 | sha384($salt.utf16le($pass)) | Raw Hash salted and/or iterated10830 | sha384(utf16le($pass).$salt) | Raw Hash salted and/or iterated1710 | sha512($pass.$salt) | Raw Hash salted and/or iterated1720 | sha512($salt.$pass) | Raw Hash salted and/or iterated1740 | sha512($salt.utf16le($pass)) | Raw Hash salted and/or iterated1730 | sha512(utf16le($pass).$salt) | Raw Hash salted and/or iterated50 | HMAC-MD5 (key = $pass) | Raw Hash authenticated60 | HMAC-MD5 (key = $salt) | Raw Hash authenticated150 | HMAC-SHA1 (key = $pass) | Raw Hash authenticated160 | HMAC-SHA1 (key = $salt) | Raw Hash authenticated1450 | HMAC-SHA256 (key = $pass) | Raw Hash authenticated1460 | HMAC-SHA256 (key = $salt) | Raw Hash authenticated1750 | HMAC-SHA512 (key = $pass) | Raw Hash authenticated1760 | HMAC-SHA512 (key = $salt) | Raw Hash authenticated11750 | HMAC-Streebog-256 (key = $pass), big-endian | Raw Hash authenticated11760 | HMAC-Streebog-256 (key = $salt), big-endian | Raw Hash authenticated11850 | HMAC-Streebog-512 (key = $pass), big-endian | Raw Hash authenticated11860 | HMAC-Streebog-512 (key = $salt), big-endian | Raw Hash authenticated28700 | Amazon AWS4-HMAC-SHA256 | Raw Hash authenticated11500 | CRC32 | Raw Checksum27900 | CRC32C | Raw Checksum28000 | CRC64Jones | Raw Checksum18700 | Java Object hashCode() | Raw Checksum25700 | MurmurHash | Raw Checksum27800 | MurmurHash3 | Raw Checksum14100 | 3DES (PT = $salt, key = $pass) | Raw Cipher, Known-plaintext attack14000 | DES (PT = $salt, key = $pass) | Raw Cipher, Known-plaintext attack26401 | AES-128-ECB NOKDF (PT = $salt, key = $pass) | Raw Cipher, Known-plaintext attack26402 | AES-192-ECB NOKDF (PT = $salt, key = $pass) | Raw Cipher, Known-plaintext attack26403 | AES-256-ECB NOKDF (PT = $salt, key = $pass) | Raw Cipher, Known-plaintext attack15400 | ChaCha20 | Raw Cipher, Known-plaintext attack14500 | Linux Kernel Crypto API (2.4) | Raw Cipher, Known-plaintext attack14900 | Skip32 (PT = $salt, key = $pass) | Raw Cipher, Known-plaintext attack11900 | PBKDF2-HMAC-MD5 | Generic KDF12000 | PBKDF2-HMAC-SHA1 | Generic KDF10900 | PBKDF2-HMAC-SHA256 | Generic KDF12100 | PBKDF2-HMAC-SHA512 | Generic KDF8900 | scrypt | Generic KDF400 | phpass | Generic KDF16100 | TACACS+ | Network Protocol11400 | SIP digest authentication (MD5) | Network Protocol5300 | IKE-PSK MD5 | Network Protocol5400 | IKE-PSK SHA1 | Network Protocol25100 | SNMPv3 HMAC-MD5-96 | Network Protocol25000 | SNMPv3 HMAC-MD5-96/HMAC-SHA1-96 | Network Protocol25200 | SNMPv3 HMAC-SHA1-96 | Network Protocol26700 | SNMPv3 HMAC-SHA224-128 | Network Protocol26800 | SNMPv3 HMAC-SHA256-192 | Network Protocol26900 | SNMPv3 HMAC-SHA384-256 | Network Protocol27300 | SNMPv3 HMAC-SHA512-384 | Network Protocol2500 | WPA-EAPOL-PBKDF2 | Network Protocol2501 | WPA-EAPOL-PMK | Network Protocol22000 | WPA-PBKDF2-PMKID+EAPOL | Network Protocol22001 | WPA-PMK-PMKID+EAPOL | Network Protocol16800 | WPA-PMKID-PBKDF2 | Network Protocol16801 | WPA-PMKID-PMK | Network Protocol7300 | IPMI2 RAKP HMAC-SHA1 | Network Protocol10200 | CRAM-MD5 | Network Protocol16500 | JWT (JSON Web Token) | Network Protocol29200 | Radmin3 | Network Protocol19600 | Kerberos 5, etype 17, TGS-REP | Network Protocol19800 | Kerberos 5, etype 17, Pre-Auth | Network Protocol28800 | Kerberos 5, etype 17, DB | Network Protocol19700 | Kerberos 5, etype 18, TGS-REP | Network Protocol19900 | Kerberos 5, etype 18, Pre-Auth | Network Protocol28900 | Kerberos 5, etype 18, DB | Network Protocol7500 | Kerberos 5, etype 23, AS-REQ Pre-Auth | Network Protocol13100 | Kerberos 5, etype 23, TGS-REP | Network Protocol18200 | Kerberos 5, etype 23, AS-REP | Network Protocol5500 | NetNTLMv1 / NetNTLMv1+ESS | Network Protocol27000 | NetNTLMv1 / NetNTLMv1+ESS (NT) | Network Protocol5600 | NetNTLMv2 | Network Protocol27100 | NetNTLMv2 (NT) | Network Protocol29100 | Flask Session Cookie ($salt.$salt.$pass) | Network Protocol4800 | iSCSI CHAP authentication, MD5(CHAP) | Network Protocol8500 | RACF | Operating System6300 | AIX {smd5} | Operating System6700 | AIX {ssha1} | Operating System6400 | AIX {ssha256} | Operating System6500 | AIX {ssha512} | Operating System3000 | LM | Operating System19000 | QNX /etc/shadow (MD5) | Operating System19100 | QNX /etc/shadow (SHA256) | Operating System19200 | QNX /etc/shadow (SHA512) | Operating System15300 | DPAPI masterkey file v1 (context 1 and 2) | Operating System15310 | DPAPI masterkey file v1 (context 3) | Operating System15900 | DPAPI masterkey file v2 (context 1 and 2) | Operating System15910 | DPAPI masterkey file v2 (context 3) | Operating System7200 | GRUB 2 | Operating System12800 | MS-AzureSync PBKDF2-HMAC-SHA256 | Operating System12400 | BSDi Crypt, Extended DES | Operating System1000 | NTLM | Operating System9900 | Radmin2 | Operating System5800 | Samsung Android Password/PIN | Operating System28100 | Windows Hello PIN/Password | Operating System13800 | Windows Phone 8+ PIN/password | Operating System2410 | Cisco-ASA MD5 | Operating System9200 | Cisco-IOS $8$ (PBKDF2-SHA256) | Operating System9300 | Cisco-IOS $9$ (scrypt) | Operating System5700 | Cisco-IOS type 4 (SHA256) | Operating System2400 | Cisco-PIX MD5 | Operating System8100 | Citrix NetScaler (SHA1) | Operating System22200 | Citrix NetScaler (SHA512) | Operating System1100 | Domain Cached Credentials (DCC), MS Cache | Operating System2100 | Domain Cached Credentials 2 (DCC2), MS Cache 2 | Operating System7000 | FortiGate (FortiOS) | Operating System26300 | FortiGate256 (FortiOS256) | Operating System125 | ArubaOS | Operating System501 | Juniper IVE | Operating System22 | Juniper NetScreen/SSG (ScreenOS) | Operating System15100 | Juniper/NetBSD sha1crypt | Operating System26500 | iPhone passcode (UID key + System Keybag) | Operating System122 | macOS v10.4, macOS v10.5, macOS v10.6 | Operating System1722 | macOS v10.7 | Operating System7100 | macOS v10.8+ (PBKDF2-SHA512) | Operating System3200 | bcrypt $2*$, Blowfish (Unix) | Operating System500 | md5crypt, MD5 (Unix), Cisco-IOS $1$ (MD5) | Operating System1500 | descrypt, DES (Unix), Traditional DES | Operating System29000 | sha1($salt.sha1(utf16le($username).':'.utf16le($pass))) | Operating System7400 | sha256crypt $5$, SHA256 (Unix) | Operating System1800 | sha512crypt $6$, SHA512 (Unix) | Operating System24600 | SQLCipher | Database Server131 | MSSQL (2000) | Database Server132 | MSSQL (2005) | Database Server1731 | MSSQL (2012, 2014) | Database Server24100 | MongoDB ServerKey SCRAM-SHA-1 | Database Server24200 | MongoDB ServerKey SCRAM-SHA-256 | Database Server12 | PostgreSQL | Database Server11100 | PostgreSQL CRAM (MD5) | Database Server28600 | PostgreSQL SCRAM-SHA-256 | Database Server3100 | Oracle H: Type (Oracle 7+) | Database Server112 | Oracle S: Type (Oracle 11+) | Database Server12300 | Oracle T: Type (Oracle 12+) | Database Server7401 | MySQL $A$ (sha256crypt) | Database Server11200 | MySQL CRAM (SHA1) | Database Server200 | MySQL323 | Database Server300 | MySQL4.1/MySQL5 | Database Server8000 | Sybase ASE | Database Server8300 | DNSSEC (NSEC3) | FTP, HTTP, SMTP, LDAP Server25900 | KNX IP Secure - Device Authentication Code | FTP, HTTP, SMTP, LDAP Server16400 | CRAM-MD5 Dovecot | FTP, HTTP, SMTP, LDAP Server1411 | SSHA-256(Base64), LDAP {SSHA256} | FTP, HTTP, SMTP, LDAP Server1711 | SSHA-512(Base64), LDAP {SSHA512} | FTP, HTTP, SMTP, LDAP Server24900 | Dahua Authentication MD5 | FTP, HTTP, SMTP, LDAP Server10901 | RedHat 389-DS LDAP (PBKDF2-HMAC-SHA256) | FTP, HTTP, SMTP, LDAP Server15000 | FileZilla Server >= 0.9.55 | FTP, HTTP, SMTP, LDAP Server12600 | ColdFusion 10+ | FTP, HTTP, SMTP, LDAP Server1600 | Apache $apr1$ MD5, md5apr1, MD5 (APR) | FTP, HTTP, SMTP, LDAP Server141 | Episerver 6.x < .NET 4 | FTP, HTTP, SMTP, LDAP Server1441 | Episerver 6.x >= .NET 4 | FTP, HTTP, SMTP, LDAP Server1421 | hMailServer | FTP, HTTP, SMTP, LDAP Server101 | nsldap, SHA-1(Base64), Netscape LDAP SHA | FTP, HTTP, SMTP, LDAP Server111 | nsldaps, SSHA-1(Base64), Netscape LDAP SSHA | FTP, HTTP, SMTP, LDAP Server7700 | SAP CODVN B (BCODE) | Enterprise Application Software (EAS)7701 | SAP CODVN B (BCODE) from RFC_READ_TABLE | Enterprise Application Software (EAS)7800 | SAP CODVN F/G (PASSCODE) | Enterprise Application Software (EAS)7801 | SAP CODVN F/G (PASSCODE) from RFC_READ_TABLE | Enterprise Application Software (EAS)10300 | SAP CODVN H (PWDSALTEDHASH) iSSHA-1 | Enterprise Application Software (EAS)133 | PeopleSoft | Enterprise Application Software (EAS)13500 | PeopleSoft PS_TOKEN | Enterprise Application Software (EAS)21500 | SolarWinds Orion | Enterprise Application Software (EAS)21501 | SolarWinds Orion v2 | Enterprise Application Software (EAS)24 | SolarWinds Serv-U | Enterprise Application Software (EAS)8600 | Lotus Notes/Domino 5 | Enterprise Application Software (EAS)8700 | Lotus Notes/Domino 6 | Enterprise Application Software (EAS)9100 | Lotus Notes/Domino 8 | Enterprise Application Software (EAS)26200 | OpenEdge Progress Encode | Enterprise Application Software (EAS)20600 | Oracle Transportation Management (SHA256) | Enterprise Application Software (EAS)4711 | Huawei sha1(md5($pass).$salt) | Enterprise Application Software (EAS)20711 | AuthMe sha256 | Enterprise Application Software (EAS)22400 | AES Crypt (SHA256) | Full-Disk Encryption (FDE)27400 | VMware VMX (PBKDF2-HMAC-SHA1 + AES-256-CBC) | Full-Disk Encryption (FDE)14600 | LUKS v1 (legacy) | Full-Disk Encryption (FDE)29541 | LUKS v1 RIPEMD-160 + AES | Full-Disk Encryption (FDE)29542 | LUKS v1 RIPEMD-160 + Serpent | Full-Disk Encryption (FDE)29543 | LUKS v1 RIPEMD-160 + Twofish | Full-Disk Encryption (FDE)29511 | LUKS v1 SHA-1 + AES | Full-Disk Encryption (FDE)29512 | LUKS v1 SHA-1 + Serpent | Full-Disk Encryption (FDE)29513 | LUKS v1 SHA-1 + Twofish | Full-Disk Encryption (FDE)29521 | LUKS v1 SHA-256 + AES | Full-Disk Encryption (FDE)29522 | LUKS v1 SHA-256 + Serpent | Full-Disk Encryption (FDE)29523 | LUKS v1 SHA-256 + Twofish | Full-Disk Encryption (FDE)29531 | LUKS v1 SHA-512 + AES | Full-Disk Encryption (FDE)29532 | LUKS v1 SHA-512 + Serpent | Full-Disk Encryption (FDE)29533 | LUKS v1 SHA-512 + Twofish | Full-Disk Encryption (FDE)13711 | VeraCrypt RIPEMD160 + XTS 512 bit (legacy) | Full-Disk Encryption (FDE)13712 | VeraCrypt RIPEMD160 + XTS 1024 bit (legacy) | Full-Disk Encryption (FDE)13713 | VeraCrypt RIPEMD160 + XTS 1536 bit (legacy) | Full-Disk Encryption (FDE)13741 | VeraCrypt RIPEMD160 + XTS 512 bit + boot-mode (legacy) | Full-Disk Encryption (FDE)13742 | VeraCrypt RIPEMD160 + XTS 1024 bit + boot-mode (legacy) | Full-Disk Encryption (FDE)13743 | VeraCrypt RIPEMD160 + XTS 1536 bit + boot-mode (legacy) | Full-Disk Encryption (FDE)29411 | VeraCrypt RIPEMD160 + XTS 512 bit | Full-Disk Encryption (FDE)29412 | VeraCrypt RIPEMD160 + XTS 1024 bit | Full-Disk Encryption (FDE)29413 | VeraCrypt RIPEMD160 + XTS 1536 bit | Full-Disk Encryption (FDE)29441 | VeraCrypt RIPEMD160 + XTS 512 bit + boot-mode | Full-Disk Encryption (FDE)29442 | VeraCrypt RIPEMD160 + XTS 1024 bit + boot-mode | Full-Disk Encryption (FDE)29443 | VeraCrypt RIPEMD160 + XTS 1536 bit + boot-mode | Full-Disk Encryption (FDE)13751 | VeraCrypt SHA256 + XTS 512 bit (legacy) | Full-Disk Encryption (FDE)13752 | VeraCrypt SHA256 + XTS 1024 bit (legacy) | Full-Disk Encryption (FDE)13753 | VeraCrypt SHA256 + XTS 1536 bit (legacy) | Full-Disk Encryption (FDE)13761 | VeraCrypt SHA256 + XTS 512 bit + boot-mode (legacy) | Full-Disk Encryption (FDE)13762 | VeraCrypt SHA256 + XTS 1024 bit + boot-mode (legacy) | Full-Disk Encryption (FDE)13763 | VeraCrypt SHA256 + XTS 1536 bit + boot-mode (legacy) | Full-Disk Encryption (FDE)29451 | VeraCrypt SHA256 + XTS 512 bit | Full-Disk Encryption (FDE)29452 | VeraCrypt SHA256 + XTS 1024 bit | Full-Disk Encryption (FDE)29453 | VeraCrypt SHA256 + XTS 1536 bit | Full-Disk Encryption (FDE)29461 | VeraCrypt SHA256 + XTS 512 bit + boot-mode | Full-Disk Encryption (FDE)29462 | VeraCrypt SHA256 + XTS 1024 bit + boot-mode | Full-Disk Encryption (FDE)29463 | VeraCrypt SHA256 + XTS 1536 bit + boot-mode | Full-Disk Encryption (FDE)13721 | VeraCrypt SHA512 + XTS 512 bit (legacy) | Full-Disk Encryption (FDE)13722 | VeraCrypt SHA512 + XTS 1024 bit (legacy) | Full-Disk Encryption (FDE)13723 | VeraCrypt SHA512 + XTS 1536 bit (legacy) | Full-Disk Encryption (FDE)29421 | VeraCrypt SHA512 + XTS 512 bit | Full-Disk Encryption (FDE)29422 | VeraCrypt SHA512 + XTS 1024 bit | Full-Disk Encryption (FDE)29423 | VeraCrypt SHA512 + XTS 1536 bit | Full-Disk Encryption (FDE)13771 | VeraCrypt Streebog-512 + XTS 512 bit (legacy) | Full-Disk Encryption (FDE)13772 | VeraCrypt Streebog-512 + XTS 1024 bit (legacy) | Full-Disk Encryption (FDE)13773 | VeraCrypt Streebog-512 + XTS 1536 bit (legacy) | Full-Disk Encryption (FDE)13781 | VeraCrypt Streebog-512 + XTS 512 bit + boot-mode (legacy) | Full-Disk Encryption (FDE)13782 | VeraCrypt Streebog-512 + XTS 1024 bit + boot-mode (legacy) | Full-Disk Encryption (FDE)13783 | VeraCrypt Streebog-512 + XTS 1536 bit + boot-mode (legacy) | Full-Disk Encryption (FDE)29471 | VeraCrypt Streebog-512 + XTS 512 bit | Full-Disk Encryption (FDE)29472 | VeraCrypt Streebog-512 + XTS 1024 bit | Full-Disk Encryption (FDE)29473 | VeraCrypt Streebog-512 + XTS 1536 bit | Full-Disk Encryption (FDE)29481 | VeraCrypt Streebog-512 + XTS 512 bit + boot-mode | Full-Disk Encryption (FDE)29482 | VeraCrypt Streebog-512 + XTS 1024 bit + boot-mode | Full-Disk Encryption (FDE)29483 | VeraCrypt Streebog-512 + XTS 1536 bit + boot-mode | Full-Disk Encryption (FDE)13731 | VeraCrypt Whirlpool + XTS 512 bit (legacy) | Full-Disk Encryption (FDE)13732 | VeraCrypt Whirlpool + XTS 1024 bit (legacy) | Full-Disk Encryption (FDE)13733 | VeraCrypt Whirlpool + XTS 1536 bit (legacy) | Full-Disk Encryption (FDE)29431 | VeraCrypt Whirlpool + XTS 512 bit | Full-Disk Encryption (FDE)29432 | VeraCrypt Whirlpool + XTS 1024 bit | Full-Disk Encryption (FDE)29433 | VeraCrypt Whirlpool + XTS 1536 bit | Full-Disk Encryption (FDE)23900 | BestCrypt v3 Volume Encryption | Full-Disk Encryption (FDE)16700 | FileVault 2 | Full-Disk Encryption (FDE)27500 | VirtualBox (PBKDF2-HMAC-SHA256 & AES-128-XTS) | Full-Disk Encryption (FDE)27600 | VirtualBox (PBKDF2-HMAC-SHA256 & AES-256-XTS) | Full-Disk Encryption (FDE)20011 | DiskCryptor SHA512 + XTS 512 bit | Full-Disk Encryption (FDE)20012 | DiskCryptor SHA512 + XTS 1024 bit | Full-Disk Encryption (FDE)20013 | DiskCryptor SHA512 + XTS 1536 bit | Full-Disk Encryption (FDE)22100 | BitLocker | Full-Disk Encryption (FDE)12900 | Android FDE (Samsung DEK) | Full-Disk Encryption (FDE)8800 | Android FDE <= 4.3 | Full-Disk Encryption (FDE)18300 | Apple File System (APFS) | Full-Disk Encryption (FDE)6211 | TrueCrypt RIPEMD160 + XTS 512 bit (legacy) | Full-Disk Encryption (FDE)6212 | TrueCrypt RIPEMD160 + XTS 1024 bit (legacy) | Full-Disk Encryption (FDE)6213 | TrueCrypt RIPEMD160 + XTS 1536 bit (legacy) | Full-Disk Encryption (FDE)6241 | TrueCrypt RIPEMD160 + XTS 512 bit + boot-mode (legacy) | Full-Disk Encryption (FDE)6242 | TrueCrypt RIPEMD160 + XTS 1024 bit + boot-mode (legacy) | Full-Disk Encryption (FDE)6243 | TrueCrypt RIPEMD160 + XTS 1536 bit + boot-mode (legacy) | Full-Disk Encryption (FDE)29311 | TrueCrypt RIPEMD160 + XTS 512 bit | Full-Disk Encryption (FDE)29312 | TrueCrypt RIPEMD160 + XTS 1024 bit | Full-Disk Encryption (FDE)29313 | TrueCrypt RIPEMD160 + XTS 1536 bit | Full-Disk Encryption (FDE)29341 | TrueCrypt RIPEMD160 + XTS 512 bit + boot-mode | Full-Disk Encryption (FDE)29342 | TrueCrypt RIPEMD160 + XTS 1024 bit + boot-mode | Full-Disk Encryption (FDE)29343 | TrueCrypt RIPEMD160 + XTS 1536 bit + boot-mode | Full-Disk Encryption (FDE)6221 | TrueCrypt SHA512 + XTS 512 bit (legacy) | Full-Disk Encryption (FDE)6222 | TrueCrypt SHA512 + XTS 1024 bit (legacy) | Full-Disk Encryption (FDE)6223 | TrueCrypt SHA512 + XTS 1536 bit (legacy) | Full-Disk Encryption (FDE)29321 | TrueCrypt SHA512 + XTS 512 bit | Full-Disk Encryption (FDE)29322 | TrueCrypt SHA512 + XTS 1024 bit | Full-Disk Encryption (FDE)29323 | TrueCrypt SHA512 + XTS 1536 bit | Full-Disk Encryption (FDE)6231 | TrueCrypt Whirlpool + XTS 512 bit (legacy) | Full-Disk Encryption (FDE)6232 | TrueCrypt Whirlpool + XTS 1024 bit (legacy) | Full-Disk Encryption (FDE)6233 | TrueCrypt Whirlpool + XTS 1536 bit (legacy) | Full-Disk Encryption (FDE)29331 | TrueCrypt Whirlpool + XTS 512 bit | Full-Disk Encryption (FDE)29332 | TrueCrypt Whirlpool + XTS 1024 bit | Full-Disk Encryption (FDE)29333 | TrueCrypt Whirlpool + XTS 1536 bit | Full-Disk Encryption (FDE)12200 | eCryptfs | Full-Disk Encryption (FDE)10400 | PDF 1.1 - 1.3 (Acrobat 2 - 4) | Document10410 | PDF 1.1 - 1.3 (Acrobat 2 - 4), collider #1 | Document10420 | PDF 1.1 - 1.3 (Acrobat 2 - 4), collider #2 | Document10500 | PDF 1.4 - 1.6 (Acrobat 5 - 8) | Document25400 | PDF 1.4 - 1.6 (Acrobat 5 - 8) - user and owner pass | Document10600 | PDF 1.7 Level 3 (Acrobat 9) | Document10700 | PDF 1.7 Level 8 (Acrobat 10 - 11) | Document9400 | MS Office 2007 | Document9500 | MS Office 2010 | Document9600 | MS Office 2013 | Document25300 | MS Office 2016 - SheetProtection | Document9700 | MS Office <= 2003 $0/$1, MD5 + RC4 | Document9710 | MS Office <= 2003 $0/$1, MD5 + RC4, collider #1 | Document9720 | MS Office <= 2003 $0/$1, MD5 + RC4, collider #2 | Document9810 | MS Office <= 2003 $3, SHA1 + RC4, collider #1 | Document9820 | MS Office <= 2003 $3, SHA1 + RC4, collider #2 | Document9800 | MS Office <= 2003 $3/$4, SHA1 + RC4 | Document18400 | Open Document Format (ODF) 1.2 (SHA-256, AES) | Document18600 | Open Document Format (ODF) 1.1 (SHA-1, Blowfish) | Document16200 | Apple Secure Notes | Document23300 | Apple iWork | Document6600 | 1Password, agilekeychain | Password Manager8200 | 1Password, cloudkeychain | Password Manager9000 | Password Safe v2 | Password Manager5200 | Password Safe v3 | Password Manager6800 | LastPass + LastPass sniffed | Password Manager13400 | KeePass 1 (AES/Twofish) and KeePass 2 (AES) | Password Manager29700 | KeePass 1 (AES/Twofish) and KeePass 2 (AES) - keyfile only mode | Password Manager23400 | Bitwarden | Password Manager16900 | Ansible Vault | Password Manager26000 | Mozilla key3.db | Password Manager26100 | Mozilla key4.db | Password Manager23100 | Apple Keychain | Password Manager11600 | 7-Zip | Archive12500 | RAR3-hp | Archive23800 | RAR3-p (Compressed) | Archive23700 | RAR3-p (Uncompressed) | Archive13000 | RAR5 | Archive17220 | PKZIP (Compressed Multi-File) | Archive17200 | PKZIP (Compressed) | Archive17225 | PKZIP (Mixed Multi-File) | Archive17230 | PKZIP (Mixed Multi-File Checksum-Only) | Archive17210 | PKZIP (Uncompressed) | Archive20500 | PKZIP Master Key | Archive20510 | PKZIP Master Key (6 byte optimization) | Archive23001 | SecureZIP AES-128 | Archive23002 | SecureZIP AES-192 | Archive23003 | SecureZIP AES-256 | Archive13600 | WinZip | Archive18900 | Android Backup | Archive24700 | Stuffit5 | Archive13200 | AxCrypt 1 | Archive13300 | AxCrypt 1 in-memory SHA1 | Archive23500 | AxCrypt 2 AES-128 | Archive23600 | AxCrypt 2 AES-256 | Archive14700 | iTunes backup < 10.0 | Archive14800 | iTunes backup >= 10.0 | Archive8400 | WBB3 (Woltlab Burning Board) | Forums, CMS, E-Commerce2612 | PHPS | Forums, CMS, E-Commerce121 | SMF (Simple Machines Forum) > v1.1 | Forums, CMS, E-Commerce3711 | MediaWiki B type | Forums, CMS, E-Commerce4521 | Redmine | Forums, CMS, E-Commerce24800 | Umbraco HMAC-SHA1 | Forums, CMS, E-Commerce11 | Joomla < 2.5.18 | Forums, CMS, E-Commerce13900 | OpenCart | Forums, CMS, E-Commerce11000 | PrestaShop | Forums, CMS, E-Commerce16000 | Tripcode | Forums, CMS, E-Commerce7900 | Drupal7 | Forums, CMS, E-Commerce4522 | PunBB | Forums, CMS, E-Commerce2811 | MyBB 1.2+, IPB2+ (Invision Power Board) | Forums, CMS, E-Commerce2611 | vBulletin < v3.8.5 | Forums, CMS, E-Commerce2711 | vBulletin >= v3.8.5 | Forums, CMS, E-Commerce25600 | bcrypt(md5($pass)) / bcryptmd5 | Forums, CMS, E-Commerce25800 | bcrypt(sha1($pass)) / bcryptsha1 | Forums, CMS, E-Commerce28400 | bcrypt(sha512($pass)) / bcryptsha512 | Forums, CMS, E-Commerce21 | osCommerce, xt:Commerce | Forums, CMS, E-Commerce18100 | TOTP (HMAC-SHA1) | One-Time Password2000 | STDOUT | Plaintext99999 | Plaintext | Plaintext21600 | Web2py pbkdf2-sha512 | Framework10000 | Django (PBKDF2-SHA256) | Framework124 | Django (SHA-1) | Framework12001 | Atlassian (PBKDF2-HMAC-SHA1) | Framework19500 | Ruby on Rails Restful-Authentication | Framework27200 | Ruby on Rails Restful Auth (one round, no sitekey) | Framework30000 | Python Werkzeug MD5 (HMAC-MD5 (key = $salt)) | Framework30120 | Python Werkzeug SHA256 (HMAC-SHA256 (key = $salt)) | Framework20200 | Python passlib pbkdf2-sha512 | Framework20300 | Python passlib pbkdf2-sha256 | Framework20400 | Python passlib pbkdf2-sha1 | Framework24410 | PKCS#8 Private Keys (PBKDF2-HMAC-SHA1 + 3DES/AES) | Private Key24420 | PKCS#8 Private Keys (PBKDF2-HMAC-SHA256 + 3DES/AES) | Private Key15500 | JKS Java Key Store Private Keys (SHA1) | Private Key22911 | RSA/DSA/EC/OpenSSH Private Keys ($0$) | Private Key22921 | RSA/DSA/EC/OpenSSH Private Keys ($6$) | Private Key22931 | RSA/DSA/EC/OpenSSH Private Keys ($1, $3$) | Private Key22941 | RSA/DSA/EC/OpenSSH Private Keys ($4$) | Private Key22951 | RSA/DSA/EC/OpenSSH Private Keys ($5$) | Private Key23200 | XMPP SCRAM PBKDF2-SHA1 | Instant Messaging Service28300 | Teamspeak 3 (channel hash) | Instant Messaging Service22600 | Telegram Desktop < v2.1.14 (PBKDF2-HMAC-SHA1) | Instant Messaging Service24500 | Telegram Desktop >= v2.1.14 (PBKDF2-HMAC-SHA512) | Instant Messaging Service22301 | Telegram Mobile App Passcode (SHA256) | Instant Messaging Service23 | Skype | Instant Messaging Service29600 | Terra Station Wallet (AES256-CBC(PBKDF2($pass))) | Cryptocurrency Wallet26600 | MetaMask Wallet | Cryptocurrency Wallet21000 | BitShares v0.x - sha512(sha512_bin(pass)) | Cryptocurrency Wallet28501 | Bitcoin WIF private key (P2PKH), compressed | Cryptocurrency Wallet28502 | Bitcoin WIF private key (P2PKH), uncompressed | Cryptocurrency Wallet28503 | Bitcoin WIF private key (P2WPKH, Bech32), compressed | Cryptocurrency Wallet28504 | Bitcoin WIF private key (P2WPKH, Bech32), uncompressed | Cryptocurrency Wallet28505 | Bitcoin WIF private key (P2SH(P2WPKH)), compressed | Cryptocurrency Wallet28506 | Bitcoin WIF private key (P2SH(P2WPKH)), uncompressed | Cryptocurrency Wallet11300 | Bitcoin/Litecoin wallet.dat | Cryptocurrency Wallet16600 | Electrum Wallet (Salt-Type 1-3) | Cryptocurrency Wallet21700 | Electrum Wallet (Salt-Type 4) | Cryptocurrency Wallet21800 | Electrum Wallet (Salt-Type 5) | Cryptocurrency Wallet12700 | Blockchain, My Wallet | Cryptocurrency Wallet15200 | Blockchain, My Wallet, V2 | Cryptocurrency Wallet18800 | Blockchain, My Wallet, Second Password (SHA256) | Cryptocurrency Wallet25500 | Stargazer Stellar Wallet XLM | Cryptocurrency Wallet16300 | Ethereum Pre-Sale Wallet, PBKDF2-HMAC-SHA256 | Cryptocurrency Wallet15600 | Ethereum Wallet, PBKDF2-HMAC-SHA256 | Cryptocurrency Wallet15700 | Ethereum Wallet, SCRYPT | Cryptocurrency Wallet22500 | MultiBit Classic .key (MD5) | Cryptocurrency Wallet27700 | MultiBit Classic .wallet (scrypt) | Cryptocurrency Wallet22700 | MultiBit HD (scrypt) | Cryptocurrency Wallet28200 | Exodus Desktop Wallet (scrypt) | Cryptocurrency Wallet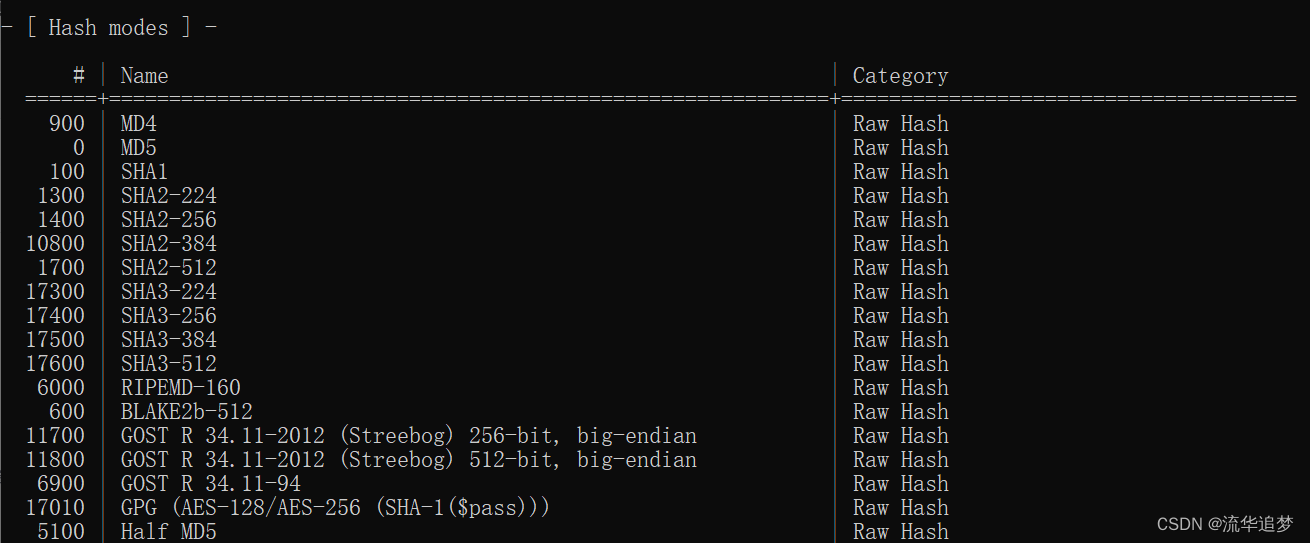
3.5. 工作负载配置
# | Performance | Runtime | Power Consumption | Desktop Impact
===+=============+=========+===================+=================1 | Low | 2 ms | Low | Minimal2 | Default | 12 ms | Economic | Noticeable3 | High | 96 ms | High | Unresponsive4 | Nightmare | 480 ms | Insane | Headless
四. Hashcat 的常见使用案例
Hashcat 支持多种平台、多种 hash 密文的破解。
4.1. RAR 文件解密
1. 通过 John The Ripper 获取文件的密文值
把要获取密文的 rar 文件拷贝到 john-1.9.0-jumbo-1-win64 的 run 目录下。
// 通过命令获取密文值
rar2john.exe Python_glxtym.rar// 获取到的密文为:
$RAR3$*1*a55d3f6aa676f7b3*9b850ef5*16*8*1*5d3dbaafa35e973c49a01dfcdcebfc4e*33
2. 通过 Hashcat 获取明文密码
hashcat.exe -m 23800 -a 3 $RAR3$*1*a55d3f6aa676f7b3*9b850ef5*16*8*1*5d3dbaafa35e973c49a01dfcdcebfc4e*33 -o password.txt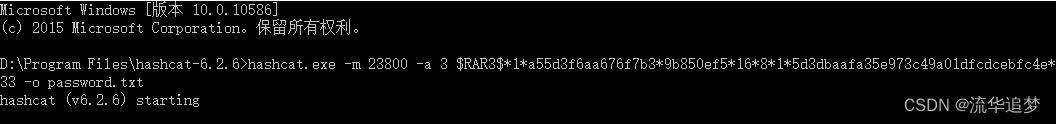
破解成功会在目录下生成 password.txt 文件。
4.2. MD5 密文解密
4.2.1. 字典模式破解
需要提前准备好字典文件 password.dict。
hashcat -m 0 -a 0 d3786ec2413a8cd9413bfcb24be95a73 password.dict --force
hashcat -m 0 -a 0 d3786ec2413a8cd9413bfcb24be95a73 password.dict --force --show
hashcat -m 0 -a 0 d3786ec2413a8cd9413bfcb24be95a73 password.dict -o result.txt –force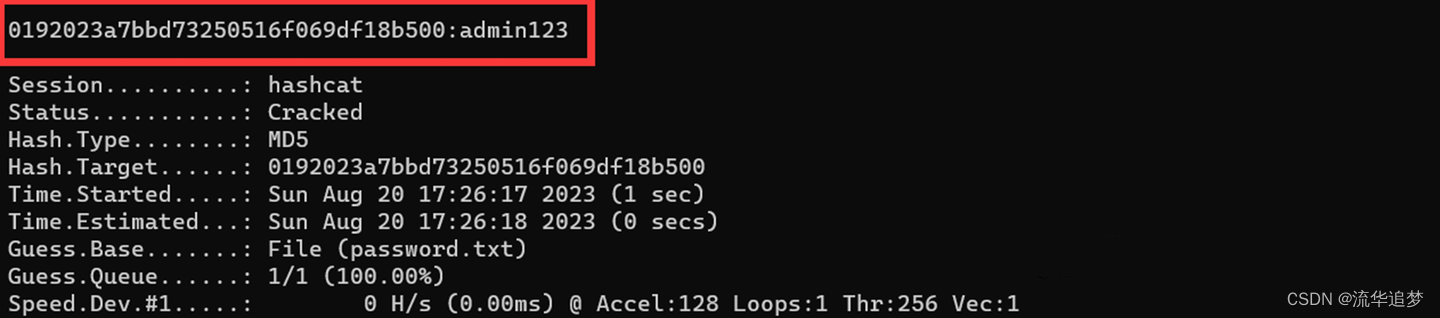
4.2.2. 掩码模式破解
hashcat -m 0 -a 3 63a9f0ea7bb98050796b649e85481845 ?l?l?l?l --force -O -w 3 -S
hashcat -m 0 -a 3 63a9f0ea7bb98050796b649e85481845 ?l?l?l?l --force -O -w 3 -S --show
hashcat -m 0 -a 3 63a9f0ea7bb98050796b649e85481845 ?l?l?l?l -o result.txt --force --show -O -w 3 -S4.2.3. 使用字典+掩码进行破解
hashcat -m 0 -a 6 1844156d4166d94387f1a4ad031ca5fa password.dict ?d?d --force -O
hashcat -m 0 -a 6 1844156d4166d94387f1a4ad031ca5fa password.dict ?d?d --force --show –O
hashcat -m 0 -a 6 1844156d4166d94387f1a4ad031ca5fa password.dict ?d?d -o result.txt --force –show –O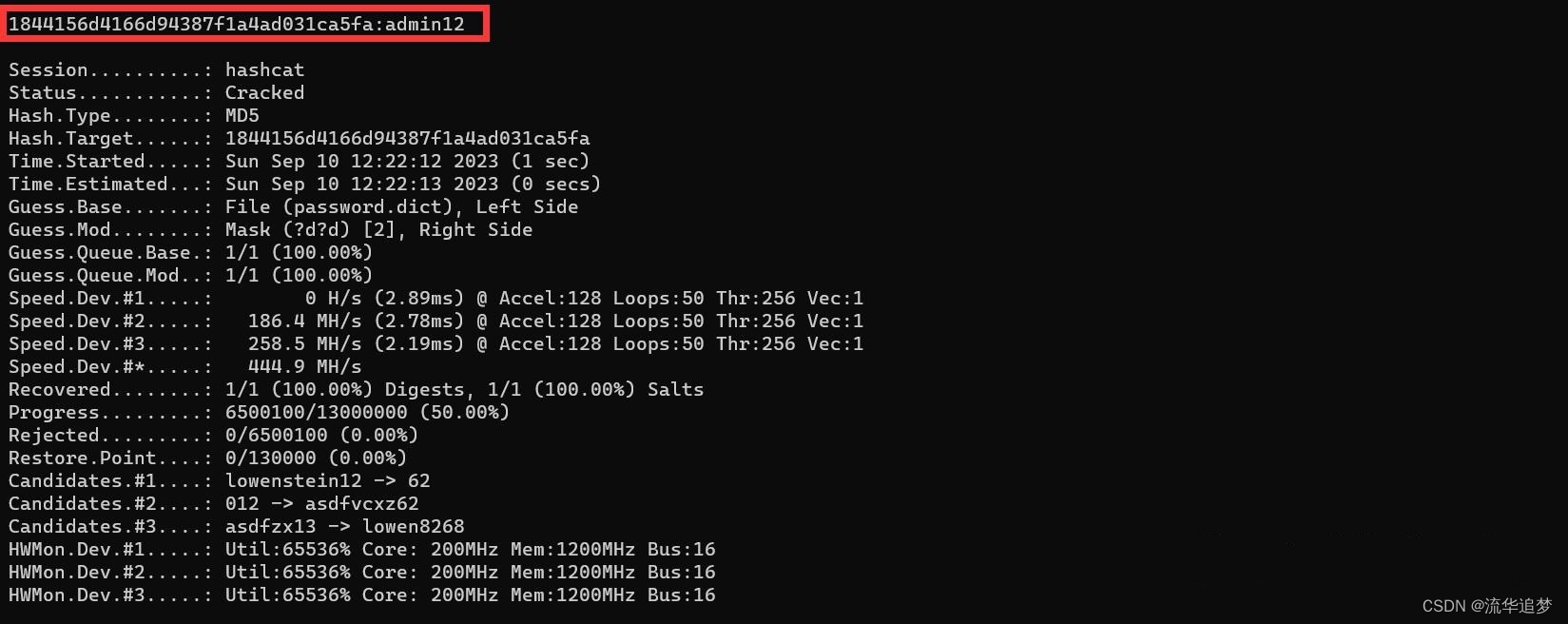
4.2.4. 使用掩码+字典进行破解
hashcat -m 0 -a 7 f8def8bcecb2e7925a2b42d60d202deb ?d?d password.dict --force -O
hashcat -m 0 -a 7 f8def8bcecb2e7925a2b42d60d202deb ?d?d password.dict --force -O --show
hashcat -m 0 -a 7 f8def8bcecb2e7925a2b42d60d202deb ?d?d password.dict -o result.txt --force –O
如果已经破解过,加参数:--show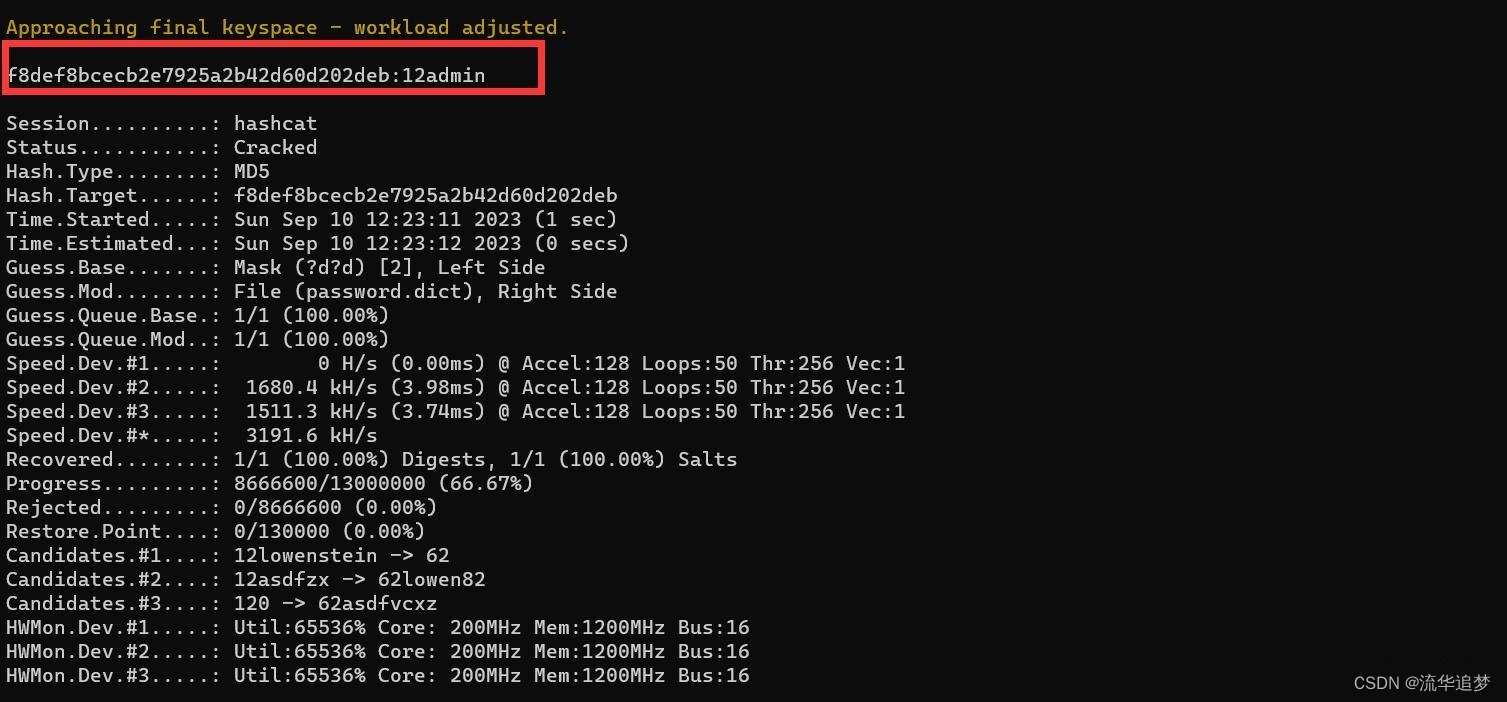
4.2.5. 批量字典破解
hashcat -m 0 -a 0 jiami.txt password.dict --force
破解后的结果文件如下:
4.3. SHA512 密文解密
密文:$6$Zje1WaoS$eH24JFr5n67149yBcDWWsfxME5cYlOXMmJxnf2uinbvYm8vWc0BmjvAoXIFY/0ZUJItRpPhHkCGDiqjXT10EV0首先使用HashIdentifier工具识别该密文的类型:
- 识别到的 hash 类型为 sha512 crypt
- 对应 hashcat 的类型编号为 1800
再使用 Hashcat 使用字典破解模式进行破解,提前准备字典文件:
hashcat -m 1800 -a 0 $6$Zje1WaoS$eH24JFr5n67149yBcDWWsfxME5cYlOXMmJxnf2uinbvYm8vWc0BmjvAoXIFY/0ZUJItRpPhHkCGDiqjXT10EV0 password.dict --force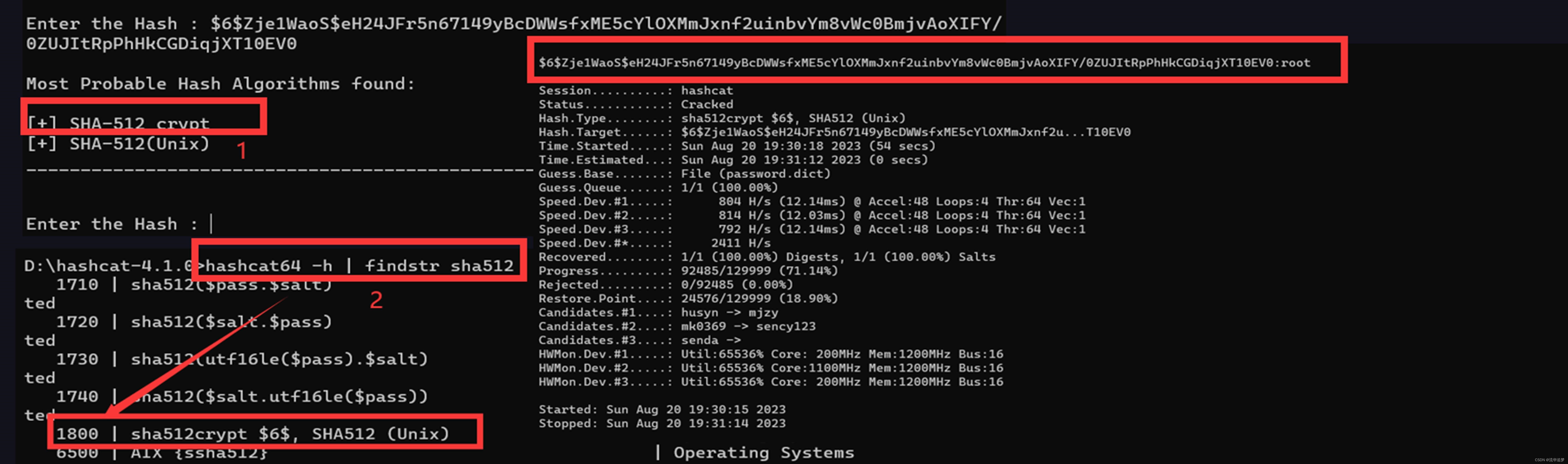
如果破解时间太长,我们可以按 s 键查看破解进度,p 键暂停,r 键继续破解,q 键退出破解。
4.4. Windows 密码解密
Windows 系统通常使用两种方法对用户的明文密码进行加密处理,分别是:
- LM Hash :对应 hashcat 中的类型编号为 3000
- ntlm hash:对应 hashcat 中的类型编号为 1000
LM Hash 是一种 Windows 系统身份认证协议,在 Windows 7 或 Windows 2008 之前的系统使用,之后的系统默认禁用了 LM Hash 协议认证,使用 ntlm hash 的方式。
对 Windows 密码进行破解建议使用高版本的 hashcat 软件,4.1.0及以下的版本会因各种问题提前终止破解而导致破解失败,本案例建议使用最新的 hashcat-6.2.6 版本。
1. root 字符串对应的 LM Hash 密文为:d480ea9533c500d4aad3b435b51404ee
hashcat -m 3000 -a 0 d480ea9533c500d4aad3b435b51404ee password.dict --force 
2. root 字符串对应的 ntlm hash 密文为:329153f560eb329c0e1deea55e88a1e9
hashcat -m 1000 -a 0 329153f560eb329c0e1deea55e88a1e9 password.dict --force -O -w 3 -S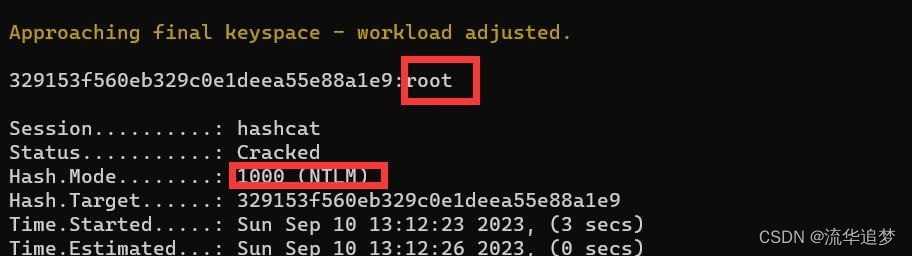
4.5. MySql 密码解密
hashcat -a 3 -m 300 --force 6BB4837EB74329105EE4568DDA7DC67ED2CA2AD9 ?d?d?d?d?d?d4.6. Office 密码解密
获取 Office 的 hash 值:python office2john.py 11.docx
结果:
11.docx:$office$*2013*100000*256*16*e4a3eb62e8d3576f861f9eded75e0525*9eeb35f0849a7800d48113440b4bbb9c*577f8d8b2e1c5f60fed76e62327b38d28f25230f6c7dfd66588d9ca8097aabb9破解密码:
hashcat -a 3 -m 9600 $office$*2013*100000*256*16*e4a3eb62e8d3576f861f9eded75e0525*9eeb35f0849a7800d48113440b4bbb9c*577f8d8b2e1c5f60fed76e62327b38d28f25230f6c7dfd66588d9ca8097aabb9 --force ?d?d?d?d?d?d4.7. 在线解密
SHA 256 在线解密:http://www.ttmd5.com/hash.php?type=09
MD5 在线解密:https://www.somd5.com/
END



















】springboot整合EasyExcel)